The Problem
Users can access corporate apps from unmanaged or non-compliant devices.
Without device trust checks, identity controls alone cannot confirm device posture, making it easier for compromised, outdated, or risky endpoints to access sensitive resources.
Organisations face a difficult balance between security and productivity when controls are not context-aware.
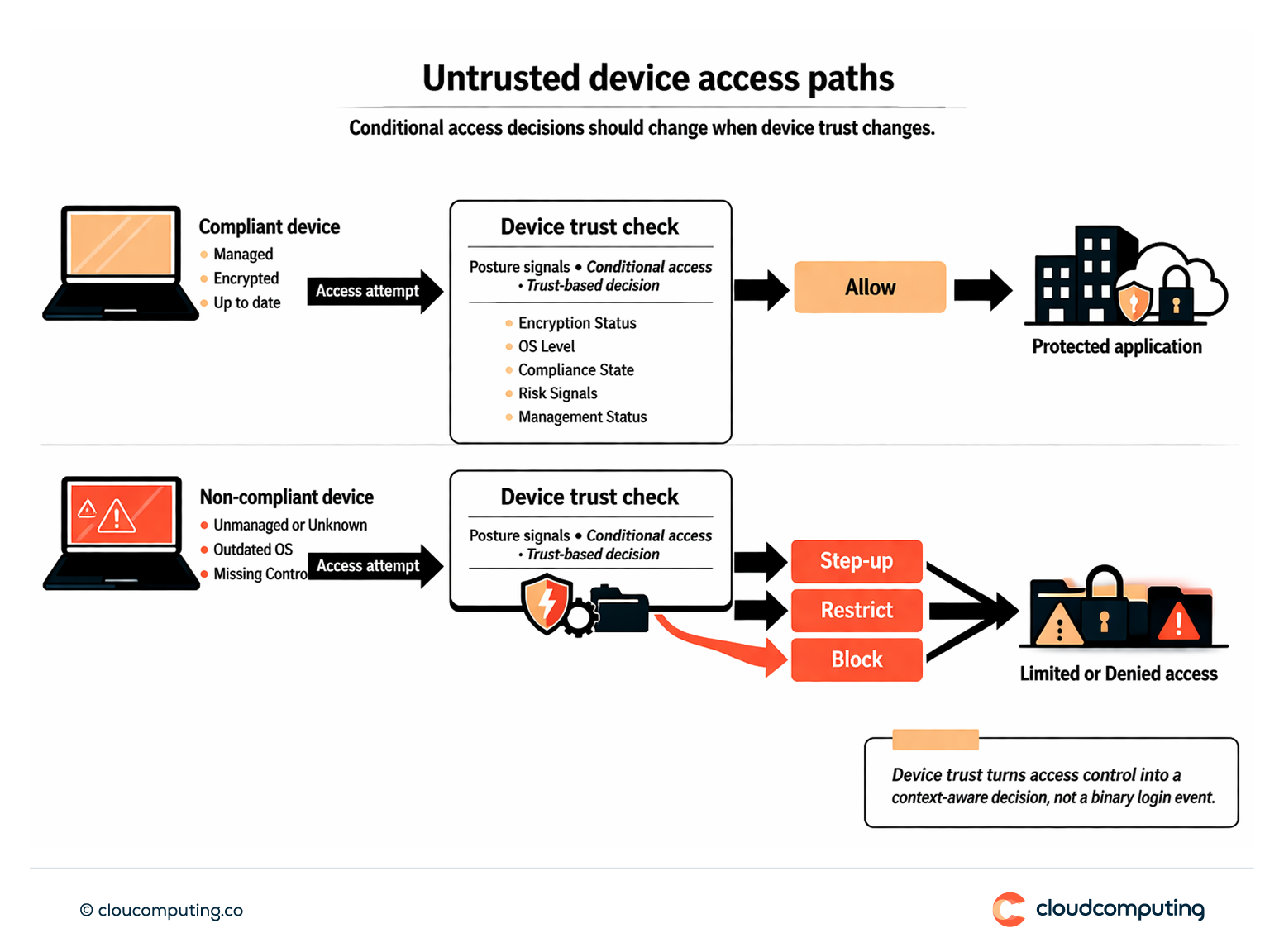
How we solve it: Enforce device posture checks and conditional access decisions based on compliance and trust signals.
We implement device-trust-driven access control so applications and sensitive resources are protected by posture-aware policies.
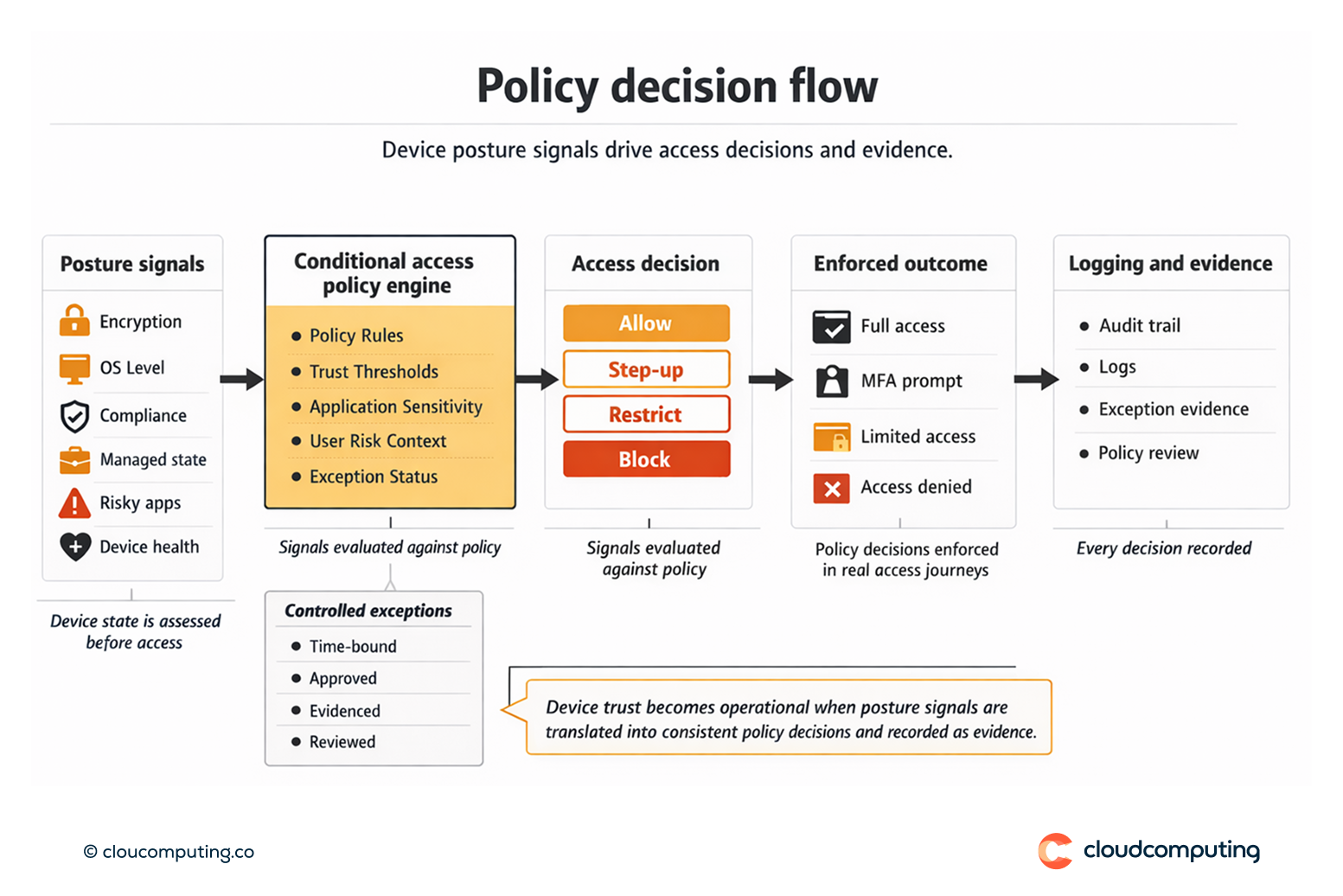
- Define trust signals and policy tiers
We define which posture signals matter (encryption, OS level, compliance status, risky apps) and map them to access outcomes. - Conditional access decisions
We enforce allow, restrict, step-up, or block decisions based on compliance and risk. - Exception governance
We implement controlled exceptions with time bounds and evidence, avoiding informal bypass paths.
Expected outcome
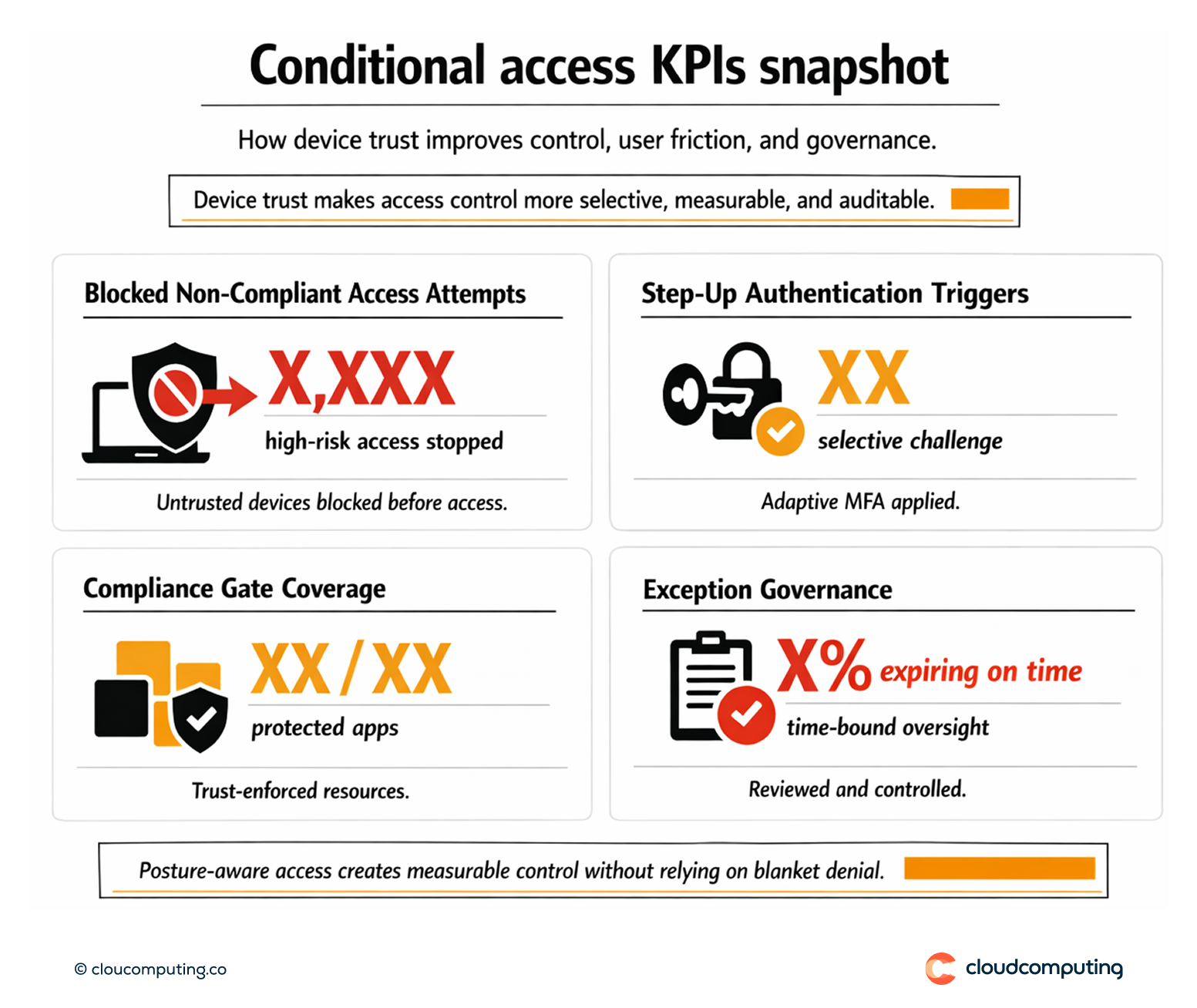
- Stronger Zero Trust controls by enforcing device trust before granting access
- Reduced exposure from unmanaged and non-compliant devices
- Less disruption through risk-tiered policies and step-up rather than blanket blocks
- Improved audit posture by evidencing posture-aware access decisions
Quick Answers
What is device trust in Zero Trust?
A posture-based assessment that confirms a device meets compliance requirements before access is granted.
Why is identity alone not enough?
Identity cannot confirm whether the device is encrypted, updated, or managed; device posture adds that assurance layer.
How do you avoid blocking legitimate work?
By using tiered outcomes such as restricted access or step-up authentication rather than blanket denial.