The Problem
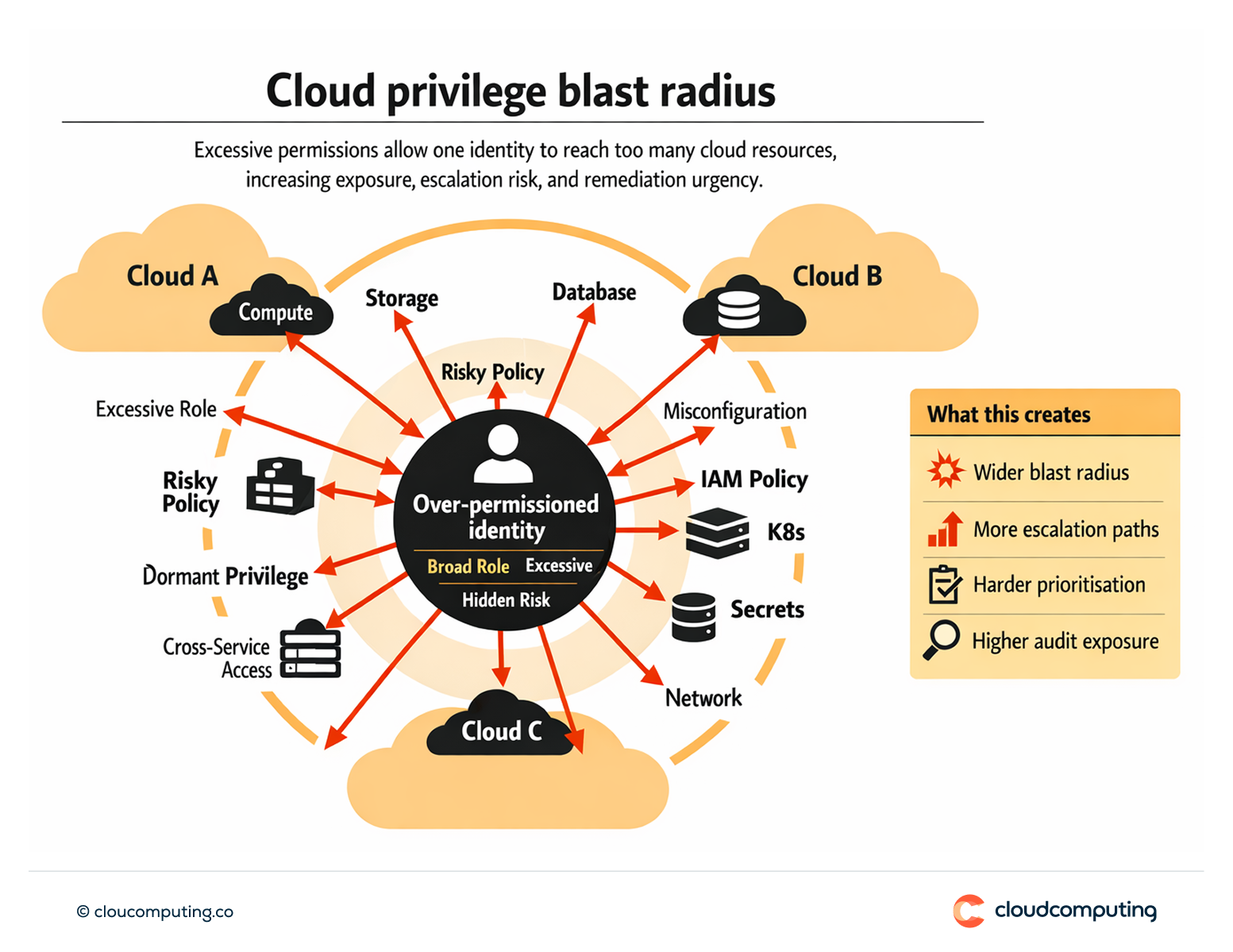
Excessive cloud permissions and misconfigurations create hidden privilege risk across multi-cloud estates.
Over-permissioned identities expand blast radius, and teams struggle to prioritise remediation.
Discovery often happens late, during audits or after incidents.
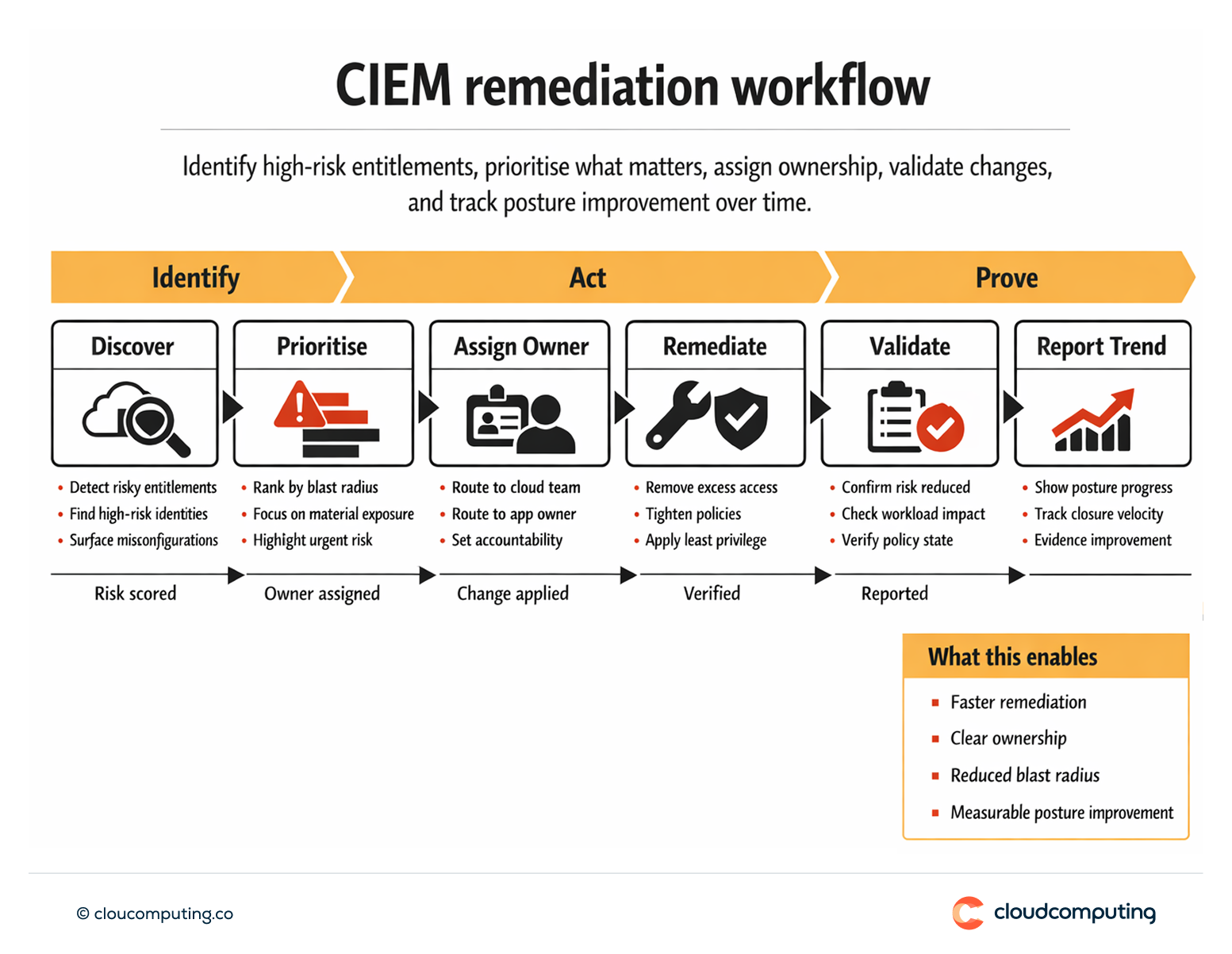
How we solve it: Deploy Delinea Privilege Control for Cloud Entitlements to identify high-risk identities, detect misconfigurations, and enforce least privilege.
We implement a risk-led approach to cloud entitlements so teams can see, prioritise, and remediate excessive access.
- Visibility and prioritisation
Identify high-risk identities and permissions that create material exposure. - Misconfiguration detection
Detect risky entitlements and configurations that increase privilege risk. - Least privilege remediation
Reduce excessive permissions with targeted changes and governance. - Trend reporting
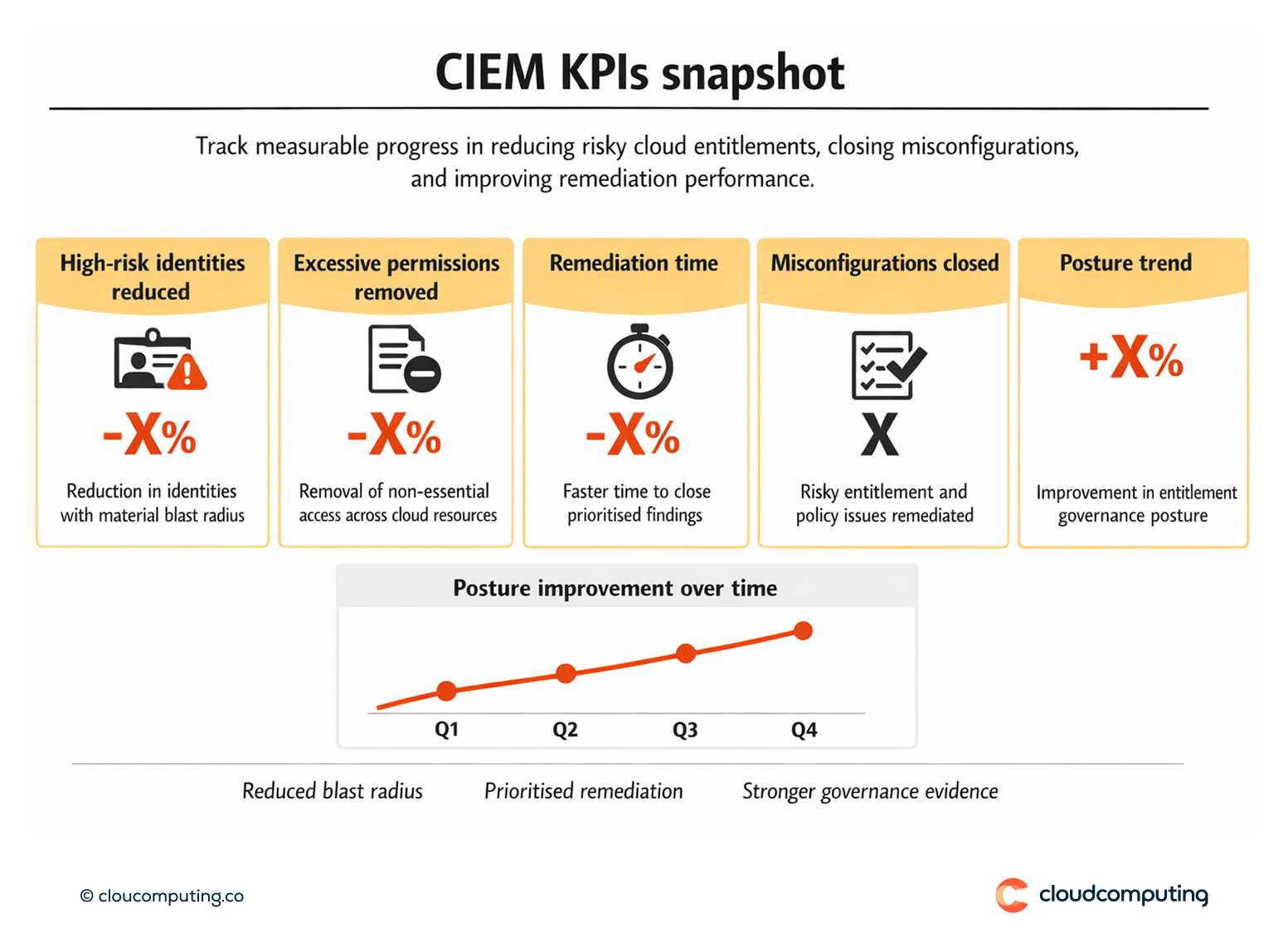
Track posture improvement and remediation velocity over time.
Expected outcome
- Fewer risky permissions through targeted least privilege remediation
- Reduced cloud blast radius by limiting over-permissioned identities
- Faster remediation with prioritised findings and clear ownership
- Improved governance posture with evidence of entitlement control
Quick Answers
What is CIEM?
Visibility and control over cloud permissions to enforce least privilege and reduce blast radius.
Why is cloud entitlement risk hard to manage?
Permissions change quickly across services, identities, and policies, creating hidden exposure.
How do you prioritise fixes?
By focusing first on identities and permissions that create the highest blast radius.