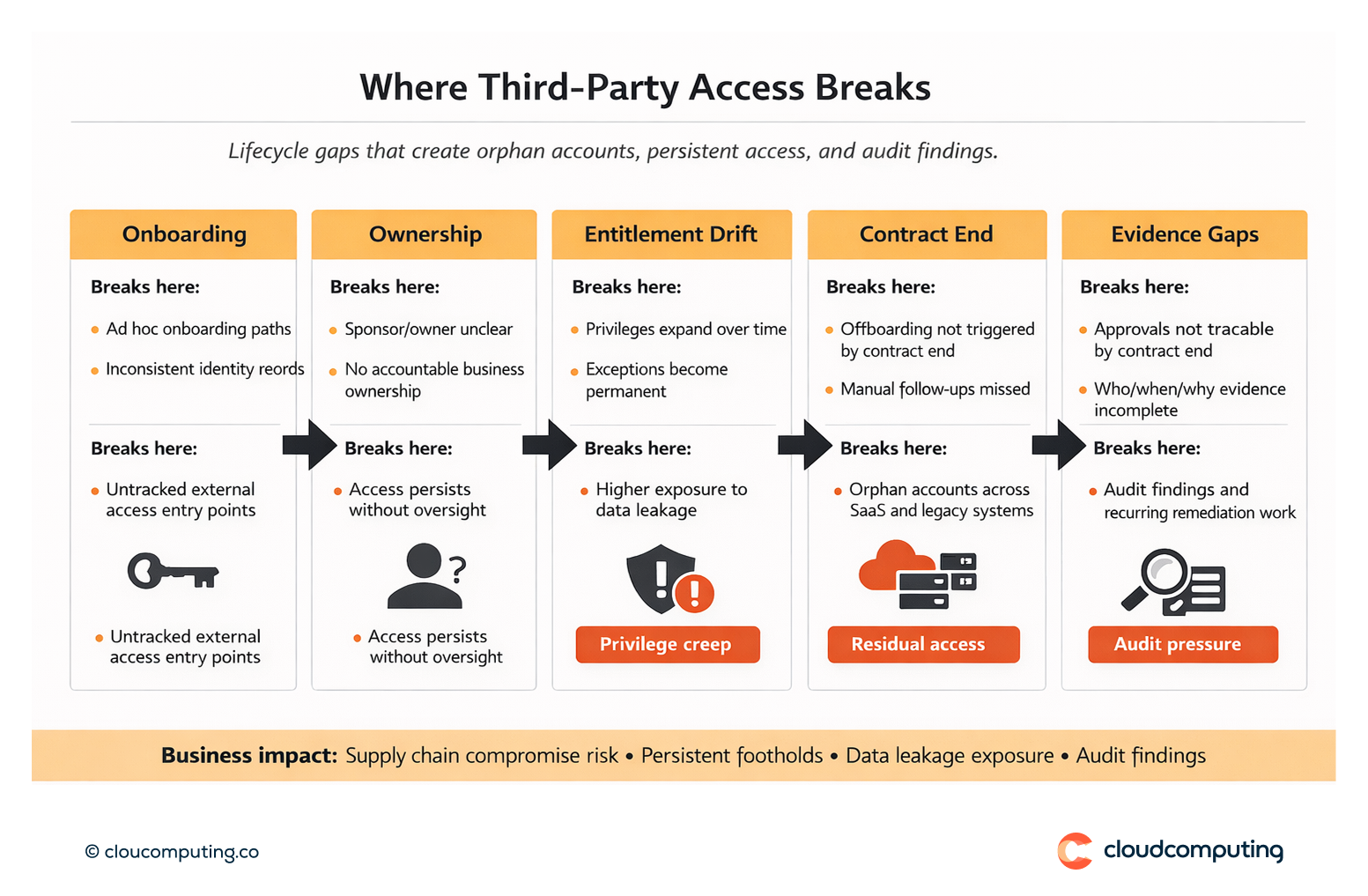
The Problem
Third-party access often grows faster than governance.
External users are onboarded through ad hoc processes, ownership is unclear, and access persists after contracts end. Accounts become orphaned across SaaS, shared platforms, and legacy systems.
Oversight is limited, which increases exposure to supply chain compromise, data leakage, and audit findings – especially where third parties touch regulated systems or sensitive data.
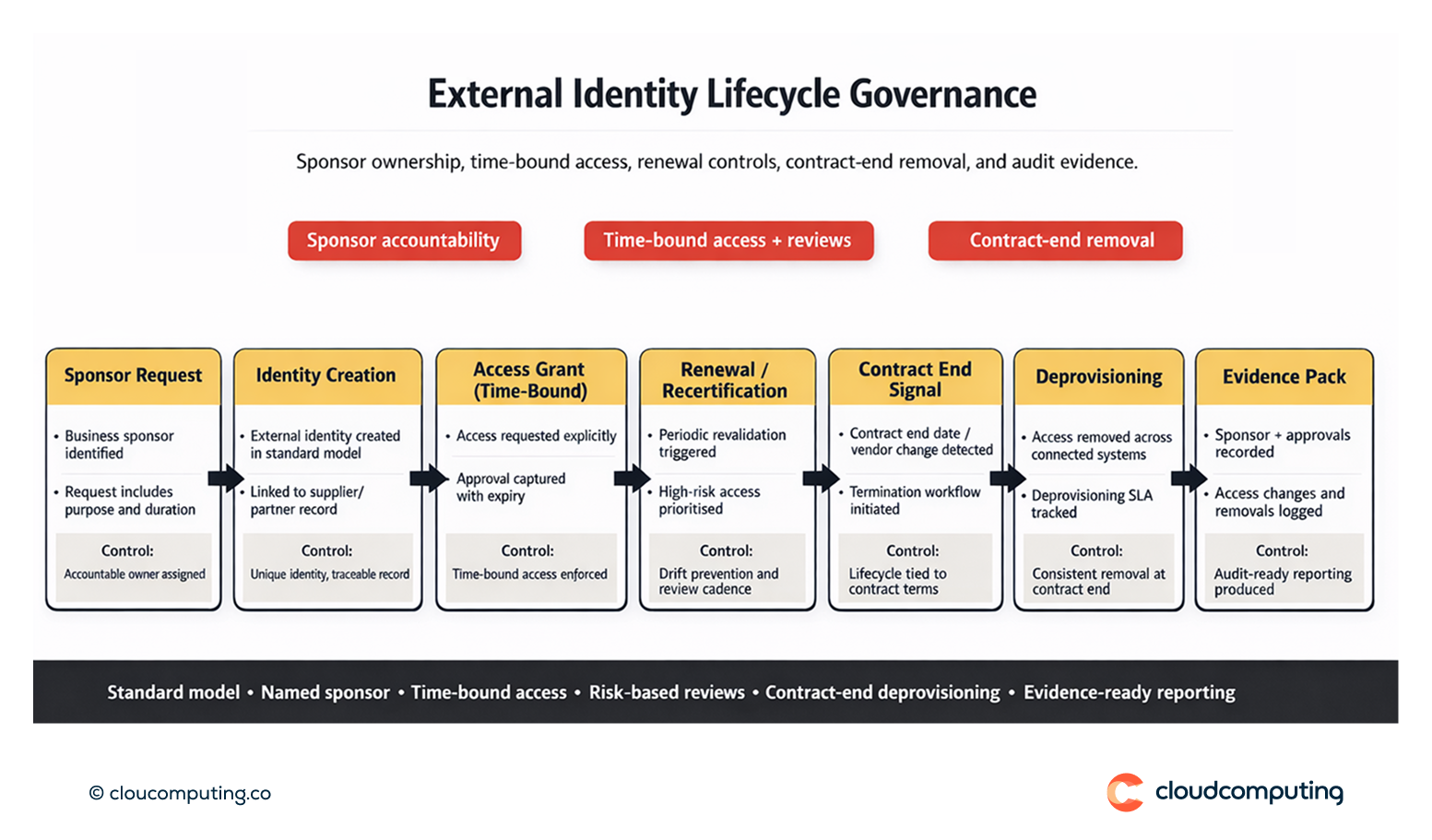
How we solve it: Lifecycle and risk governance for external identities.
We establish external identity lifecycle controls, link access to sponsorship and contract terms, and apply risk-based governance so third-party access is time-bound, traceable, and auditable.
- External identity model and sponsorship
We define a standard identity model for non-employees (partners, suppliers, contractors) and enforce a sponsor/owner model so every external identity has accountable business ownership. - Onboarding and offboarding tied to contract signals
We align lifecycle events to contract start/end dates or vendor records where available, enabling predictable onboarding, renewal, and termination flows – without relying on manual follow-ups. - Policy-driven access with time bounds
We implement request and approval controls that make third-party access explicit: what is being granted, for how long, under which conditions, and with mandatory expiry for elevated access. - Risk-based review and monitoring
We prioritise governance for high-impact third-party access (privileged access, sensitive apps, critical data) with focused certification campaigns and evidence-ready reporting. - Operational controls and audit evidence
We standardise exception handling, renewal cycles, deprovisioning SLAs, and reporting so the organisation can demonstrate control consistently, not only during audits.
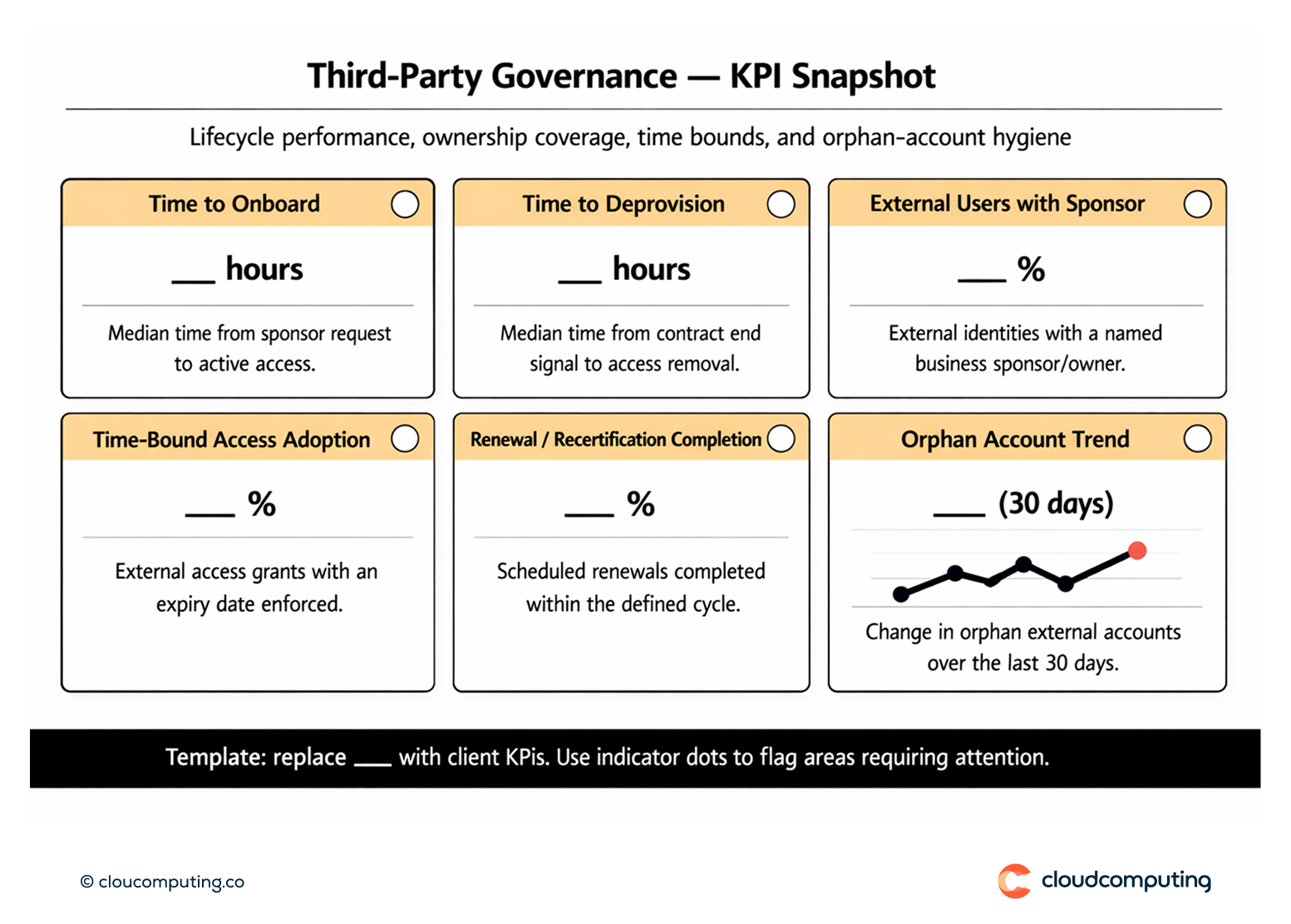
Expected outcome
- Faster onboarding and offboarding with standardised workflows and clear ownership
- Lower third-party risk through time-bound access, targeted reviews, and consistent removal at contract end
- Fewer orphan accounts across connected systems and reduced entitlement drift
- Stronger audit readiness with traceable approvals and repeatable evidence
Quick Answers
What is non-employee governance?
A set of controls that manage external identities across their lifecycle—onboarding, access changes, renewals, and termination—so access remains owned, time-bound, and auditable.
Why is third-party access high risk?
Because access often outlives contracts, ownership is unclear, and external accounts can become persistent footholds into systems and data.
What does strong third-party governance enforce?
Sponsor accountability, time-bound access, consistent offboarding at contract end, and evidence that proves control.
