The Problem
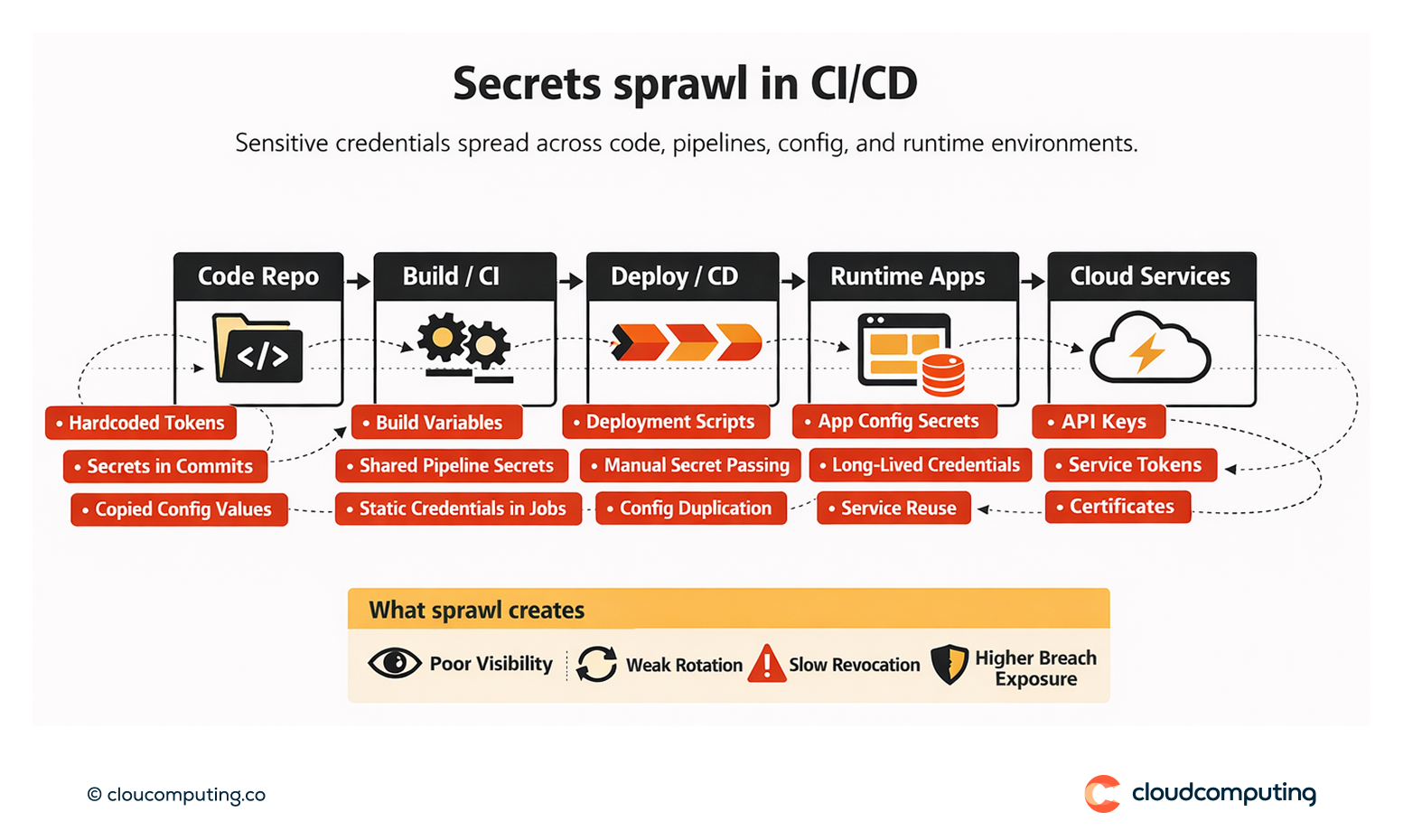
Secrets sprawl across pipelines, code, and configuration.
Tokens, keys, certificates, and passwords are hardcoded or duplicated, rarely rotated, and difficult to revoke quickly during incidents.
This increases breach likelihood and slows response.
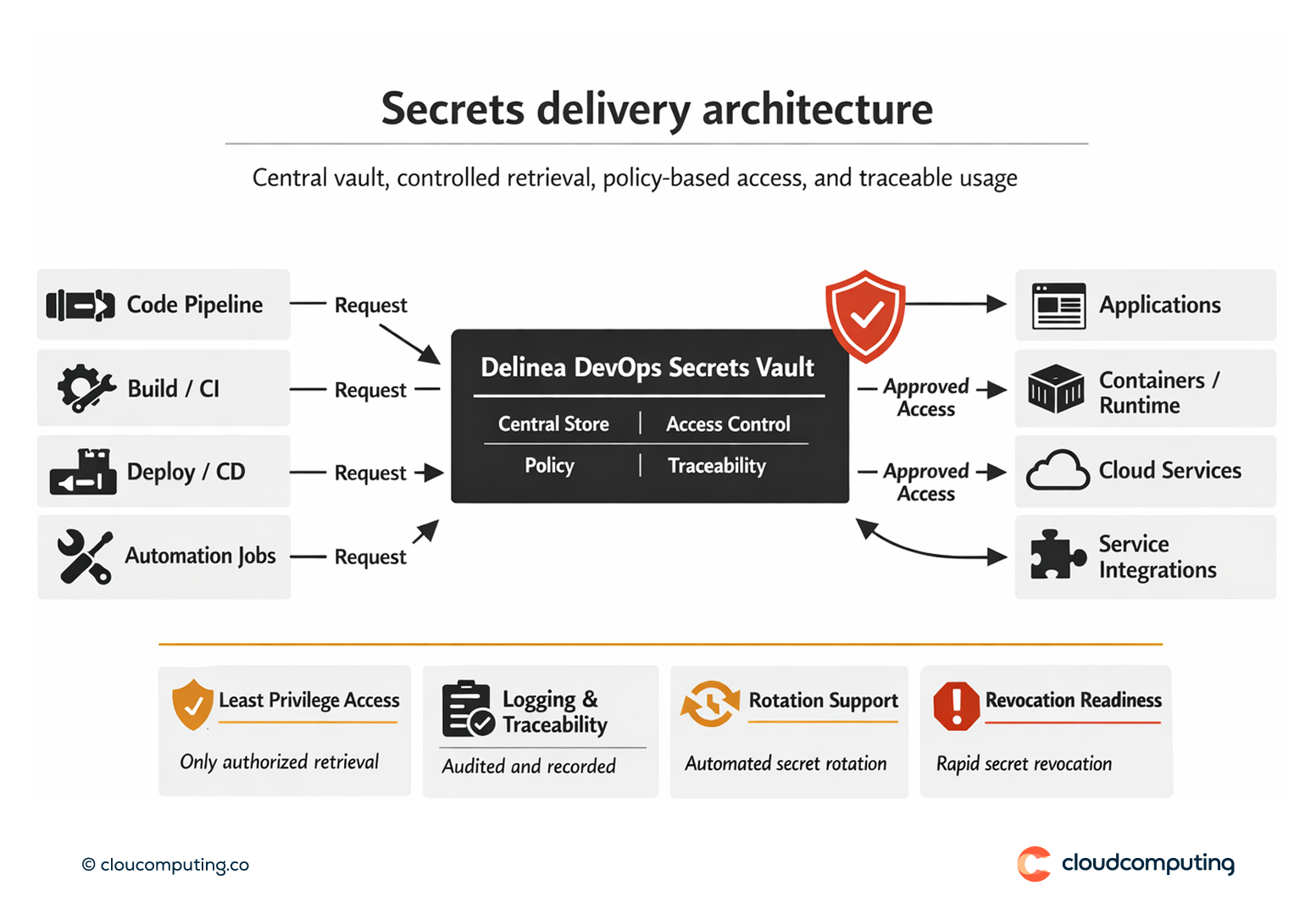
How we solve it: Roll out Delinea DevOps Secrets Vault to centrally manage secrets with usable access controls and rotation practices.
We implement a central secrets model that supports developer velocity while reducing exposure.
- Inventory and prioritisation
Identify secret types and prioritise migration based on exposure and criticality. - Integration patterns
Implement standard retrieval for CI/CD and runtime environments to reduce manual distribution. - Access controls and governance
Apply least privilege access to secrets with traceability and exception handling. - Rotation and revocation readiness
Implement rotation where feasible and define rapid revocation procedures for incidents.
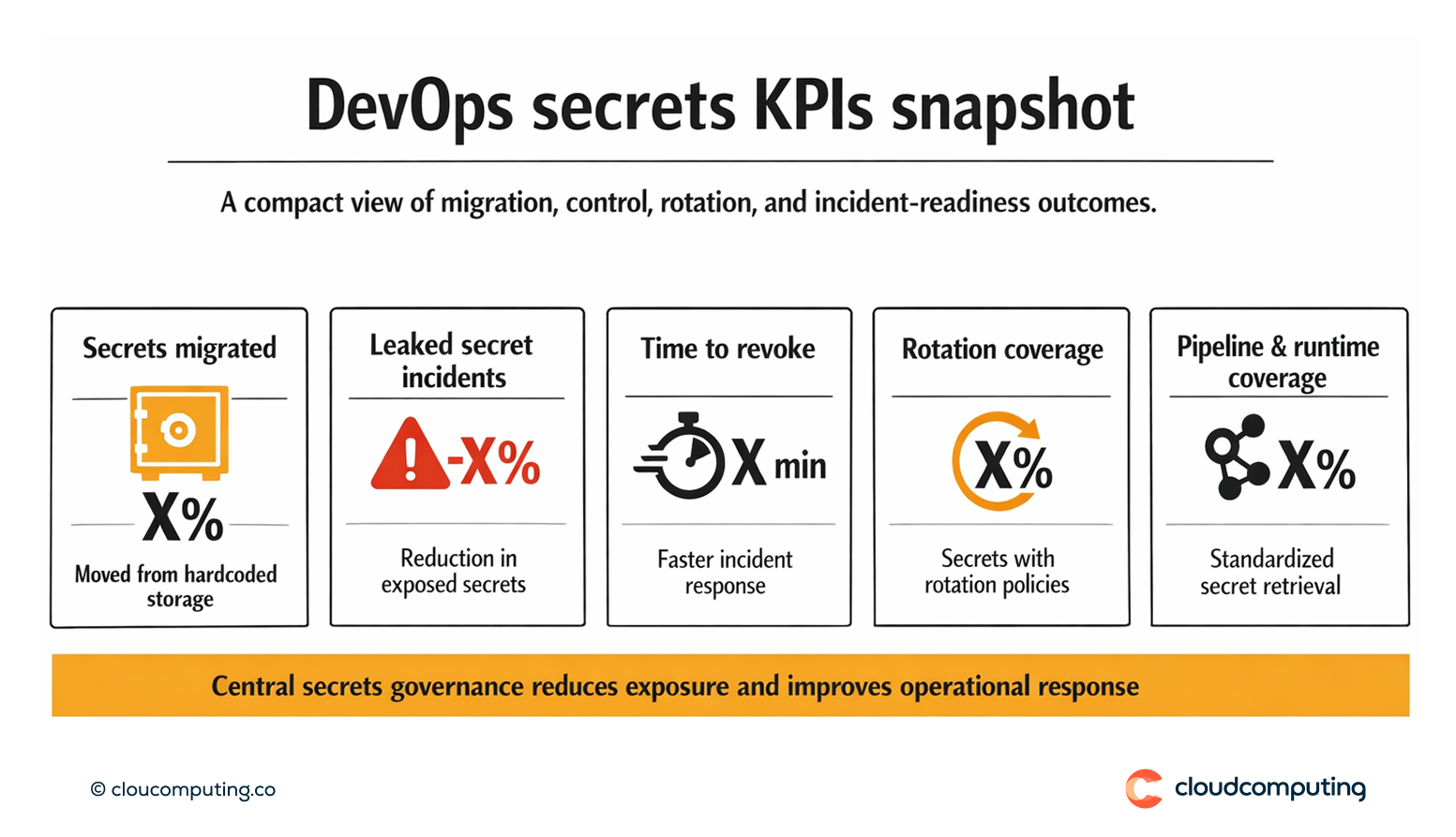
Expected outcome
- Less hardcoding across code and configuration
- Safer pipelines through controlled secret retrieval and governance
- Faster DevSecOps adoption via repeatable integration patterns
- Improved incident response with quicker secret revocation
Quick Answers
What is DevOps secrets management?
Centralising how secrets are stored, accessed, and rotated across CI/CD and application environments.
Why is hardcoding secrets risky?
It increases exposure and makes rotation and revocation slow during incidents.
How do you preserve developer velocity?
By providing standard integrations and self-service retrieval under policy.