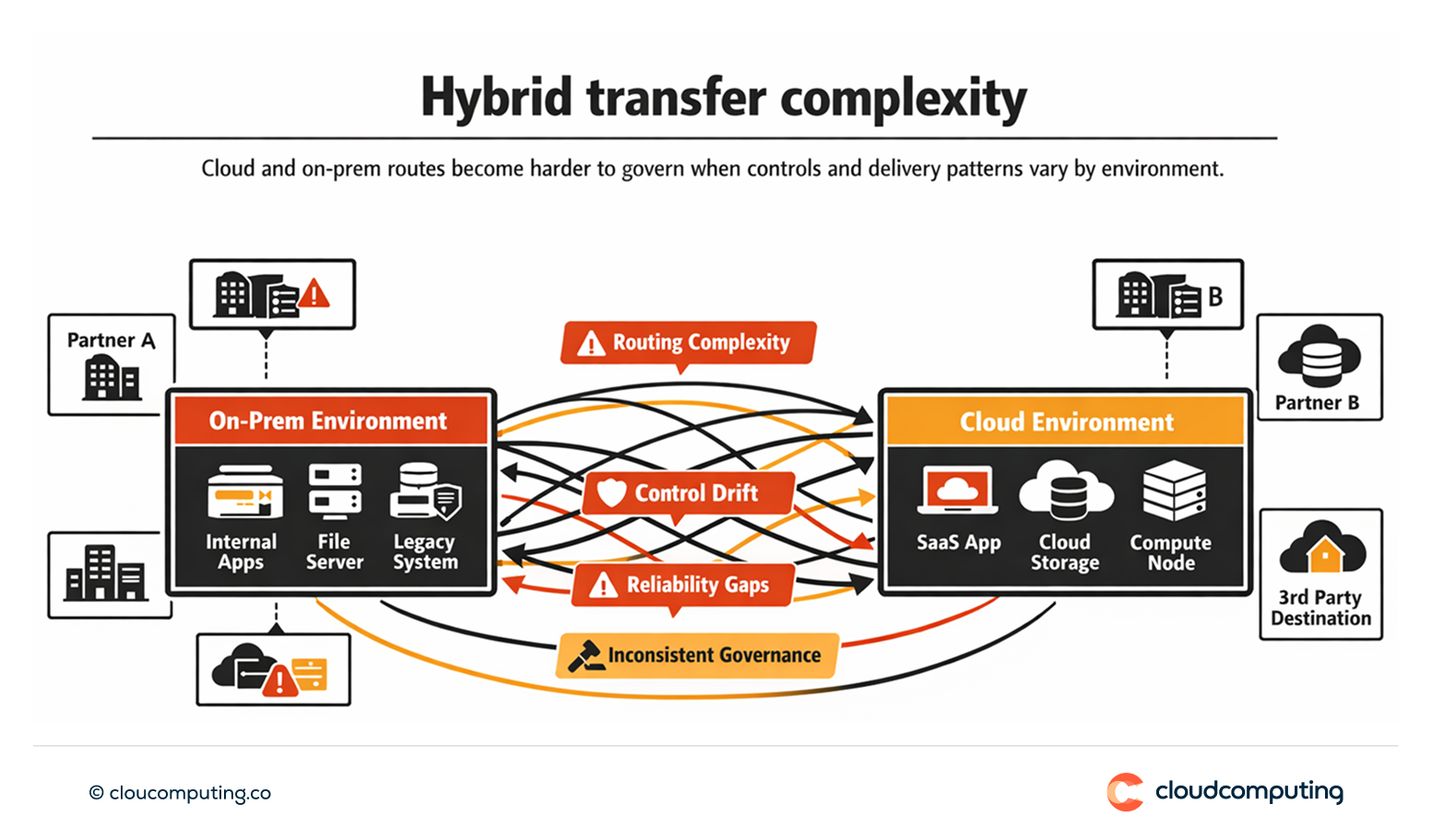
The Problem
Hybrid architectures complicate routing, security, and reliability across cloud and on-prem.
Transfers cross multiple network zones, partner endpoints vary, and controls drift between environments.
Without consistent patterns, teams face operational complexity and inconsistent governance.
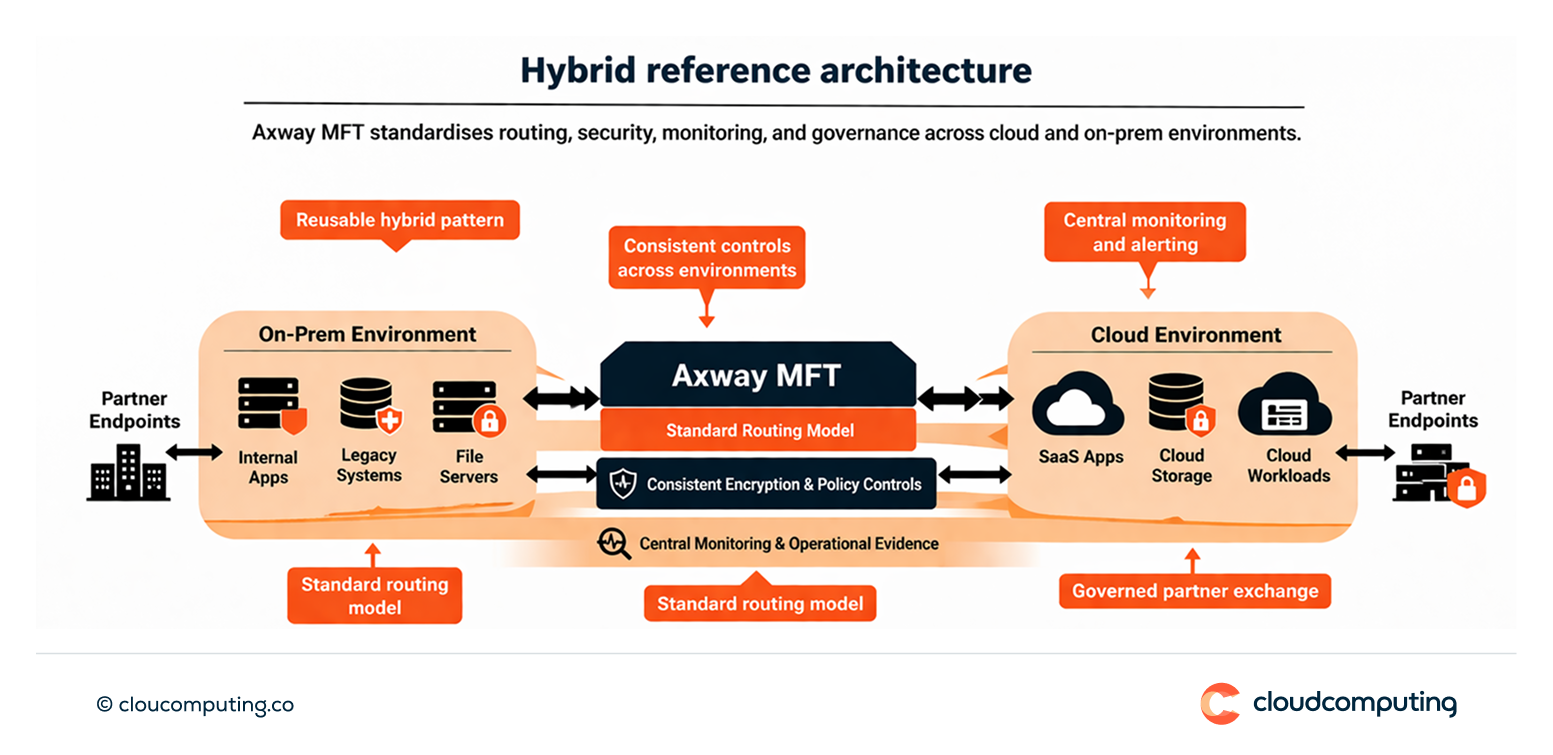
How we solve it: Design secure hybrid patterns, optimise routing, and apply consistent controls end-to-end using Axway MFT.
We implement architecture patterns that keep governance consistent across environments and maintain operational reliability.
- Hybrid reference patterns
Define standard routes and security controls for cloud-to-cloud, on-prem-to-cloud, and partner exchanges. - Consistent control enforcement
Apply encryption, policy controls, monitoring, and evidence consistently across environments. - Routing and performance optimisation
Optimise transfer routes and ensure reliability controls are applied where needed.
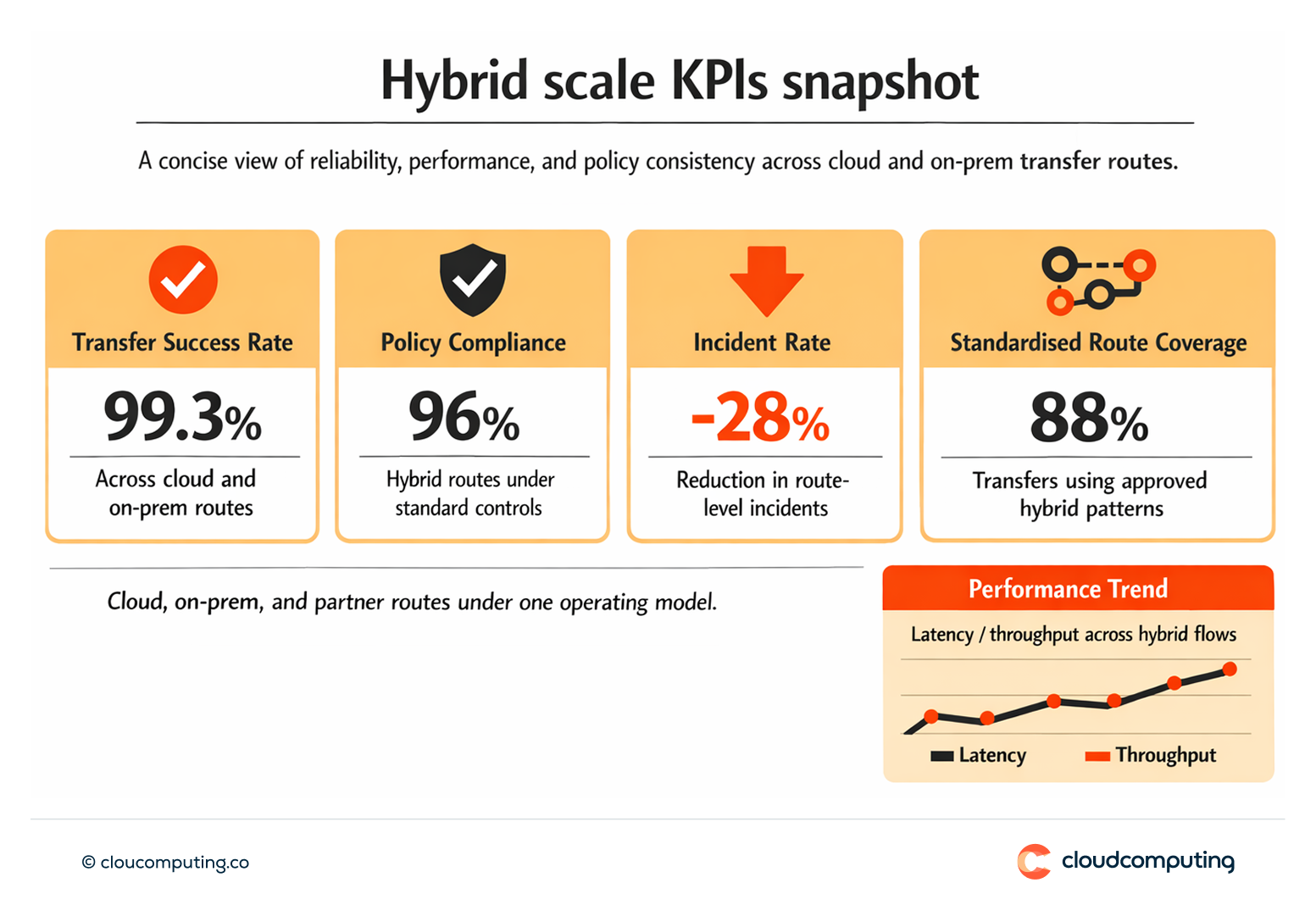
Expected outcome
- Scalable transfers across environments with predictable routing and performance
- Consistent governance across cloud and on-prem with standard policies
- Reduced operational complexity through reusable hybrid patterns
- Improved reliability by applying consistent delivery controls end-to-end
Quick Answers
What makes hybrid file transfer difficult?
Multiple network zones, varied endpoints, and inconsistent controls across cloud and on-prem environments.
What is a hybrid reference pattern?
A standard architecture and policy model for routing, security, monitoring, and evidence across environments.
How do you keep governance consistent?
By applying the same policy, encryption, monitoring, and reporting model regardless of where the transfer runs.