The Problem
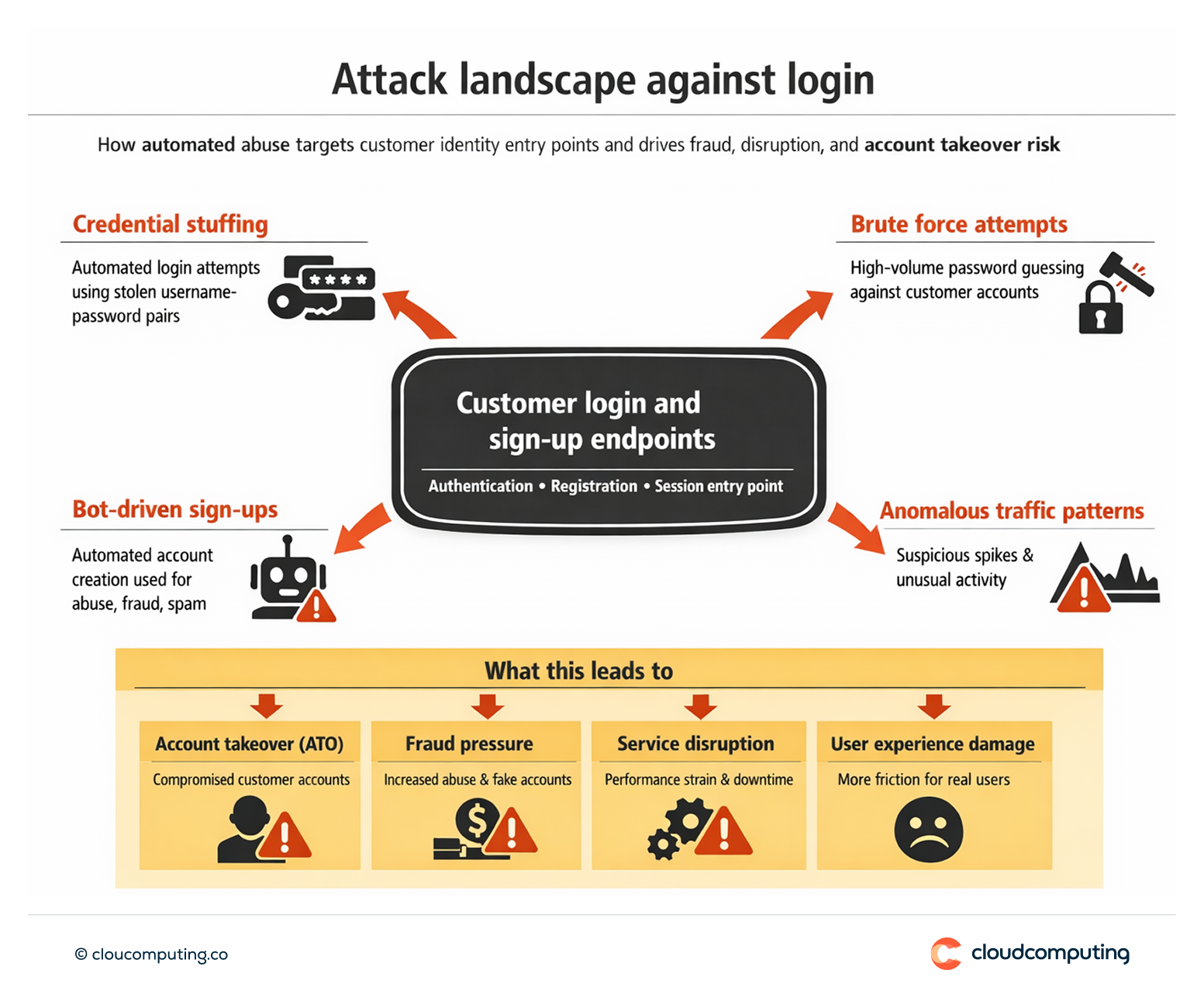
Customer login and sign-up endpoints are constantly targeted by automated abuse: credential stuffing, bot-driven account creation, brute force attempts, and anomalous traffic patterns.
When protections are inconsistent, attackers exploit weak points to increase fraud, overwhelm operations, and degrade user experience.
Teams then respond reactively, tuning controls after incidents rather than reducing exposure proactively.
How we solve it: Configure attack protection controls and response patterns to reduce automated abuse without harming legitimate users.
We implement and tune attack protection capabilities so automated attacks are detected and mitigated while legitimate customer access remains reliable.
- Baseline protections and enforcement
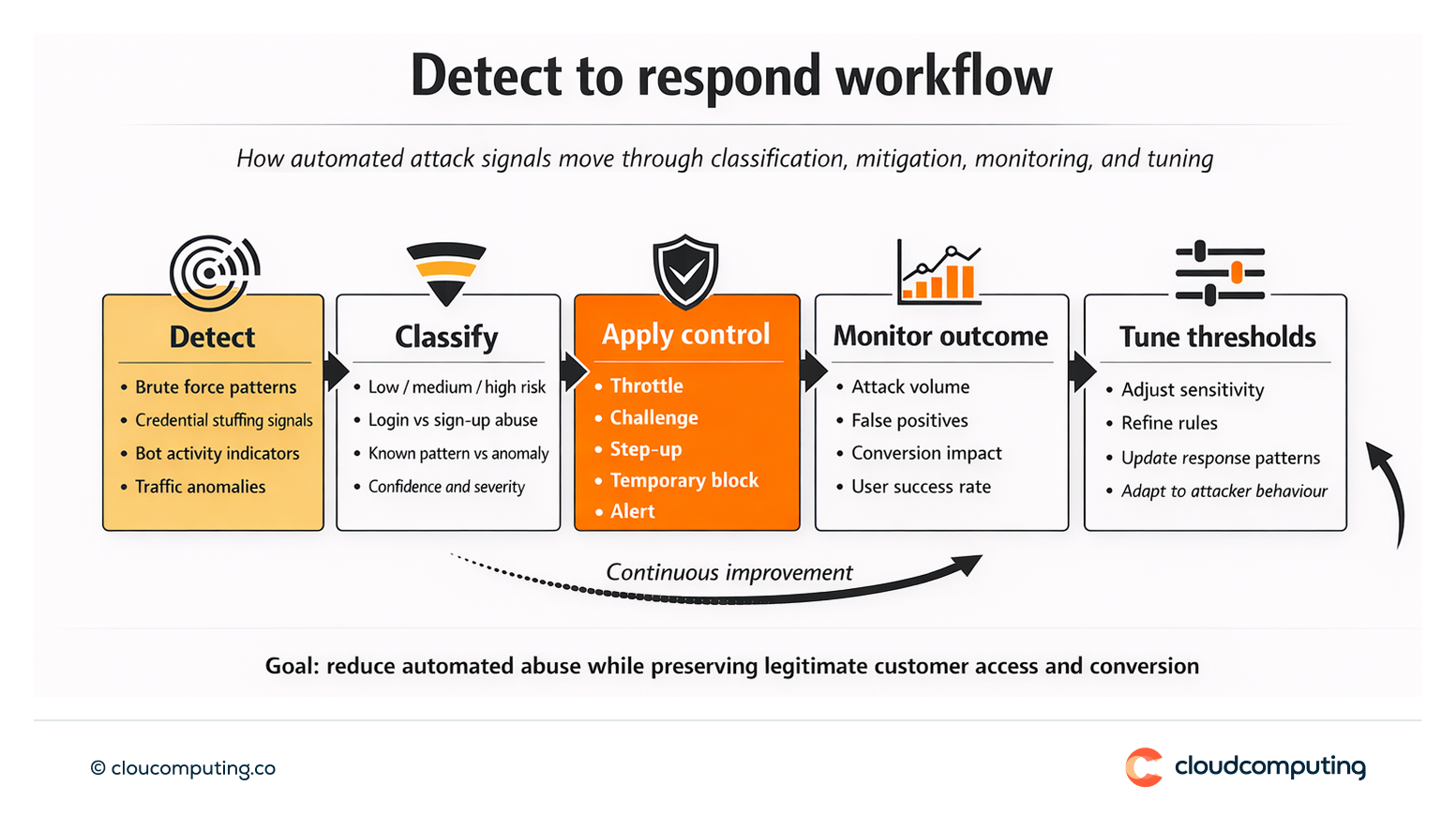
We configure brute force protections, anomaly detection patterns, and bot mitigation controls aligned to your threat profile. - Risk-aligned response patterns
We define responses that match risk: throttling, challenges, step-up requirements, temporary blocks, and alerting—avoiding blunt controls that damage conversion. - Monitoring and tuning
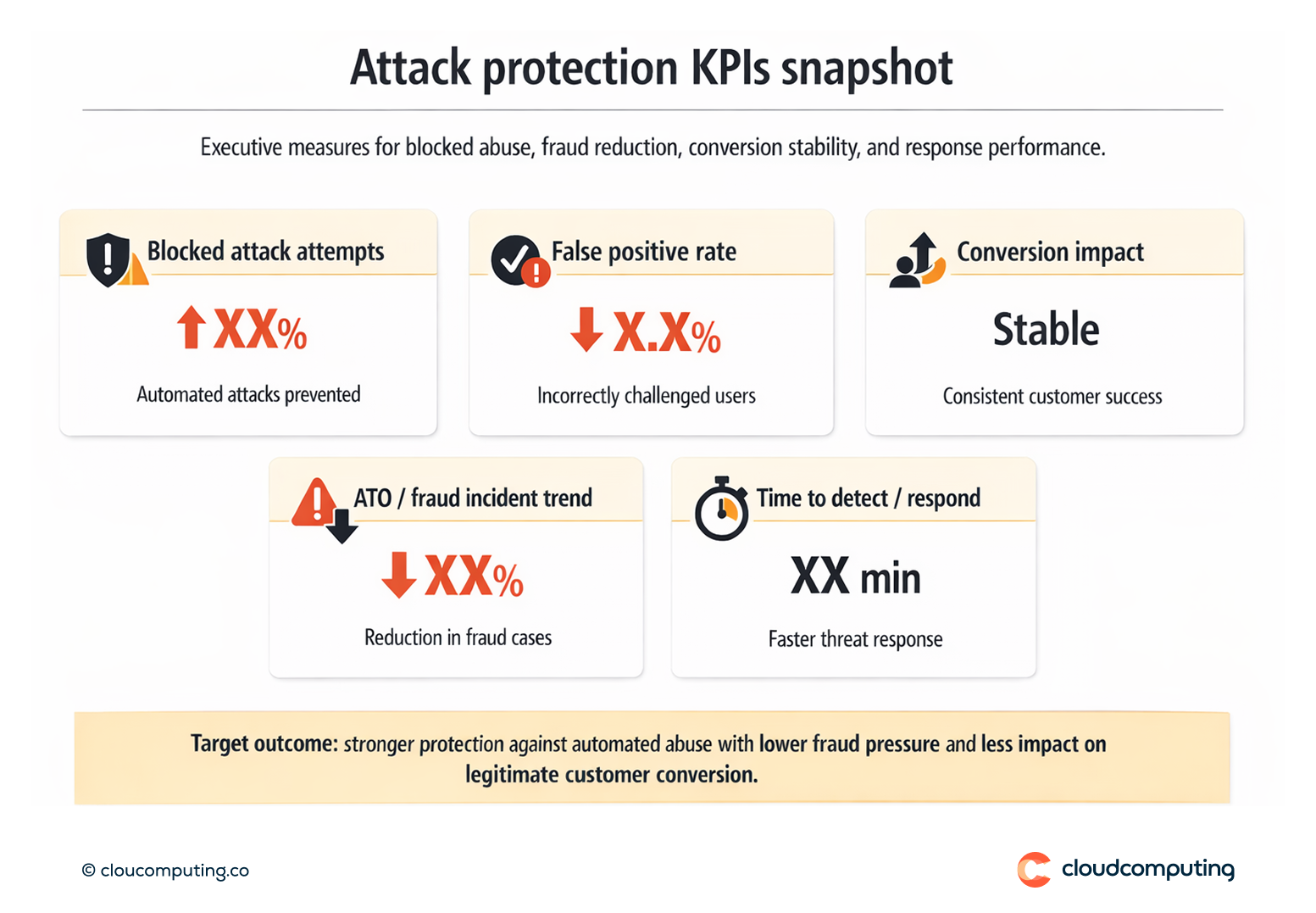
We track key signals (attack volume, false positives, conversion impact) and tune thresholds so protections remain effective as attacker behaviour changes. - Operational playbooks
We establish incident response and escalation patterns so teams can respond quickly when attack pressure spikes.
Expected outcome
- Fewer automated attacks reaching login and sign-up journeys
- Reduced fraud pressure from credential stuffing and bot-driven abuse
- Improved platform resilience during spikes in anomalous traffic
- More stable conversion by reducing blunt controls and tuning responses to risk
Quick Answers
What is credential stuffing?
Automated attempts to log in using stolen username/password combinations from other breaches.
Why do login endpoints attract constant attack pressure?
Because they are a direct path to account takeover, fraud, and monetisation, and automation makes attacks cheap at scale.
How do you protect endpoints without hurting conversion?
By applying risk-aligned controls (throttling, challenges, step-up) and tuning them based on observed impact and false positives.