The Problem
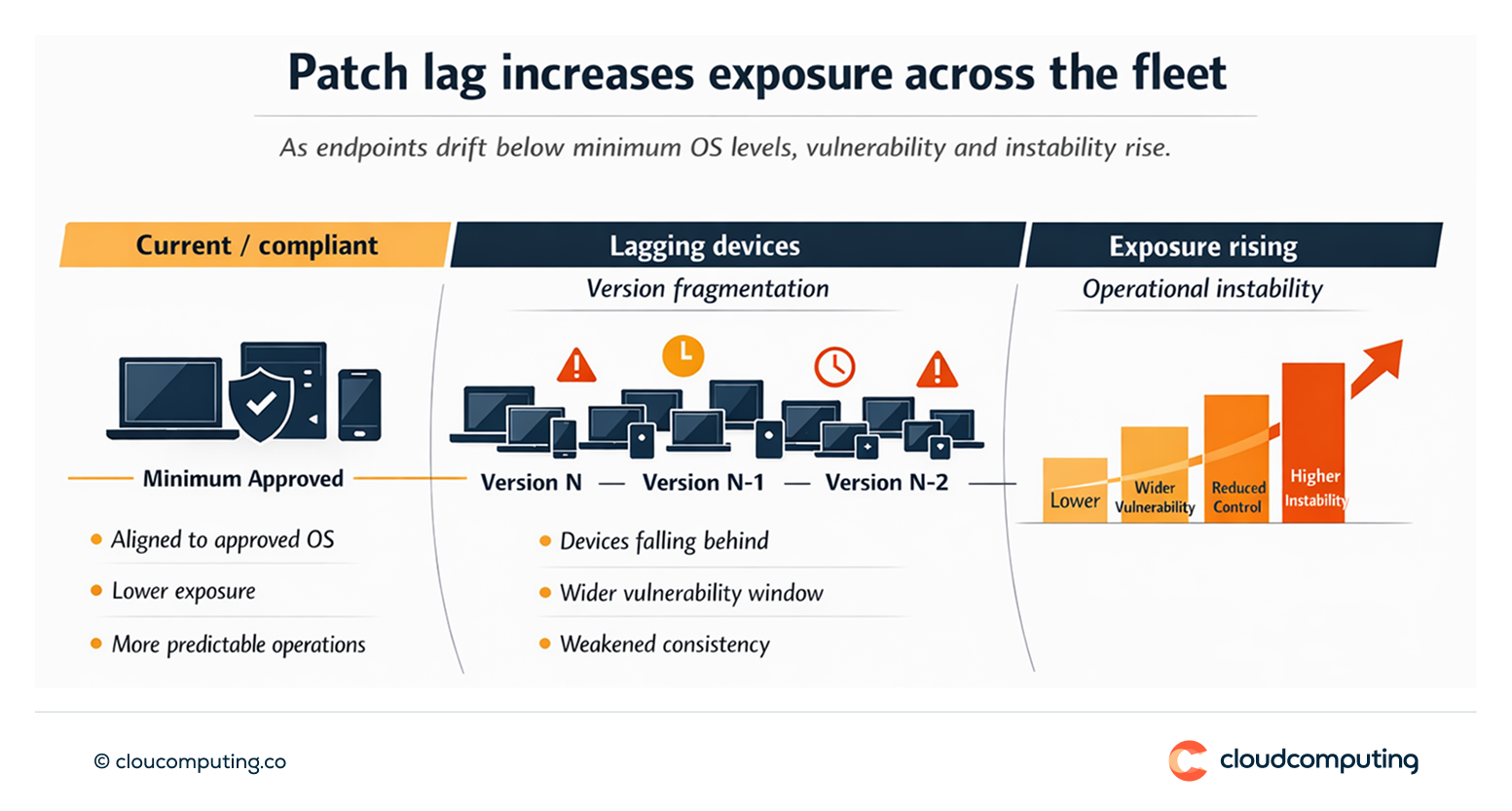
Delayed OS updates increase security exposure and operational instability.
Without a structured update strategy, endpoints fragment across OS versions, vulnerabilities persist, and changes land unpredictably.
Teams struggle to balance business continuity with minimum security baselines.
How we solve it: Define update rings, monitor adoption, and enforce minimum OS levels for predictable change and reduced exposure.
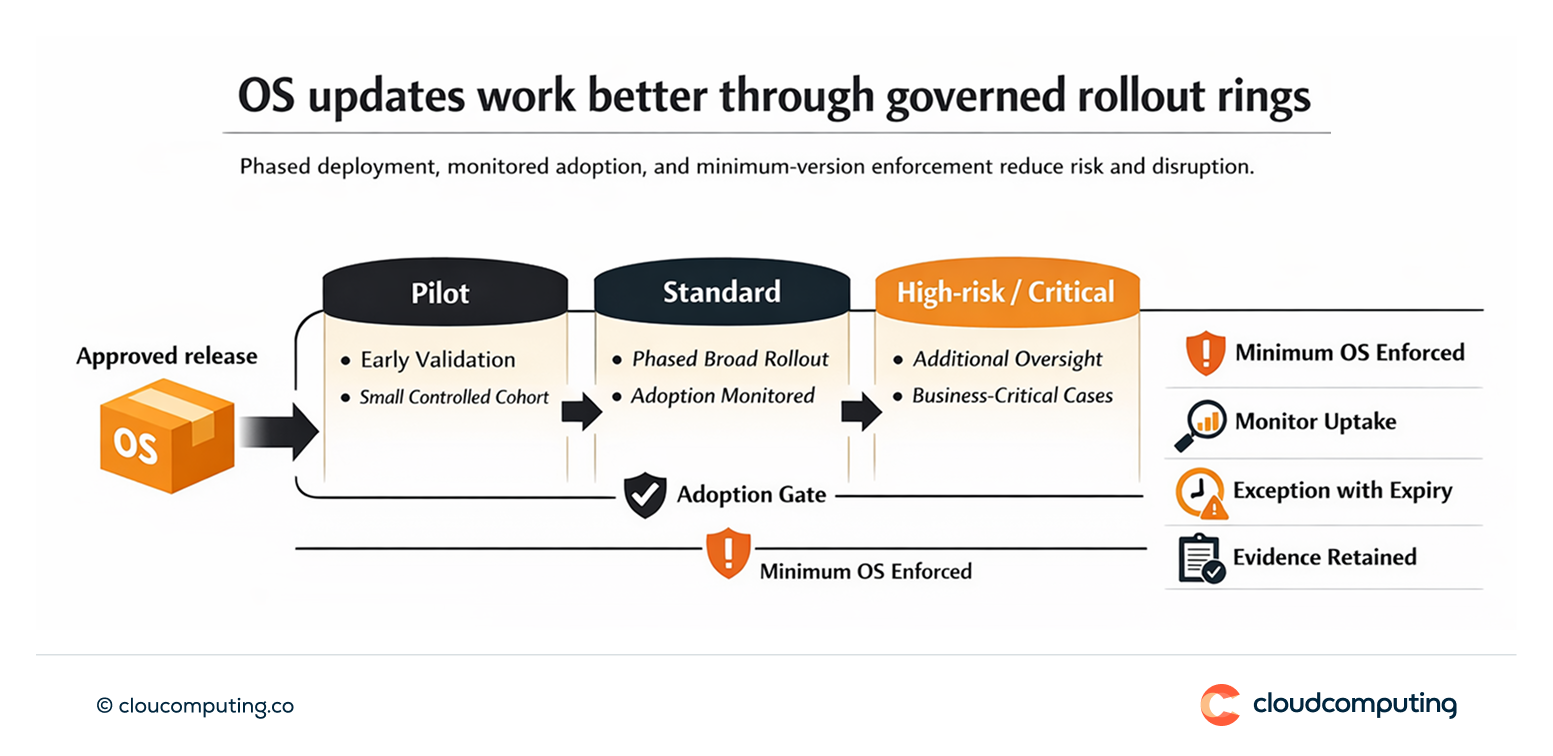
We implement an OS update governance model that balances stability with security requirements.
- Update rings and policies
We define pilot, standard, and high-risk rings with controlled rollout schedules. - Adoption monitoring and enforcement
We track uptake, identify lagging devices, and enforce minimum OS levels where required. - Exception governance
We manage exceptions with time bounds and documented risk acceptance, avoiding permanent lag.
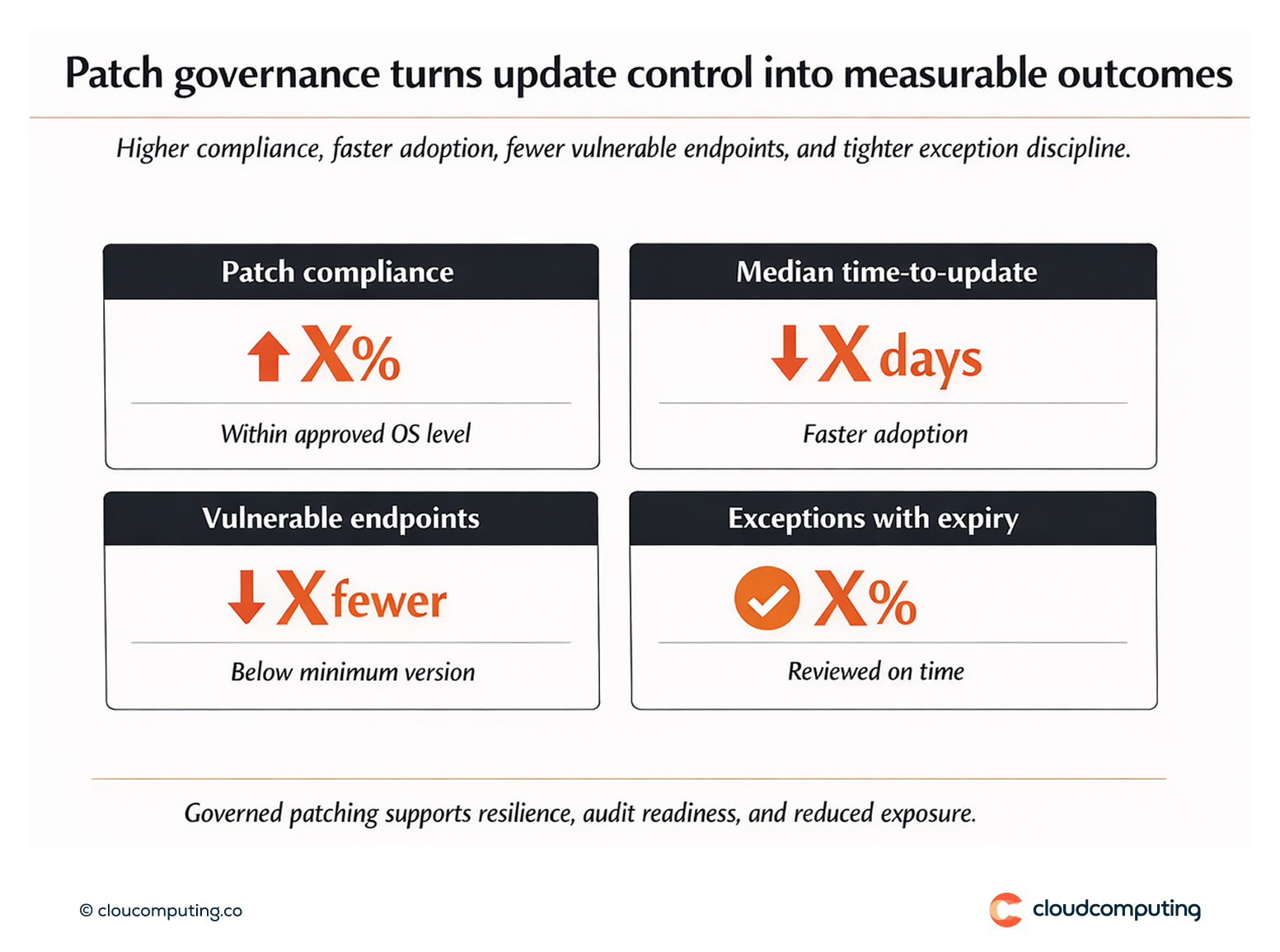
Expected outcome
- Fewer vulnerable endpoints by reducing patch lag and enforcing minimum versions
- Predictable change through controlled rollout rings
- Better resilience by reducing instability from ad hoc updates
- Clearer compliance posture through evidence of patch governance
Quick Answers
What are update rings?
Phased rollout groups that reduce disruption by validating updates before broad deployment.
Why enforce minimum OS levels?
Older OS versions increase vulnerability exposure and reduce the reliability of security controls.
How do you avoid business disruption?
By using pilots, staged deployment, and exception governance for critical edge cases.