The Problem
Different teams implement authentication and authorisation differently.
Weak links emerge through inconsistent token validation, missing scopes, lack of mutual TLS, or inconsistent JWT handling.
Attackers target the weakest API path, and security teams struggle to prove uniform controls.
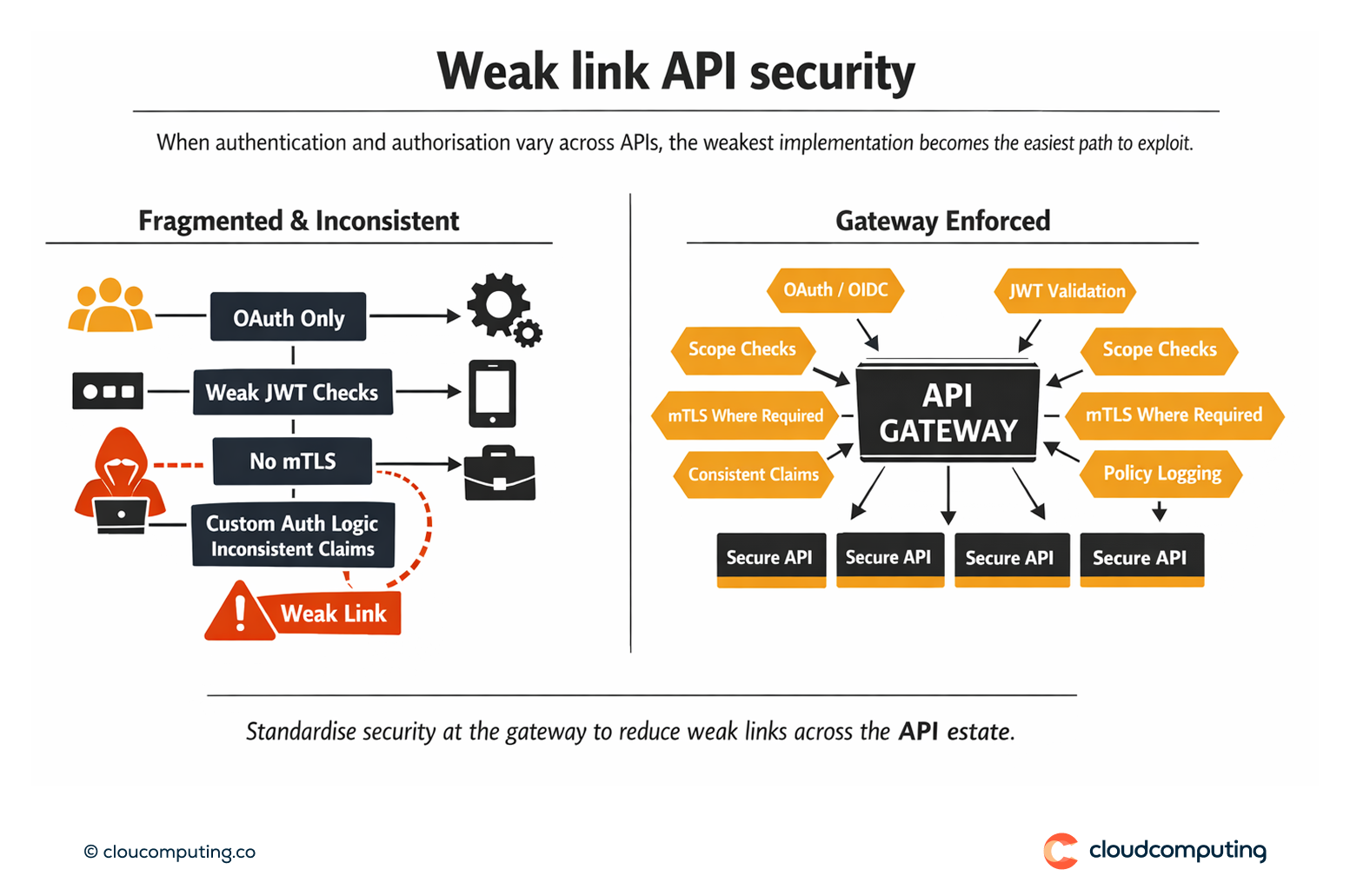
How we solve it: Standardise security policies at the gateway with consistent enforcement (OAuth/OIDC, mTLS, JWT validation).
We implement security controls as gateway policies so authentication and validation are consistent across APIs regardless of implementation.
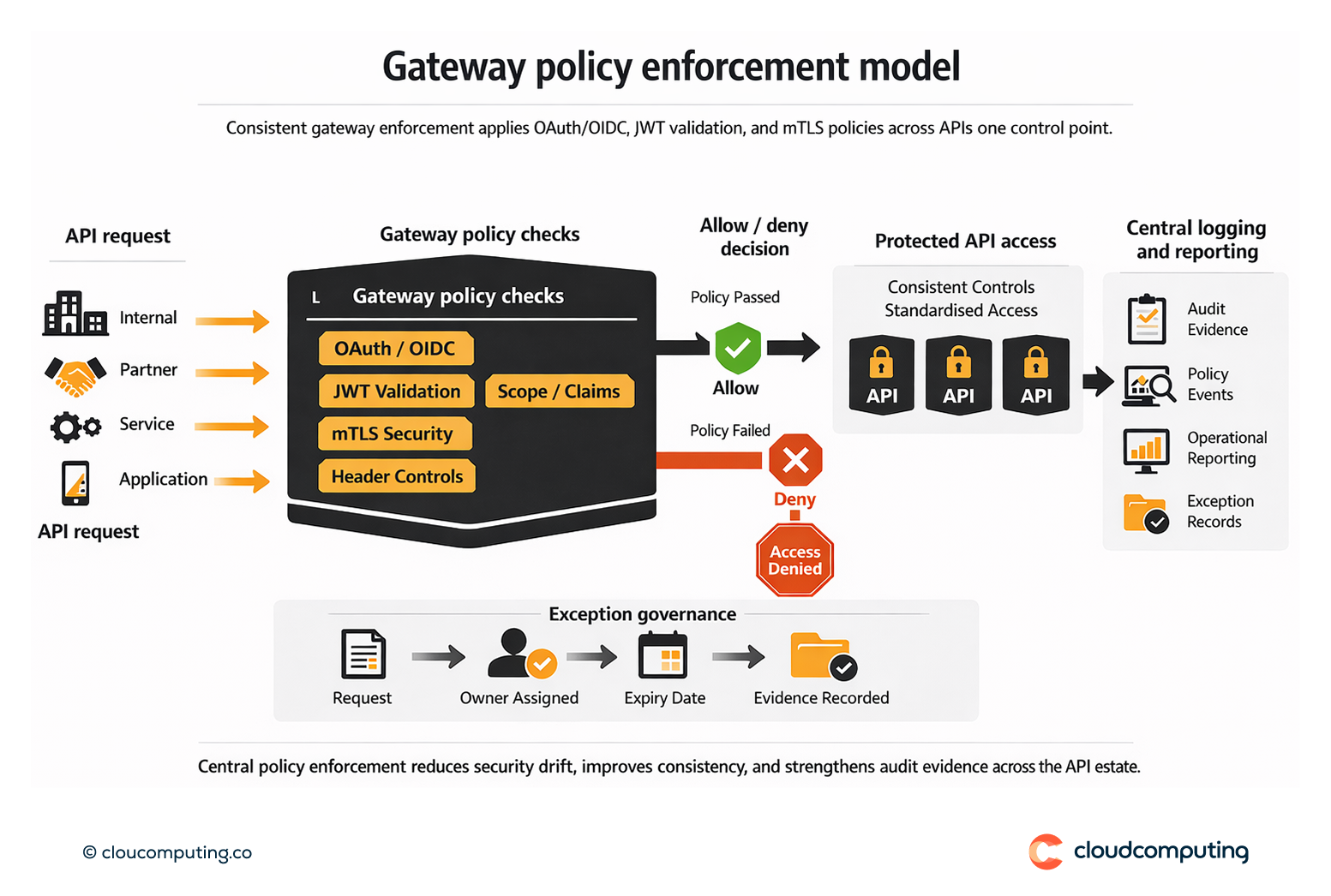
- Security baseline definition
Define required controls for API classes (internal, partner, public) including token validation and transport controls. - Gateway policy enforcement
Enforce OAuth/OIDC, JWT validation, mTLS where needed, and consistent header and claim handling. - Exception governance
Control deviations through time-bound exceptions with evidence and ownership.
Expected outcome
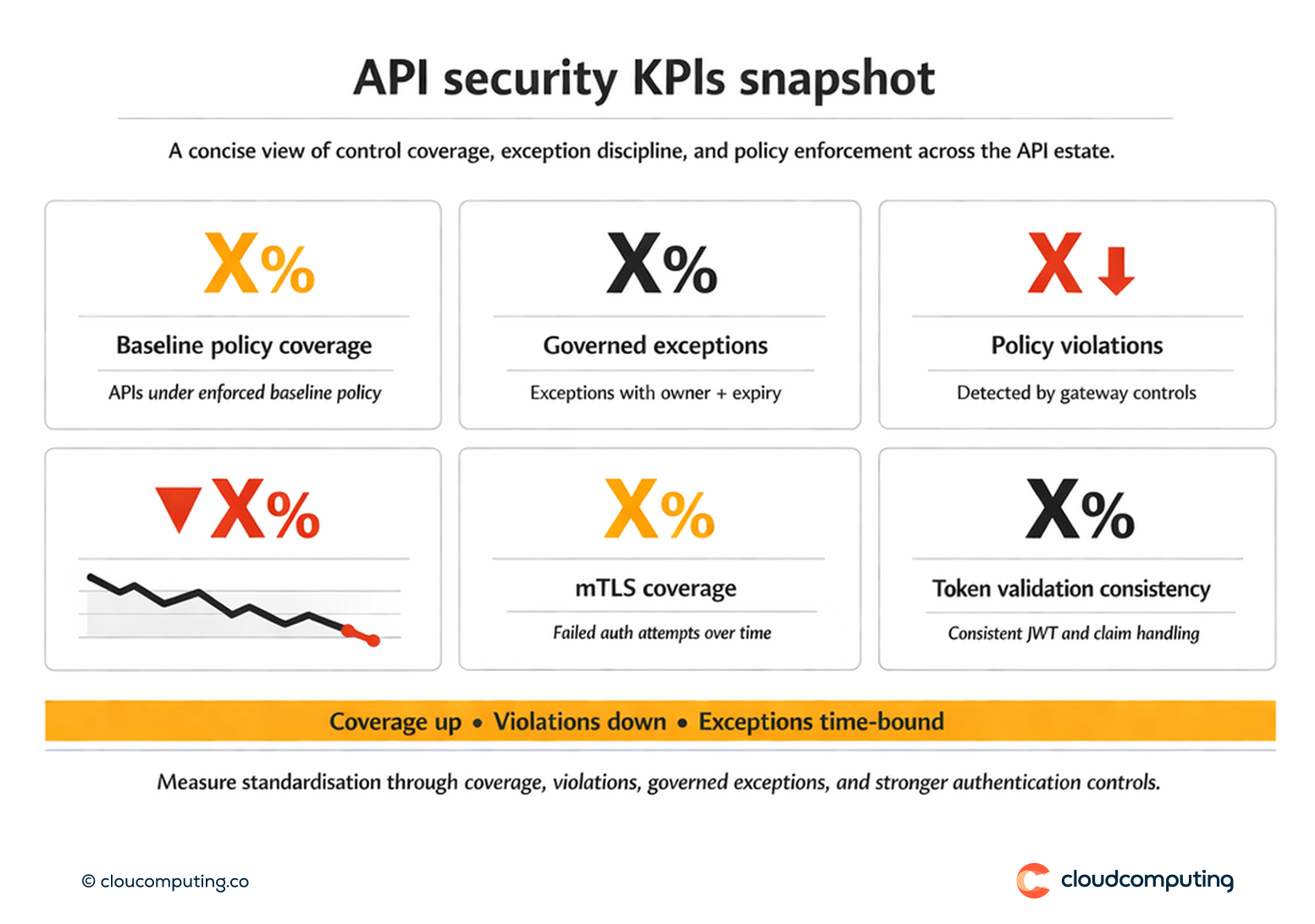
- Uniform security posture across APIs through consistent gateway enforcement
- Fewer misconfigurations by removing bespoke implementations
- Reduced breach paths by closing weak links across the API estate
- Improved audit defensibility through central policy evidence
Quick Answers
Why is inconsistent API security risky?
Attackers exploit the weakest API path, and inconsistent controls create hidden breach routes.
What does gateway enforcement solve?
It standardises authentication and validation regardless of how APIs are implemented.
When is mTLS relevant?
For high-assurance service-to-service or partner connections that require strong transport identity.