The Problem
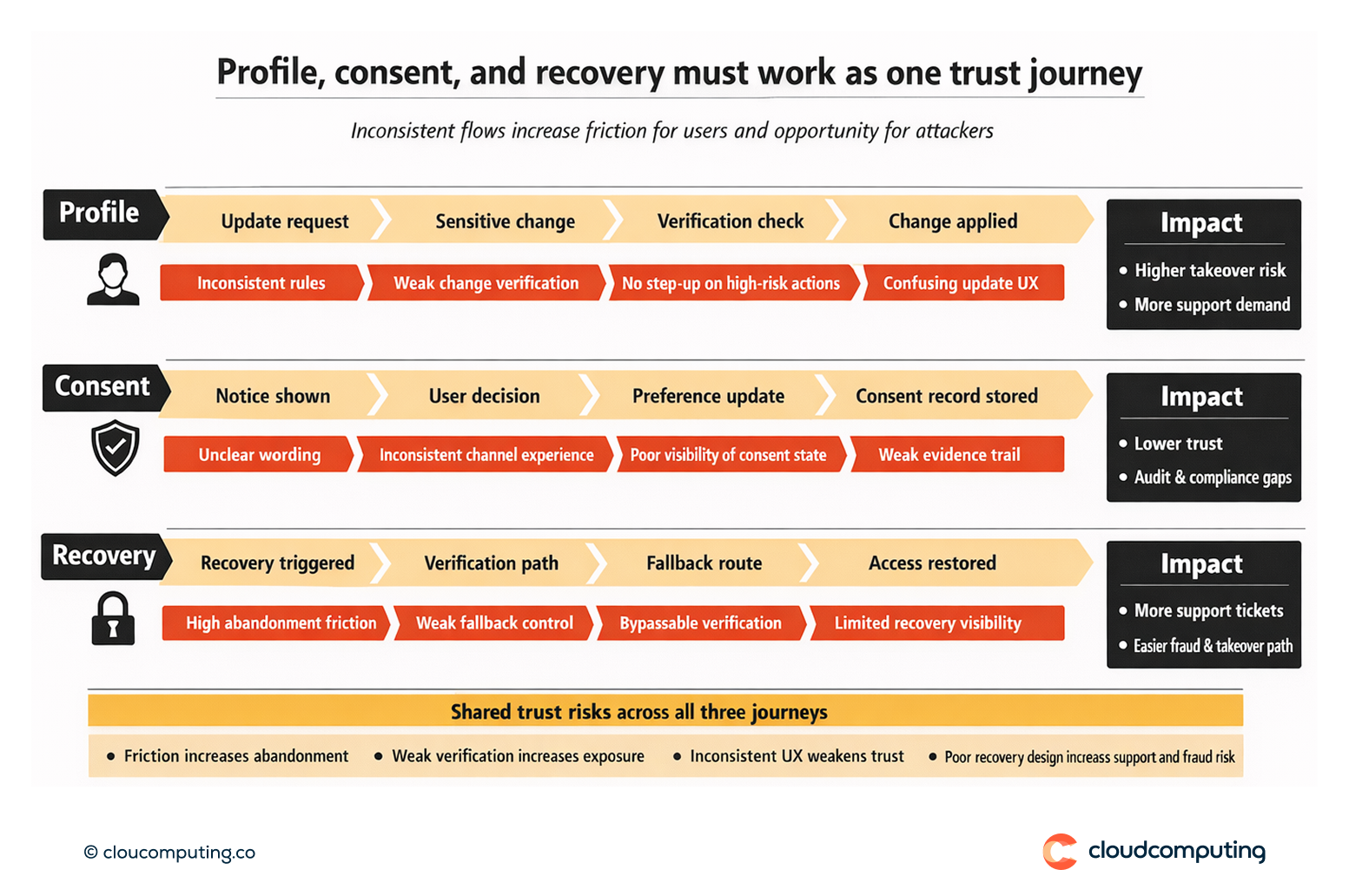
Customer trust is weakened when profile, consent, and recovery are inconsistent across channels.
Recovery flows can be either painful (high abandonment) or insecure (easy to bypass). Consent management may be unclear, and profile changes may lack appropriate verification.
These gaps create a dual risk: increased support demand and increased exposure to account takeover and fraud via weak recovery paths.
How we solve it: Design secure, brand-aligned profile, consent and recovery journeys with strong verification and consistent policy.
We build customer trust journeys that are consistent across channels, enforce verification at the right moments, and reduce support demand without weakening security.
- Profile management with assurance
We design profile update flows with verification appropriate to sensitivity (e.g., email/phone change, device changes), including step-up where required. - Consent clarity and governance
We align consent capture and management to policy and UX standards, ensuring consistent communication and auditable records. - Secure recovery flows
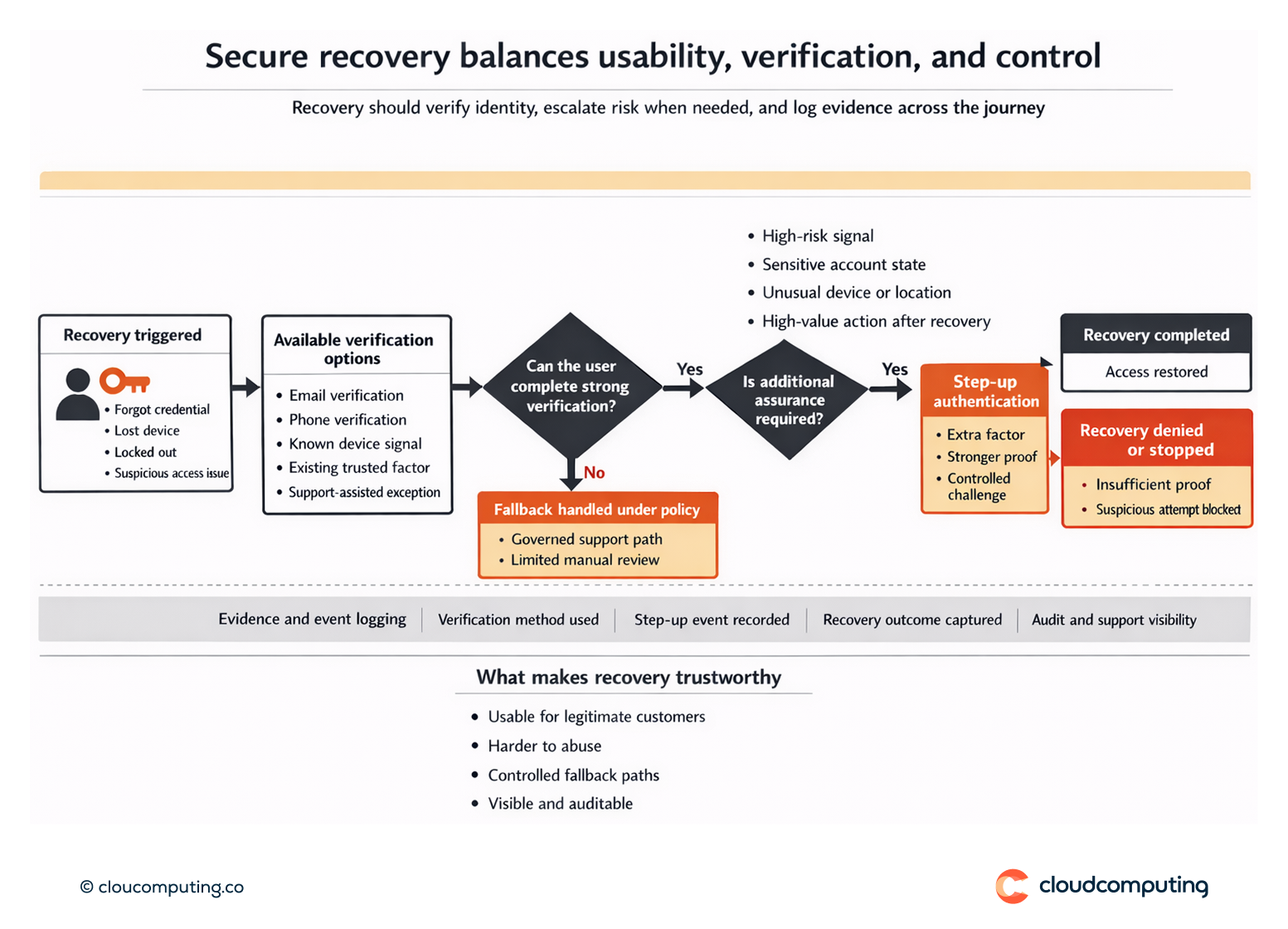
We implement recovery that is usable but resilient to abuse, with controlled fallback paths and visibility into recovery events. - Operational evidence and support reduction
We implement reporting and support patterns that reduce manual intervention and enable quick resolution when users struggle.
Expected outcome
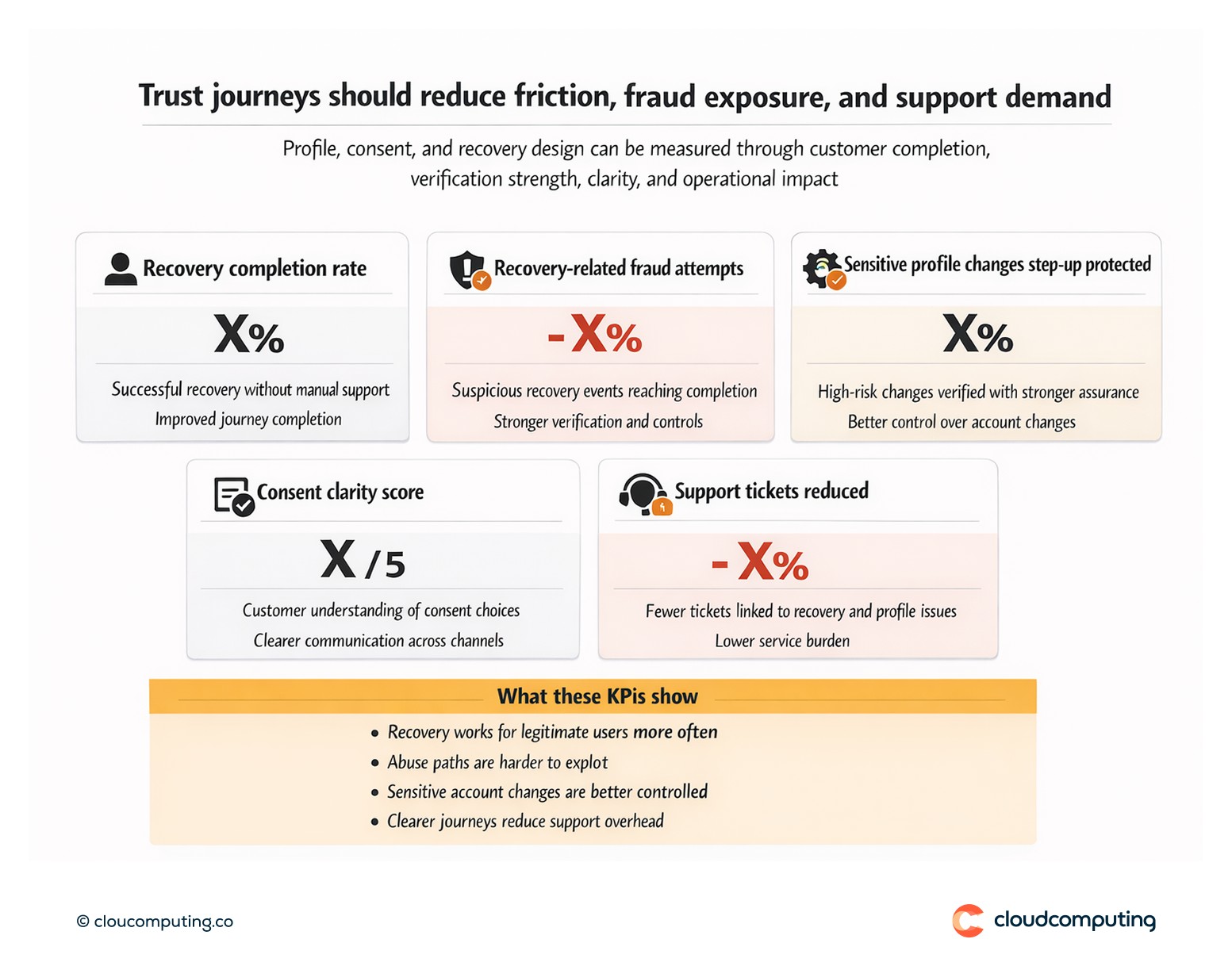
- Fewer support tickets from predictable, well-designed journeys
- Fewer risky recovery paths by strengthening verification and controlling exceptions
- Better customer trust through consistent UX and clearer consent management
- Reduced takeover risk by hardening high-value profile and recovery actions
Quick Answers
Why are recovery flows a common attack path?
Attackers often target recovery because weak verification can bypass stronger controls used at login.
What should trigger step-up in profile journeys?
Changes that impact account control or risk exposure, such as email, phone, device, or security settings.
How does consent management affect trust?
Clear, consistent consent journeys reduce confusion and improve transparency, supporting customer confidence and compliance narratives.