The Problem
Privileged actions often happen with limited accountability.
Direct RDP/SSH connections and shared credentials reduce visibility into what was done, by whom, and when.
This slows investigation, increases insider and third-party risk, and leaves audit narratives incomplete.
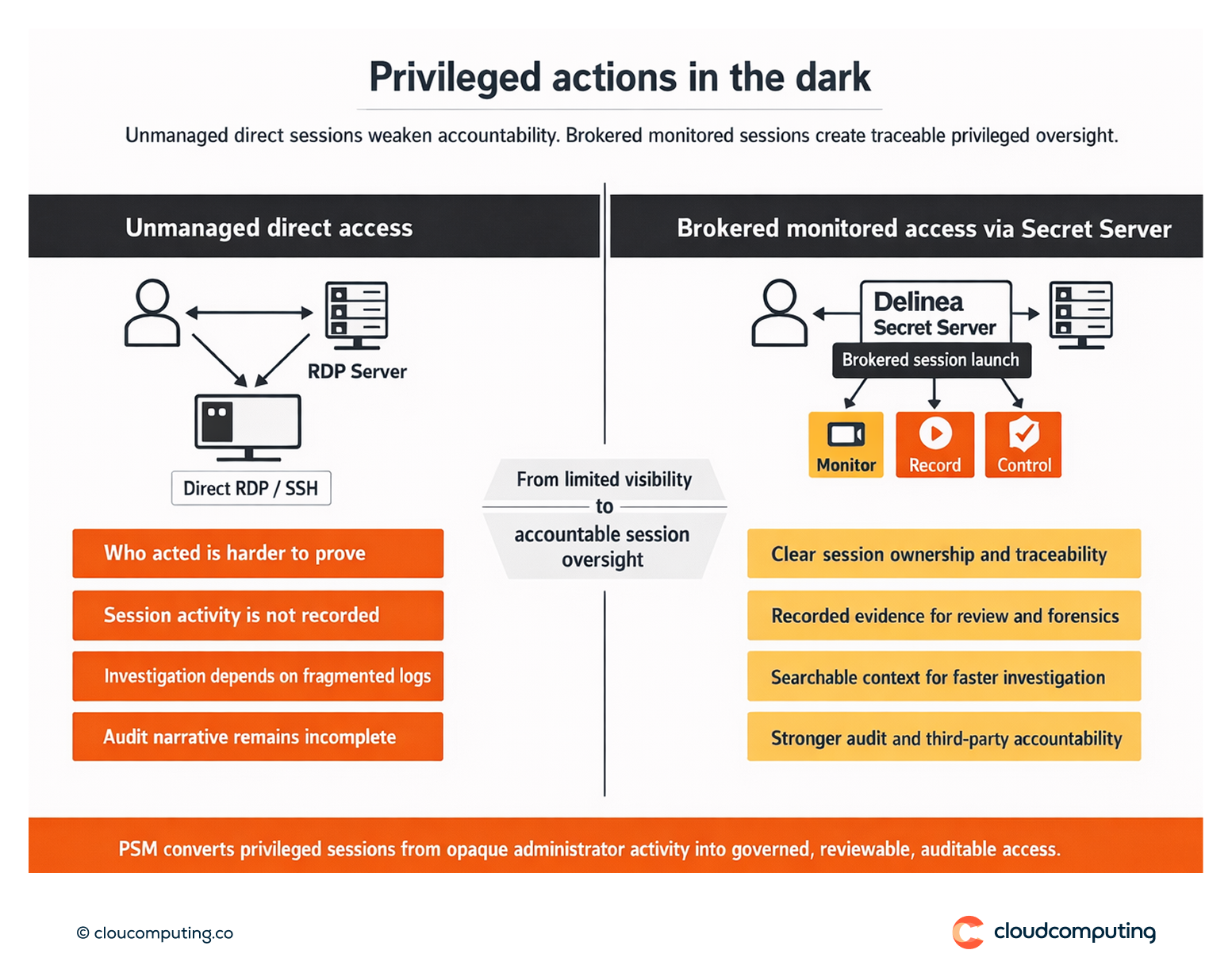
How we solve it: Enable session monitoring, recording, and real-time control for privileged sessions launched via Secret Server.
We route privileged access through controlled session launch paths and implement oversight so privileged activity becomes traceable and auditable.
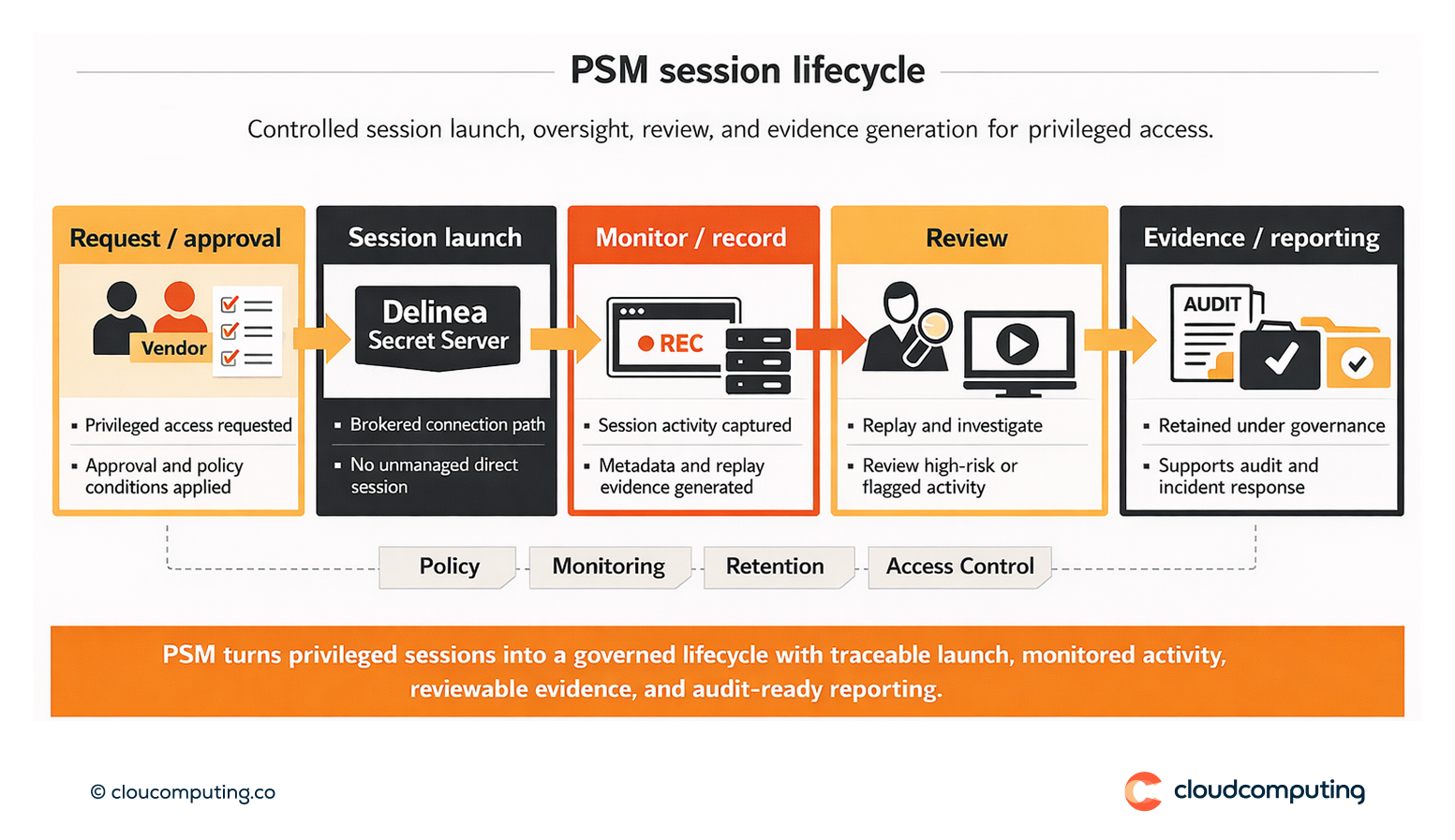
- Session brokering
Standardise access paths by launching privileged sessions through Secret Server. - Monitoring and recording
Capture session activity and metadata to support accountability and forensics. - Real-time controls
Apply policy and control options for high-risk activity, including termination where appropriate. - Evidence governance
Define retention, access controls for recordings, and reporting aligned to audit and incident response.
Expected outcome
- Auditable privileged activity with clear accountability
- Faster investigation through session replay and searchable context
- Reduced insider and third-party risk by controlling and evidencing privileged access
- Stronger operational discipline by removing unmanaged session paths
Quick Answers
What is PSM?
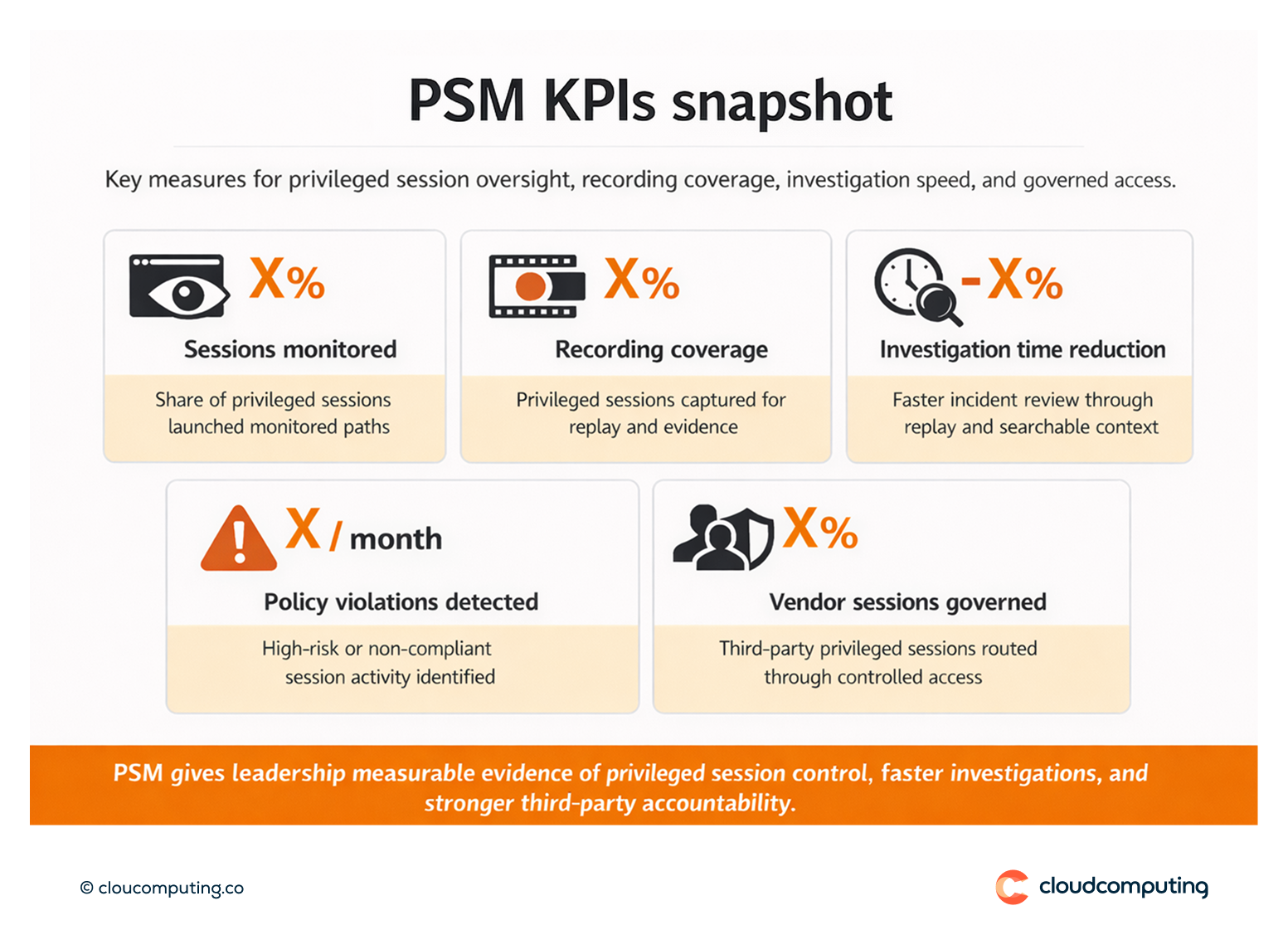
Oversight of privileged sessions through monitoring, recording, and controlled access paths.
Why is PSM needed if credentials are vaulted?
Vaulting controls secrets; PSM evidences the actions performed using privileged access.
Who should access recordings?
Authorised roles only, under defined governance and retention rules.
