The Problem
Devices fall out of compliance and no one notices in time.
Encryption is disabled, passcodes weaken, OS versions lag, risky apps appear, and configuration drift accumulates.
Without continuous posture monitoring and remediation, organisations maintain “unknown” risk pockets that surface during audits or incidents.
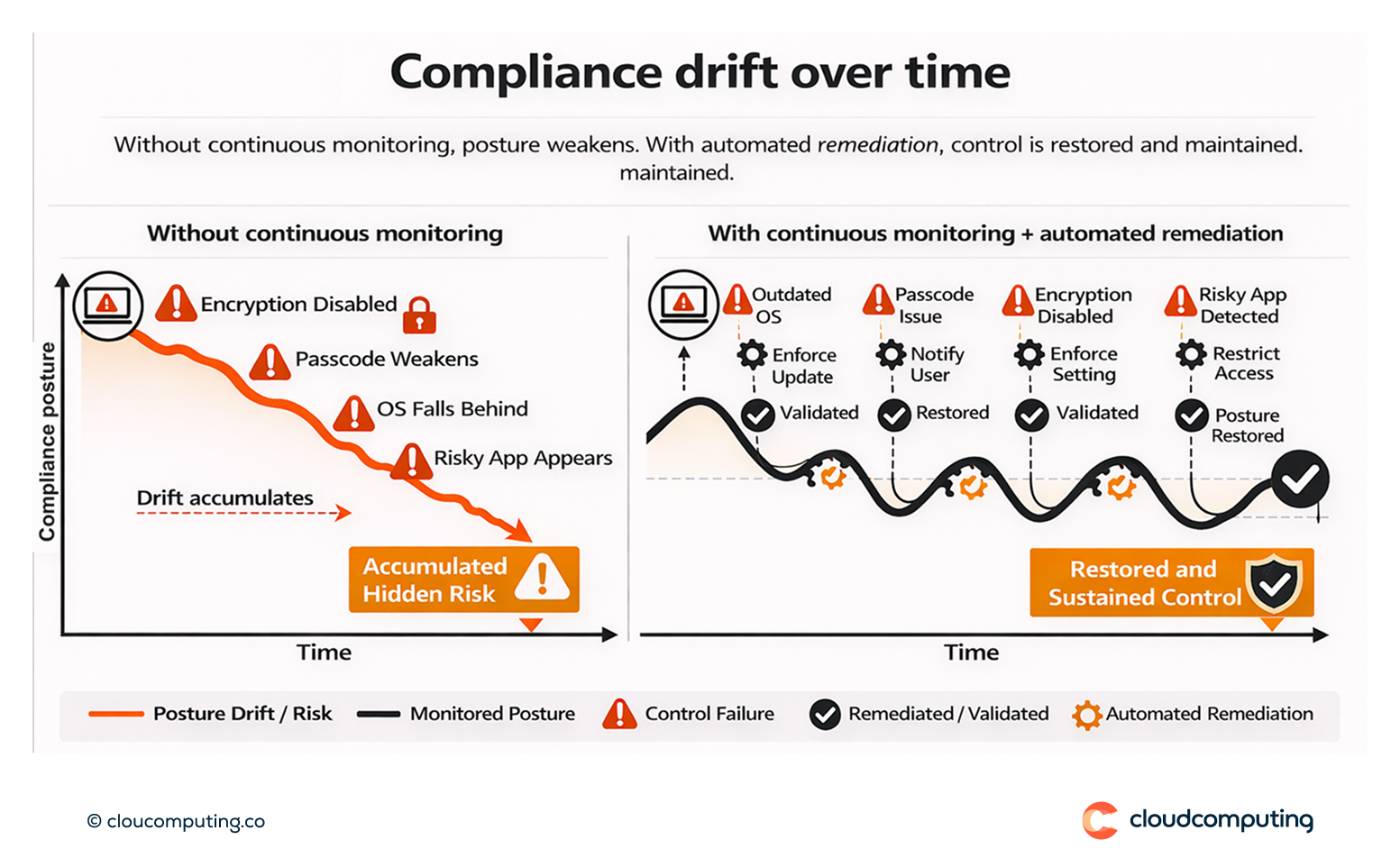
How we solve it: Enforce compliance rules, monitor posture continuously, and trigger automated remediation when devices fall out of policy.
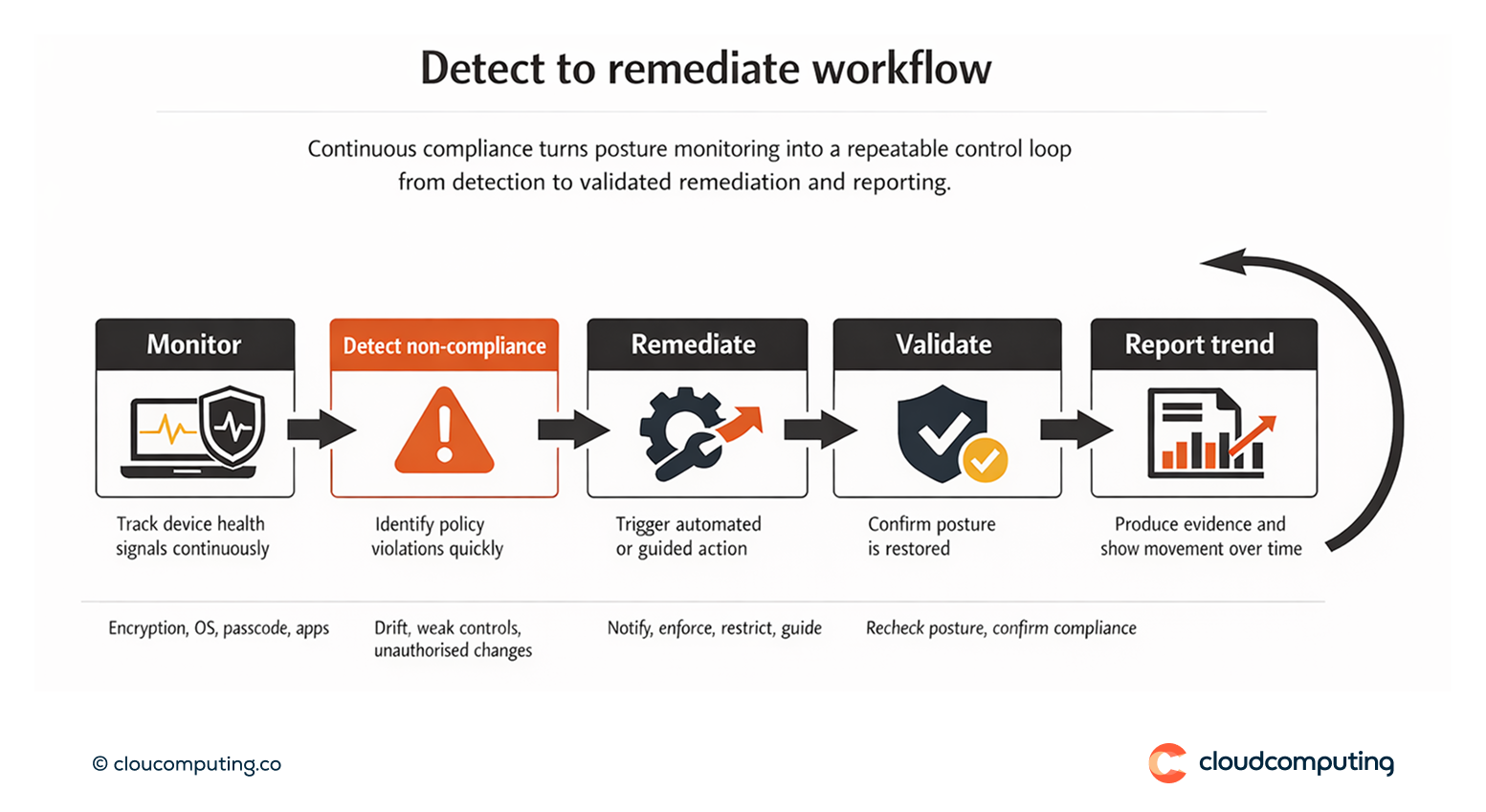
We implement continuous compliance as an operational control: define rules, monitor health signals, and remediate automatically where possible.
- Compliance rules and risk tiers
We define compliance requirements (encryption, OS level, passcode strength, risky apps) and apply them by device class and ownership. - Continuous posture monitoring
We monitor device health signals and detect non-compliance quickly. - Automated remediation
We trigger actions such as notifying users, restricting access, enforcing settings, or guiding remediation through supported workflows. - Evidence and reporting
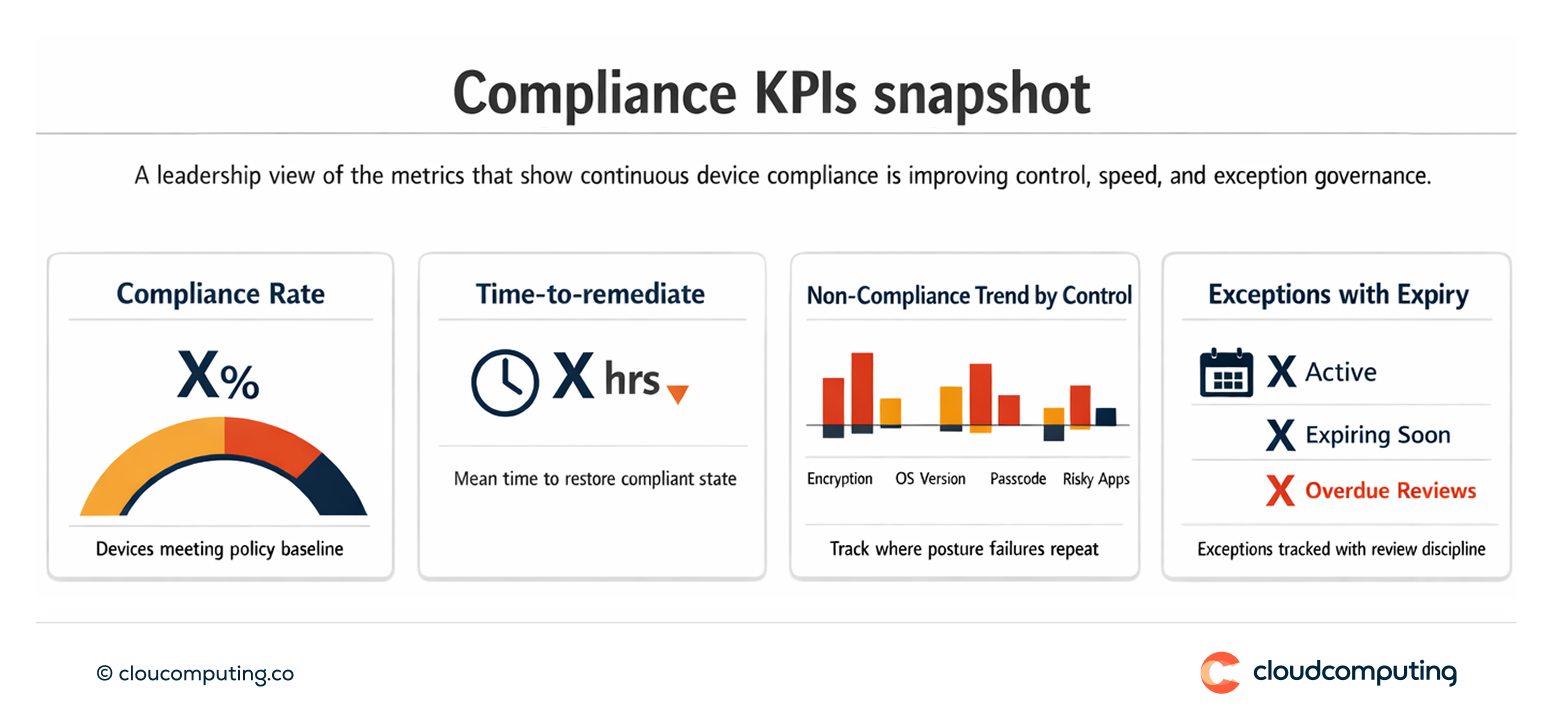
We produce posture evidence suitable for audit narratives and operational reporting.
Expected outcome
- Reduced risk exposure through timely detection and remediation
- Fewer unknown devices and fewer unmanaged posture exceptions
- Audit-ready posture with evidence of continuous enforcement
- Lower incident likelihood driven by basic hygiene failures
Quick Answers
What is continuous compliance posture?
Ongoing monitoring and enforcement of device health requirements, rather than periodic checks.
Why is automated remediation important?
It closes posture gaps quickly and reduces reliance on manual interventions.
How does this support audits?
It provides repeatable evidence that controls are enforced continuously, not only during audit windows.