The Problem
Local admin rights on endpoints enable malware and ransomware paths.
Excess privilege allows unauthorised software installs and credential harvesting, and increases persistence opportunities.
Yet removing local admin without a structured elevation model can disrupt productivity.
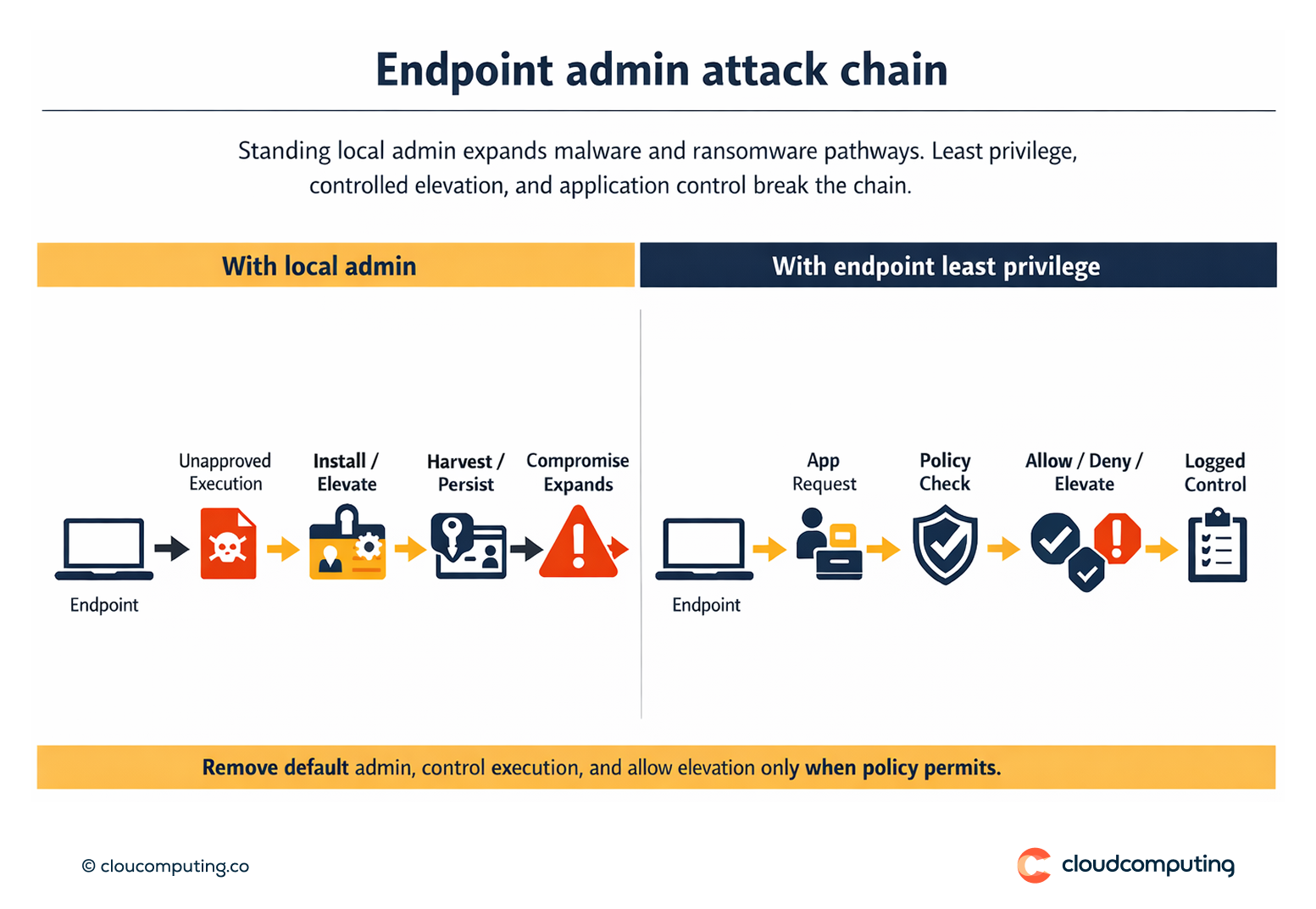
How we solve it: Deploy Delinea Privilege Manager to remove excess privilege, control application execution, and enable controlled elevation.
We implement least privilege on endpoints with policy-driven elevation and application control so productivity is preserved while risk is reduced.
- Privilege reduction strategy
Remove standing local admin and define role-based elevation needs. - Application control
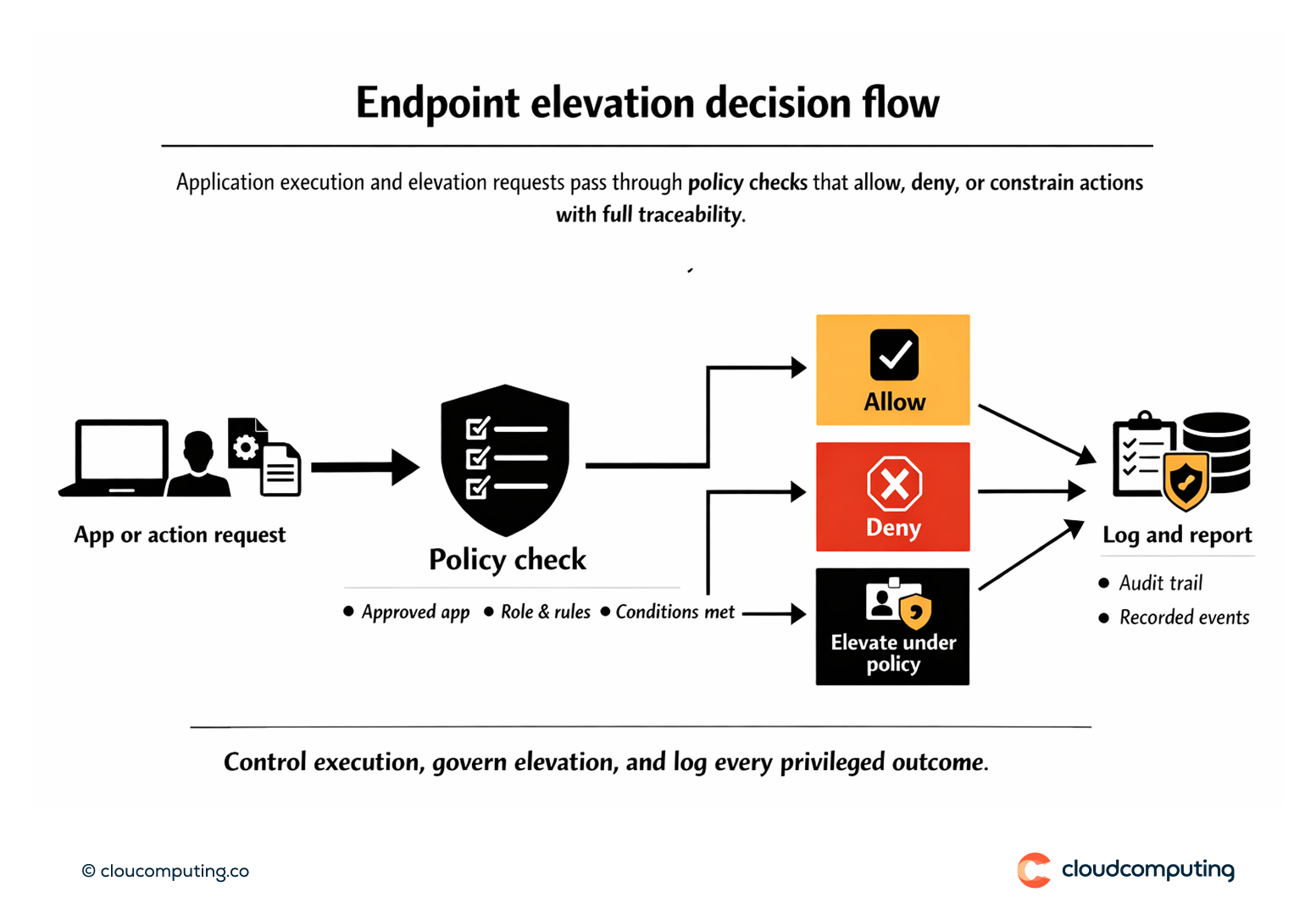
Control what can execute and under which conditions, reducing unauthorised pathways. - Controlled elevation
Enable elevation for approved actions with constraints, approvals where appropriate, and traceability. - Phased rollout and tuning
Roll out in waves and tune policies based on real usage to minimise disruption.
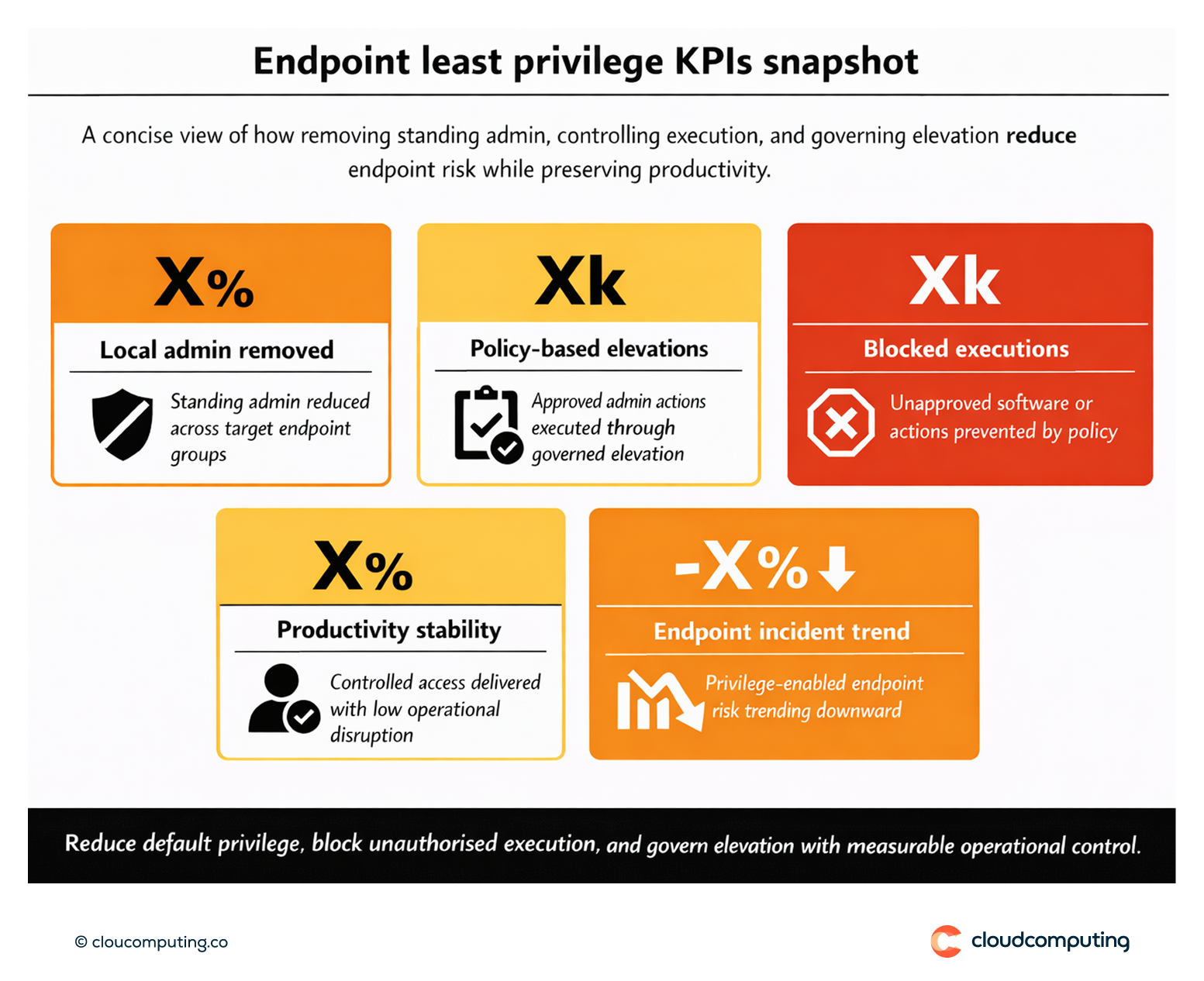
Expected outcome
- Reduced endpoint compromise risk without blanket admin rights
- Maintained productivity through predictable, controlled elevation
- Lower ransomware exposure by blocking common privilege-enabled techniques
- Improved compliance posture with auditable privilege use
Quick Answers
What is endpoint least privilege?
Removing standing local admin rights and enabling controlled elevation only when required.
How does application control help?
It reduces the ability for unauthorised software to run, cutting common malware paths.
How do you avoid user disruption?
By designing predictable elevation rules and rolling out in phases with tuning.