The Problem
Proving access control, data exposure controls, and change history is difficult.
Evidence is fragmented across logs, gateway configurations, and team-owned documentation.
Audits become manual exercises, and teams struggle to demonstrate consistent enforcement.
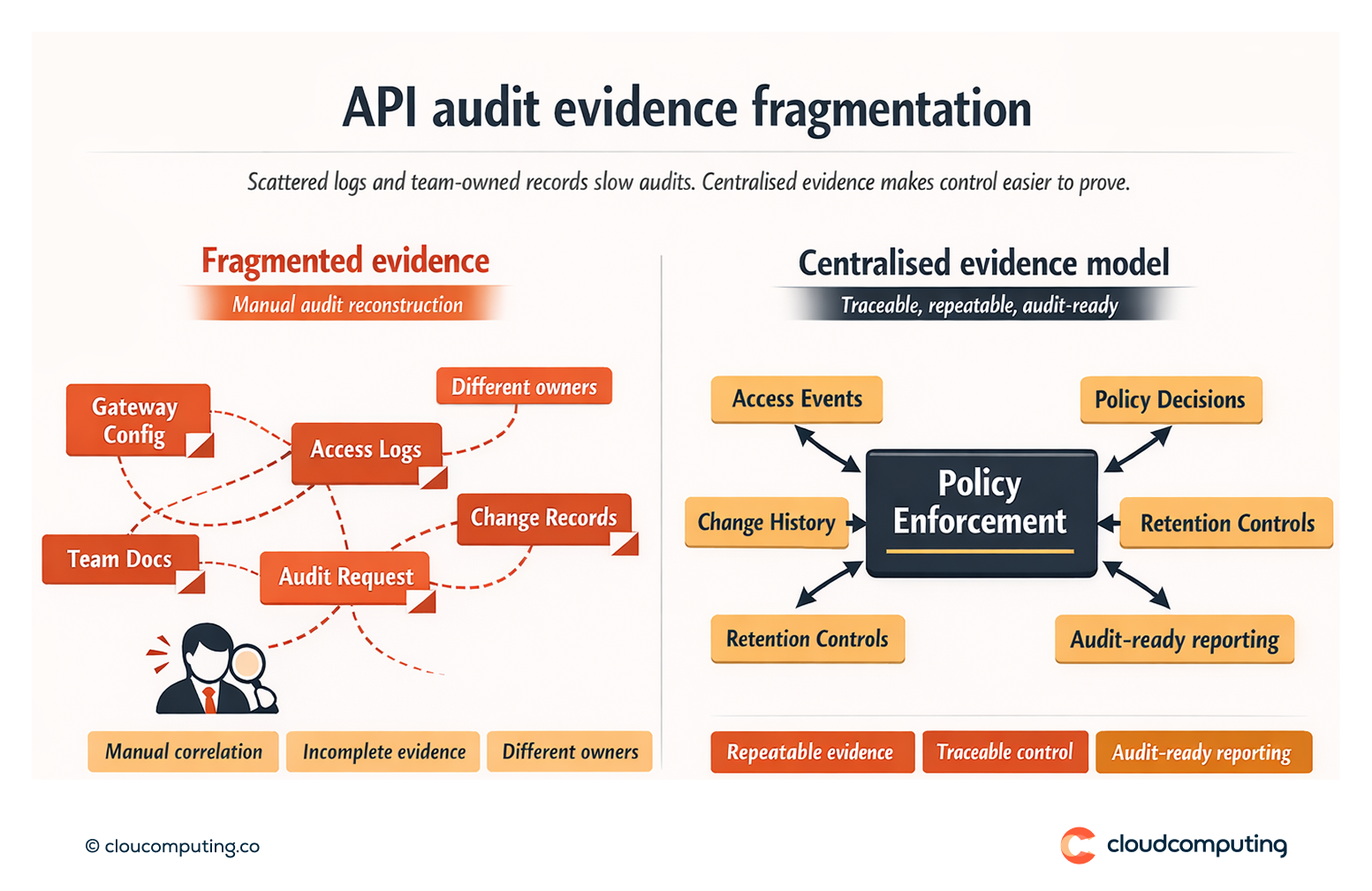
How we solve it: Centralise policy enforcement, logging, and audit-ready reporting for API traffic and changes.
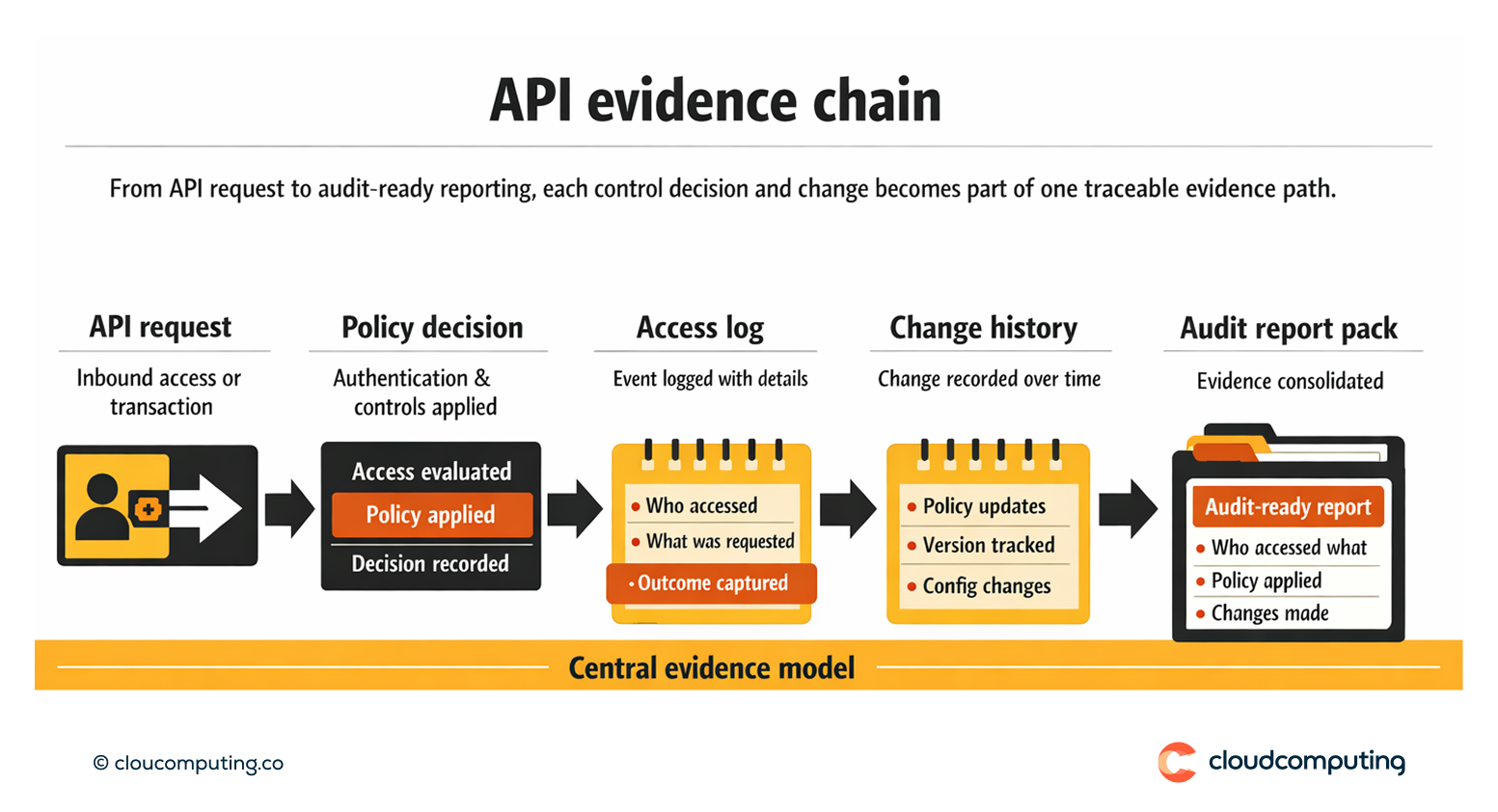
We implement an evidence model that captures policy decisions, access events, and change history in a repeatable format.
- Policy enforcement evidence
Ensure security and traffic controls are applied centrally with traceable policy outcomes. - Logging and retention
Capture access logs, change history, and key events with appropriate retention and access controls. - Audit-ready reporting packs
Provide standard reports for recurring audit questions: who accessed what, policy applied, and changes made.
Expected outcome
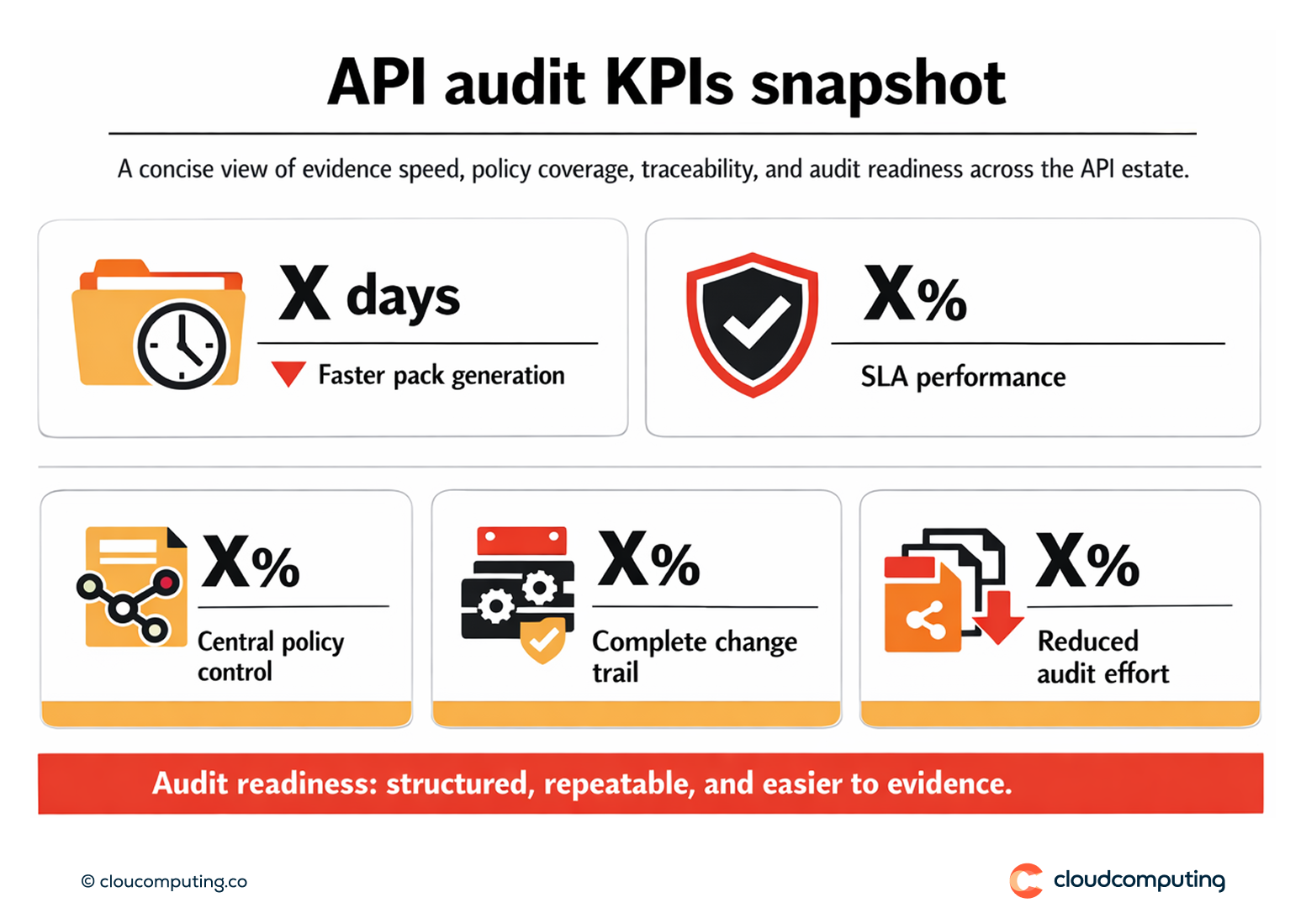
- Faster audits through repeatable evidence packs
- Stronger evidence of access control and policy enforcement
- Reduced audit fatigue by eliminating manual log correlation
- Improved compliance readiness with consistent reporting and retention
Quick Answers
What evidence do audits typically require for APIs?
Proof of access control, policy enforcement, logging, and change history for APIs and gateway policies.
Why is API audit evidence hard?
Logs and configurations are spread across teams and environments without central reporting.
What changes with a central evidence model?
Audit reporting becomes repeatable, consistent, and faster to produce.