The Problem
A one-size MFA approach creates a conversion penalty or leaves risk unaddressed.
If MFA is forced on every login, friction increases and sign-up completion drops. If MFA is optional or inconsistently applied, attackers target high-value accounts and high-risk actions with minimal resistance.
The programme fails when assurance does not scale with risk and action sensitivity.
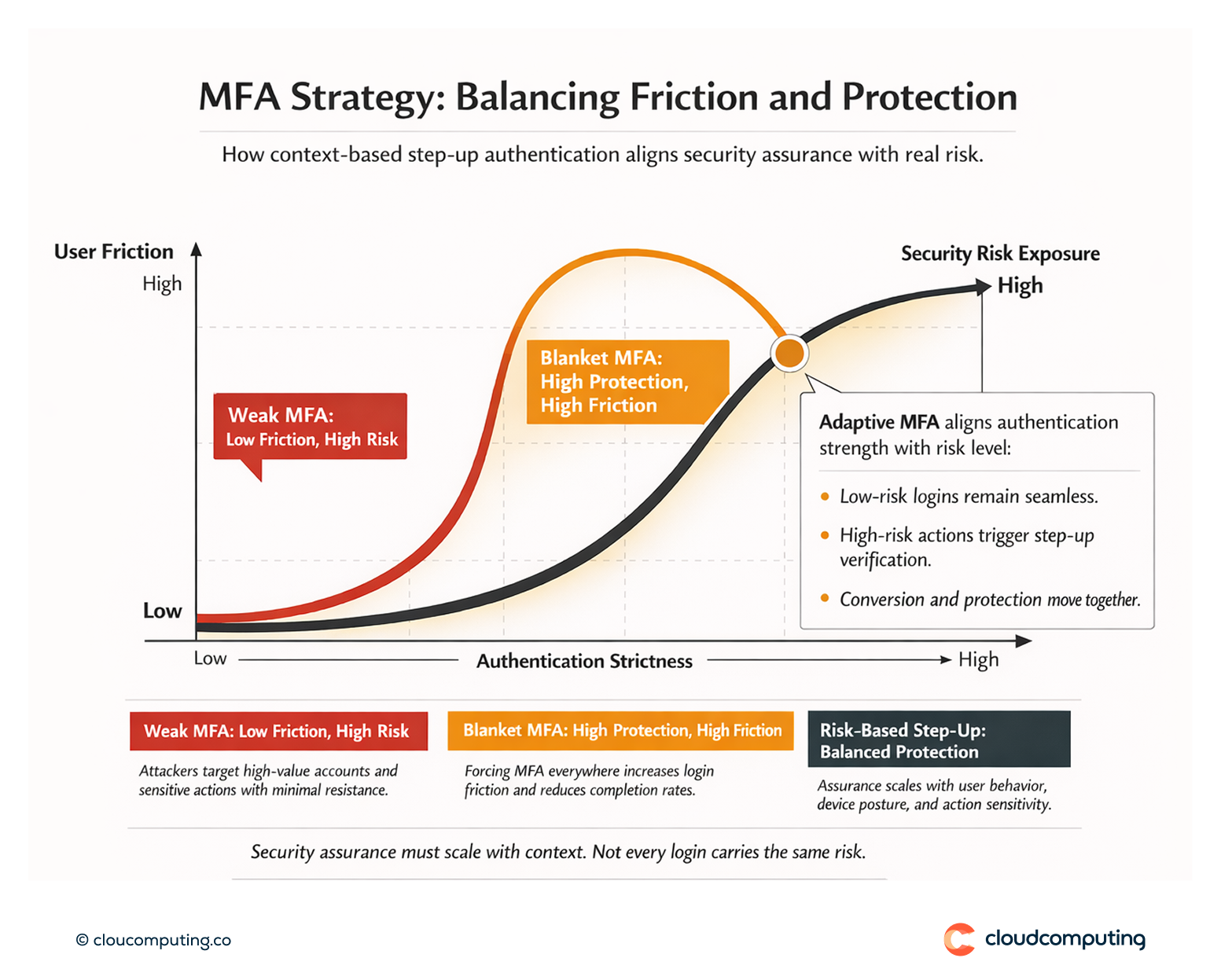
How we solve it: Enforce MFA with context-based policies and trigger step-up only when risk or action sensitivity requires it.
We implement MFA as a risk-managed control: baseline assurance where needed, and step-up at moments that matter, without degrading conversion unnecessarily.
- Define high-risk actions and assurance requirements
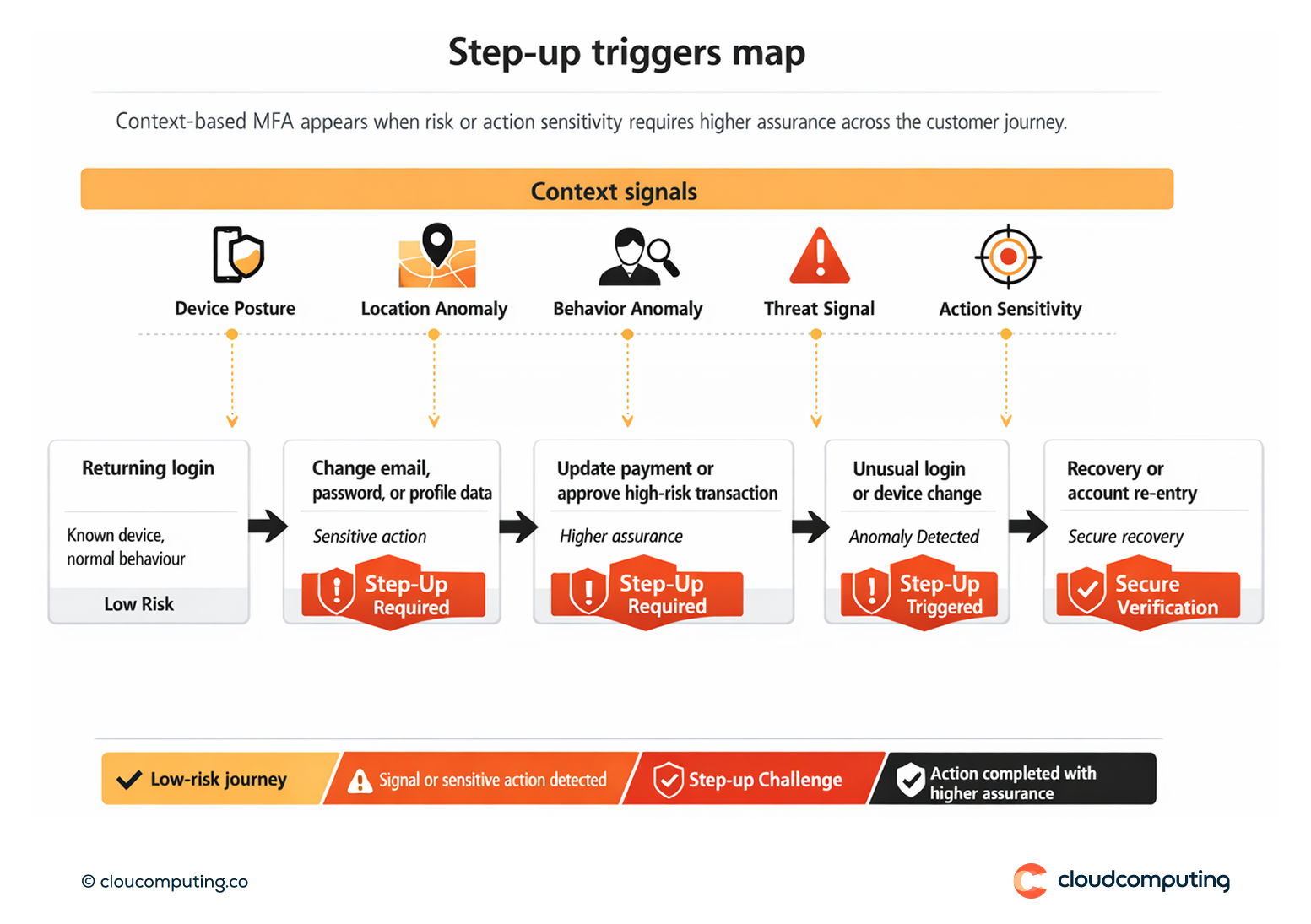
We identify where step-up is mandatory (payment changes, profile changes, device change, account recovery, admin functions, high-risk transactions). - Context-based policy design
We apply signals such as device, location, behaviour anomalies, and reputation to determine when MFA is required and when it can remain invisible. - Step-up integration across journeys
We ensure step-up is consistently triggered across web and mobile flows, including re-authentication points, not only at initial login. - Fraud-aware exception handling
We design controlled fallback and recovery, avoiding weak bypass routes that attackers exploit.
Expected outcome
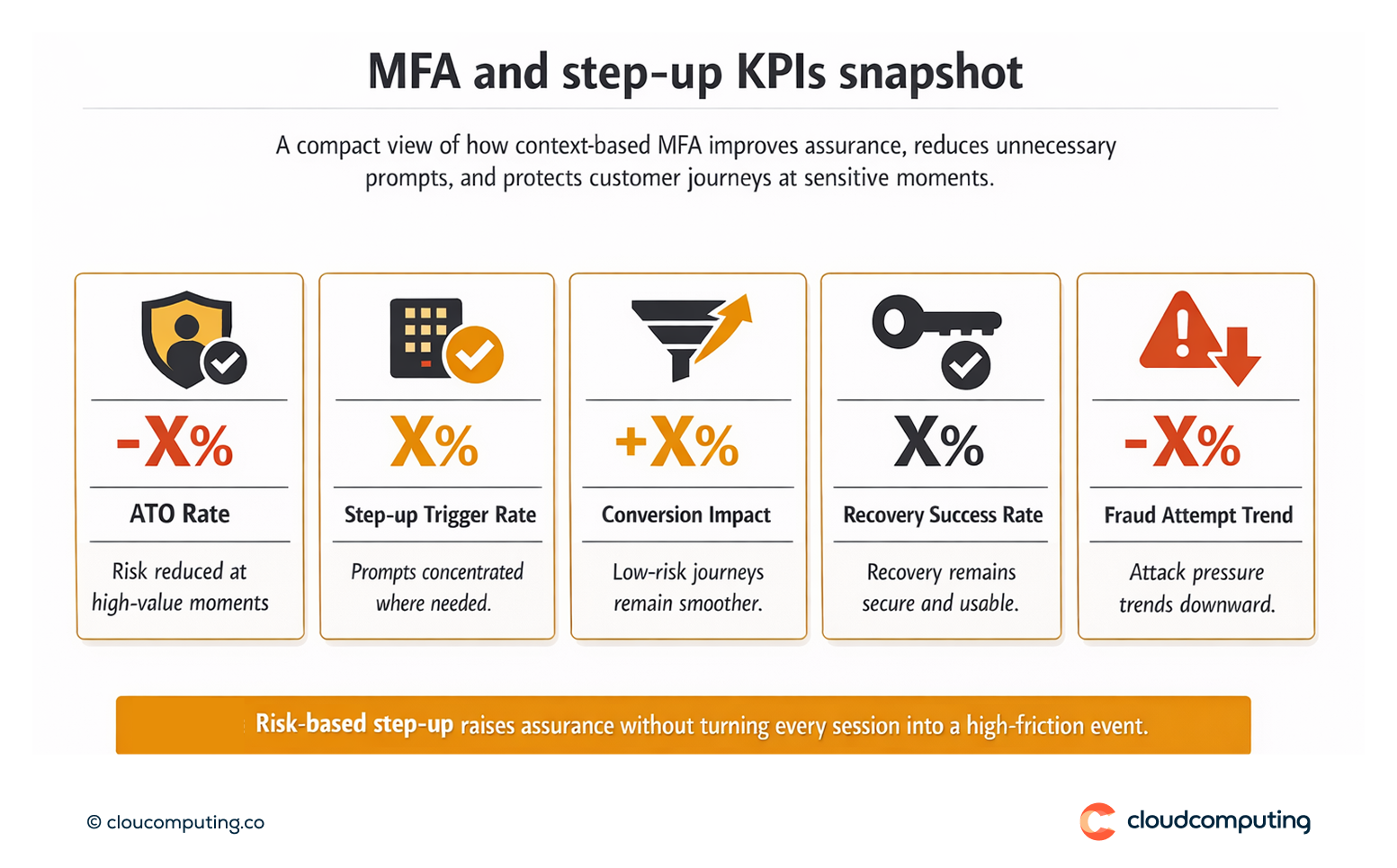
- Reduced account takeover risk by raising assurance when it matters
- Higher conversion compared to blanket MFA by limiting prompts to high-risk moments
- More consistent enforcement across channels and customer journeys
- Better customer trust through predictable, well-designed security moments
Quick Answers
What is step-up authentication in CIAM?
Additional verification triggered during sensitive actions or high-risk contexts, rather than on every login.
Why does blanket MFA reduce conversion?
It adds friction at the wrong moments, especially in sign-up and low-risk returning sessions.
How do you decide when to trigger step-up?
By combining action sensitivity with risk signals such as device posture, location anomalies, and behavioural indicators.
