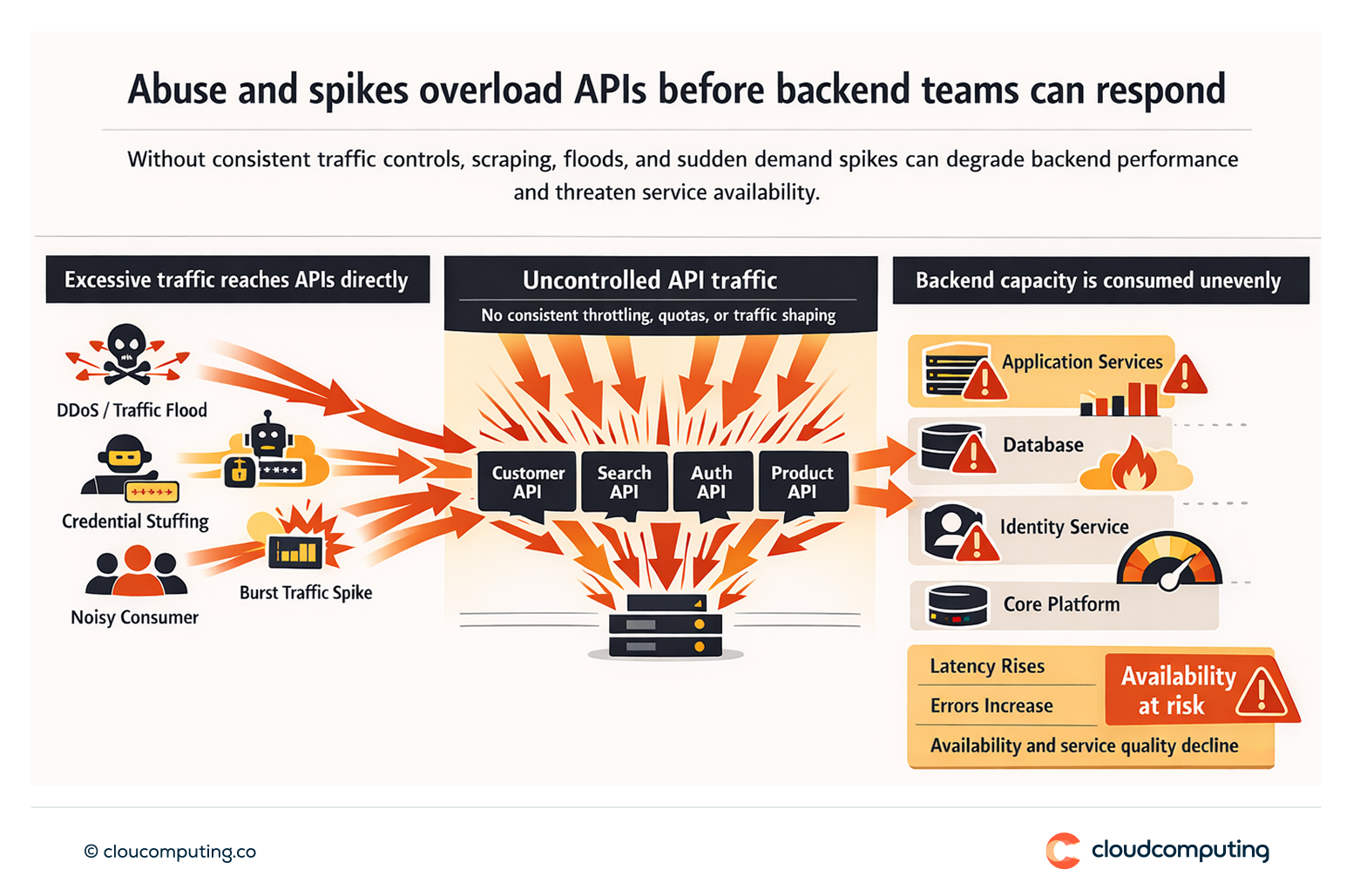
The Problem
APIs are abused and overloaded. Traffic spikes, scraping, and automated attacks degrade service quality and can take down backends.
Without consistent throttling and quotas, critical services are vulnerable to noisy neighbours and malicious activity.
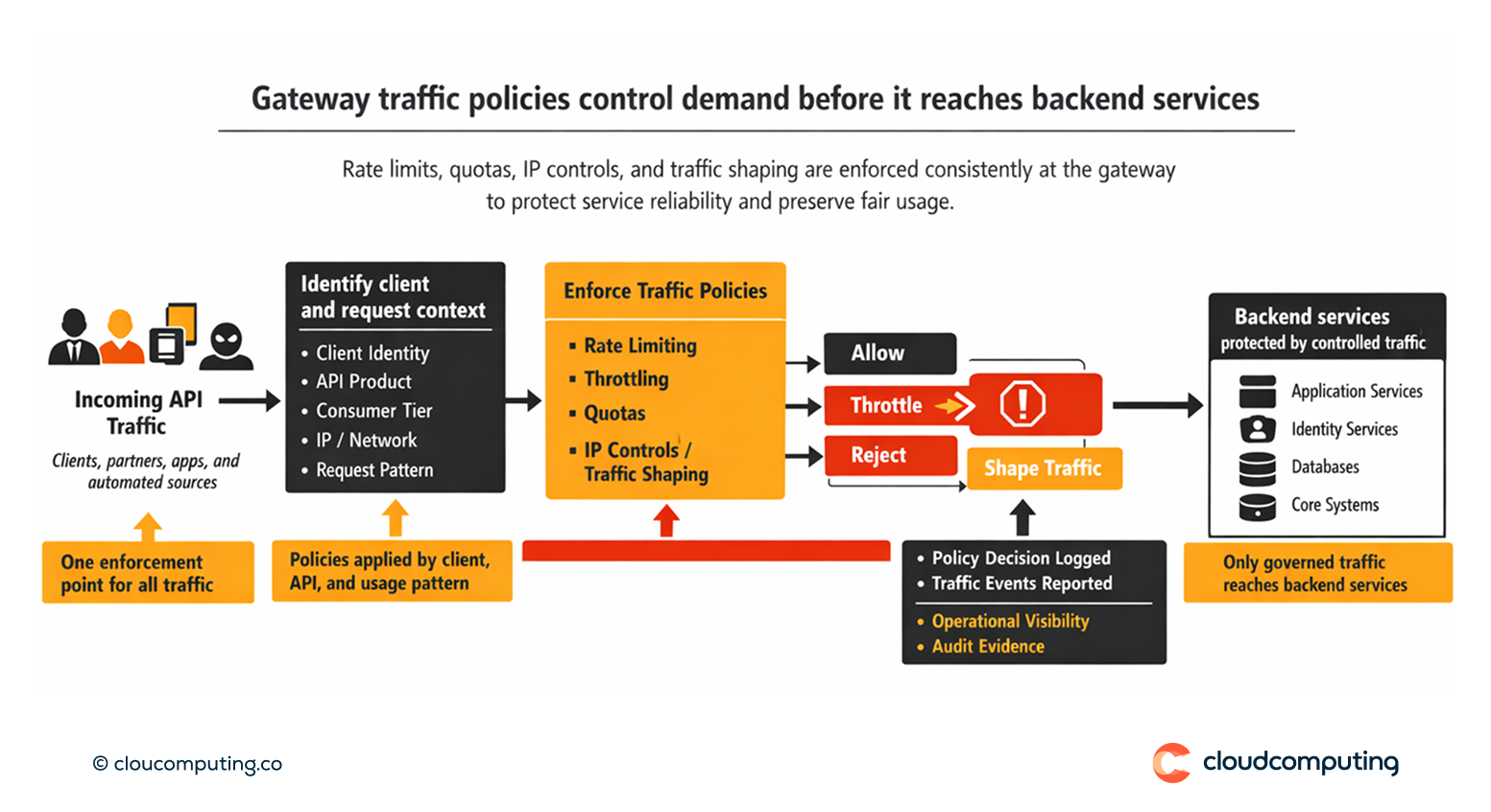
How we solve it: Apply rate limiting, throttling, quotas, IP controls, and traffic shaping at the gateway to protect backends.
We implement traffic controls as standard policies to prevent abuse and preserve service reliability.
- Rate limiting and throttling
Define per-client and per-API limits aligned to capacity and business priority. - Quotas and segmentation
Apply quotas by consumer segment, API product, or partner tier. - IP allow/deny and traffic shaping
Enforce network controls and shape traffic to protect critical services.
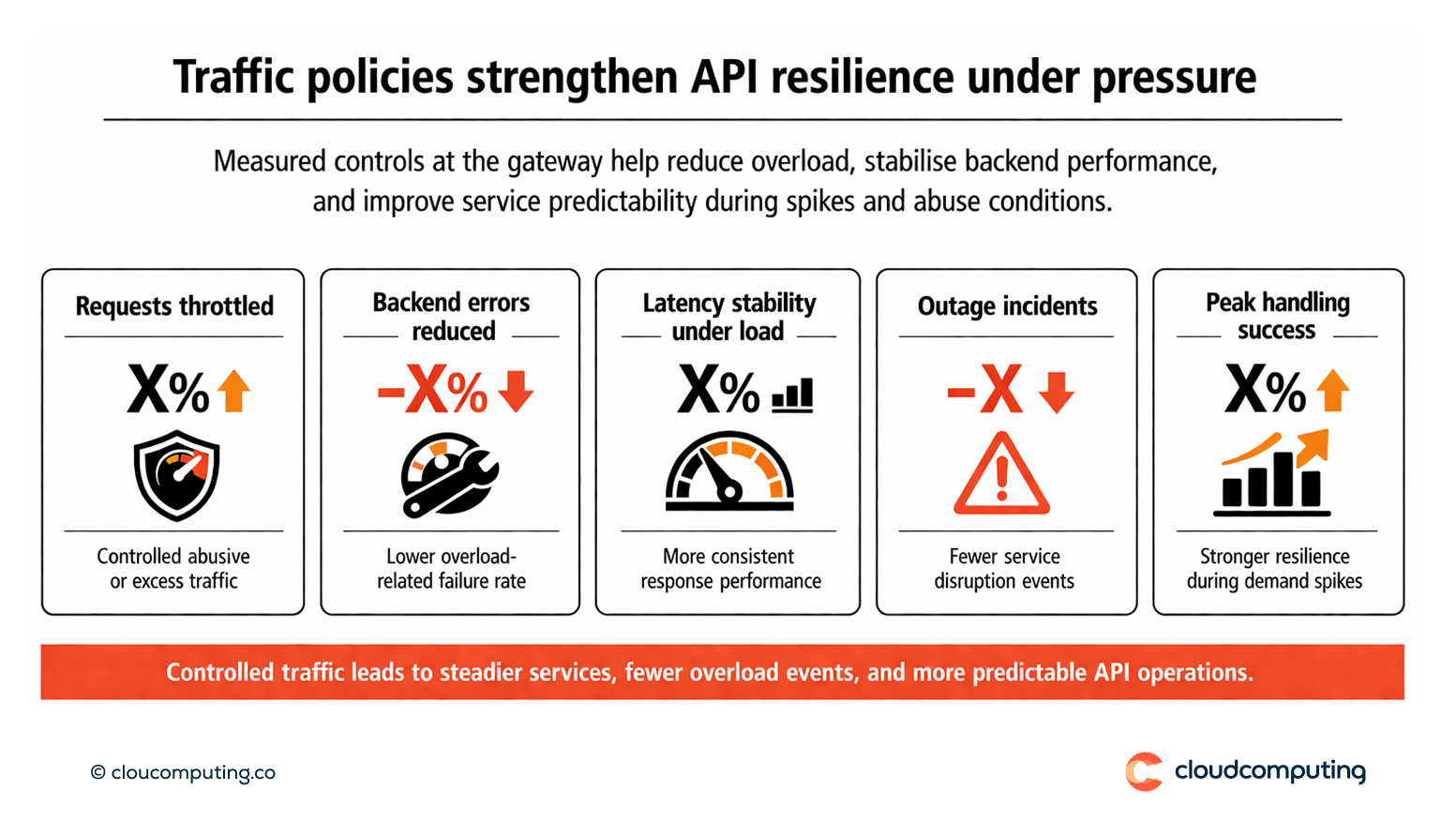
Expected outcome
- Better resilience under spikes and abuse conditions
- Protected backends through controlled traffic and fair usage
- Fewer outages by preventing overload and degradation
- Improved operational predictability through measurable traffic policies
Quick Answers
What does rate limiting protect against?
Overload from spikes and abusive traffic that can degrade services.
How do quotas help?
They enforce fair usage and align consumption to subscription tiers or partner agreements.
Why apply controls at the gateway?
It provides consistent enforcement without requiring changes in every backend service.
