The Problem
BYOD creates friction. Employees worry about privacy and personal data access, while IT worries about enforcing corporate controls and protecting data on unmanaged devices.
Without a clear model, adoption is low, exceptions proliferate, and organisations accept higher risk than necessary.
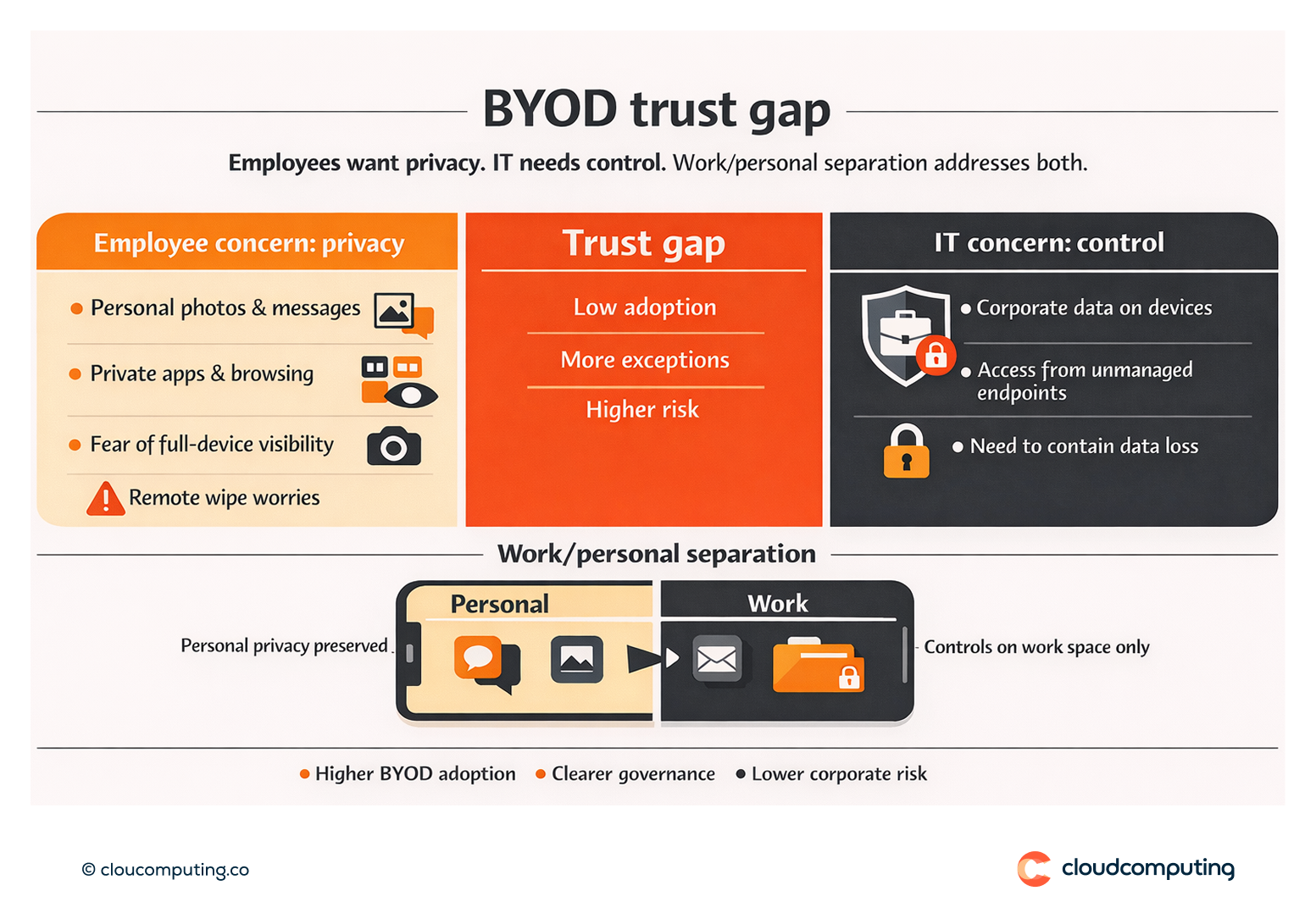
How we solve it: Implement BYOD models with work/personal separation and clear privacy boundaries to increase adoption while managing risk.
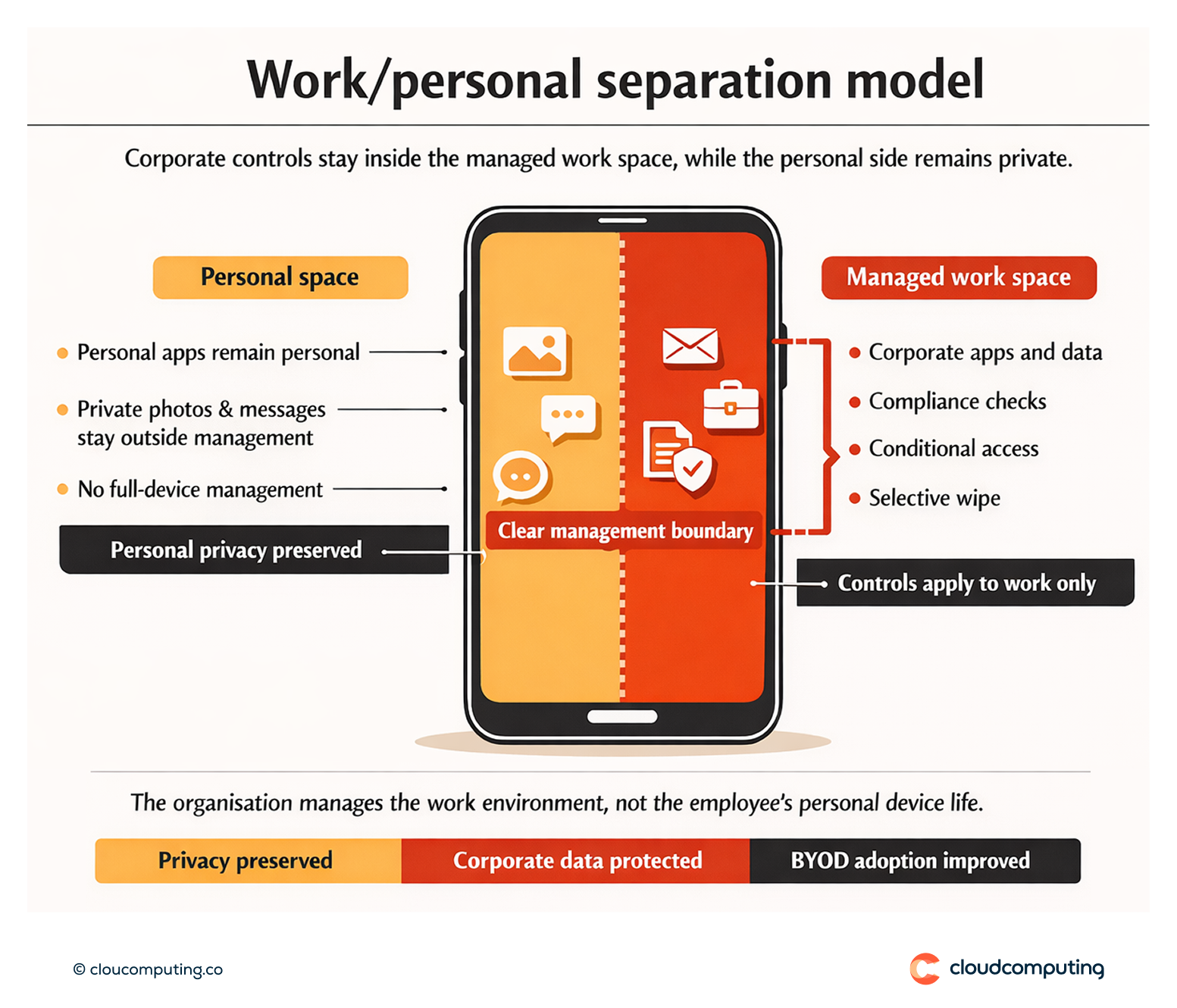
We deploy a BYOD approach that protects corporate assets without overreaching into personal device space.
- BYOD architecture and separation
We implement container or work profile separation so corporate apps and data are managed independently. - Clear privacy policy and user communication
We define and communicate what IT can and cannot see or manage to drive adoption and trust. - Security controls for the work space
We enforce required controls for corporate apps and data, including compliance rules and conditional access integration.
Expected outcome
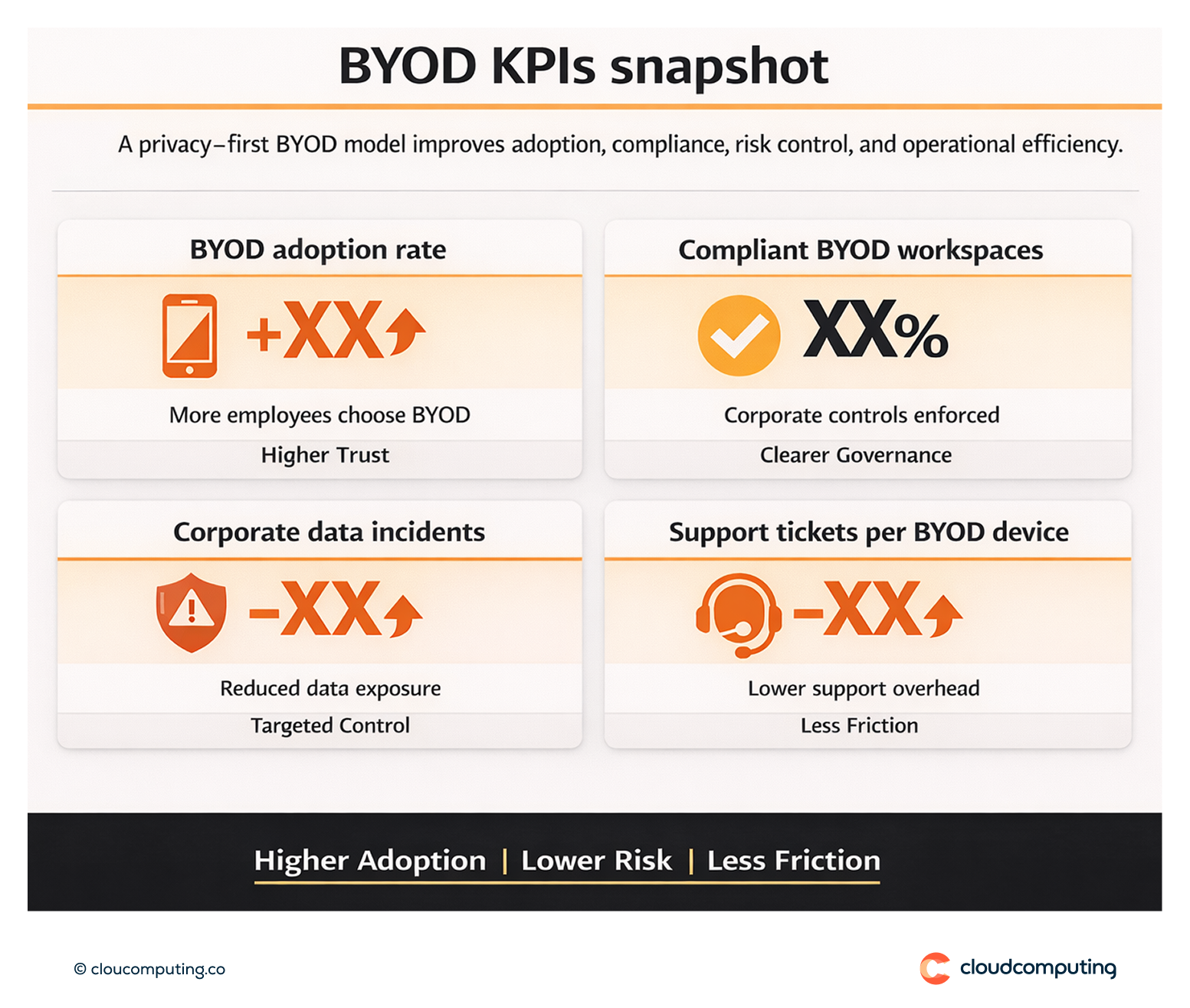
- Higher adoption through clear privacy boundaries and reduced employee friction
- Lower risk by enforcing controls on corporate apps and data
- Improved employee trust through transparent governance
- More consistent access control when combined with conditional access policies
Quick Answers
What is secure BYOD?
A model that allows personal devices to access corporate resources with managed controls applied to a separated work environment.
How is privacy protected?
Management scope is limited to the corporate workspace, not the personal side of the device.
Why does this improve adoption?
Employees accept BYOD controls when boundaries are clear and personal privacy is respected.