The Problem
Device management and security tooling often operate in silos.
Baselines are inconsistent, telemetry is fragmented, and response actions are not coordinated.
This creates blind spots where risky configurations, compromised devices, or policy violations are not acted on quickly.
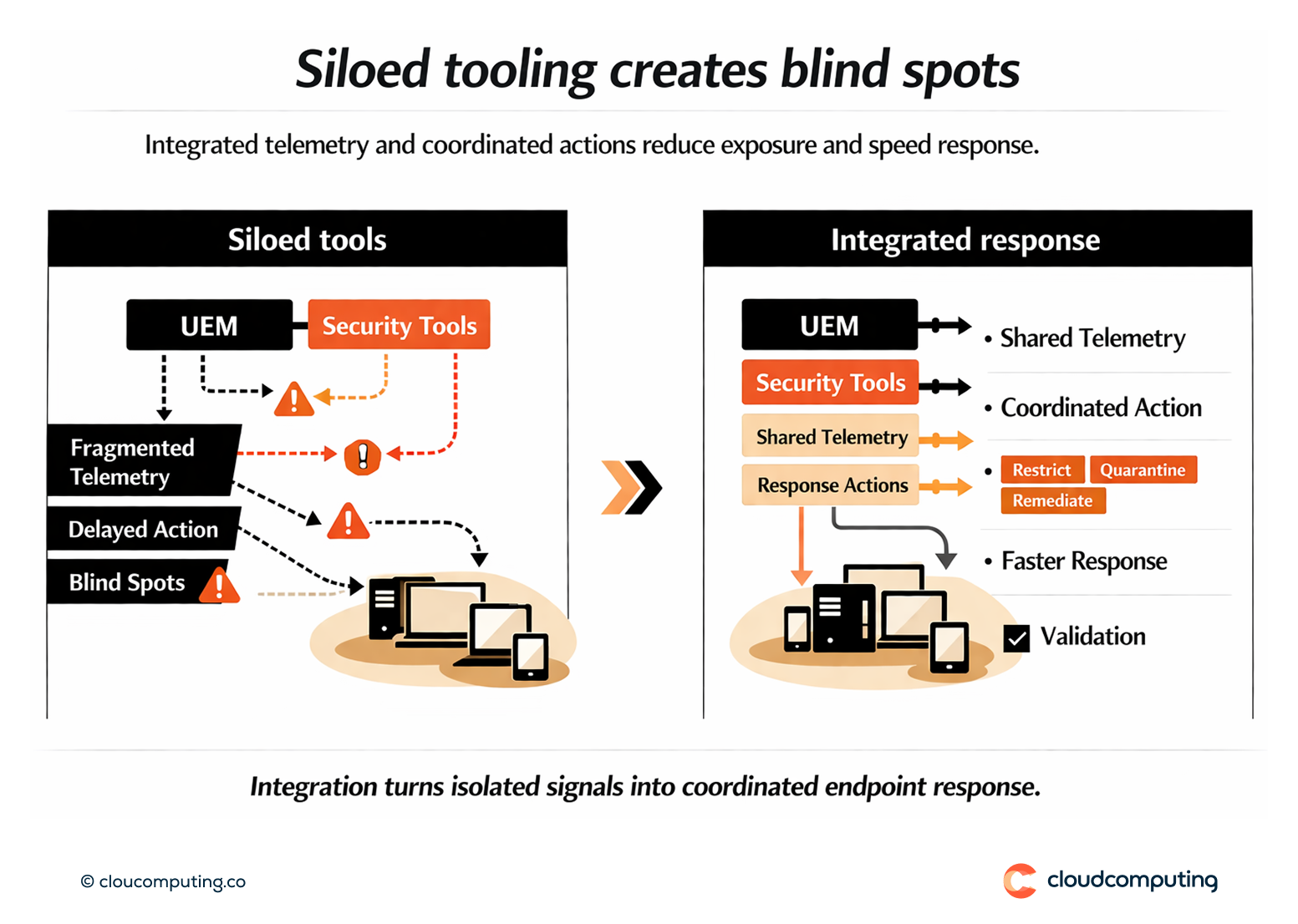
How we solve it: Align hardening baselines and integrate telemetry and actions with security tools to coordinate prevention and response.
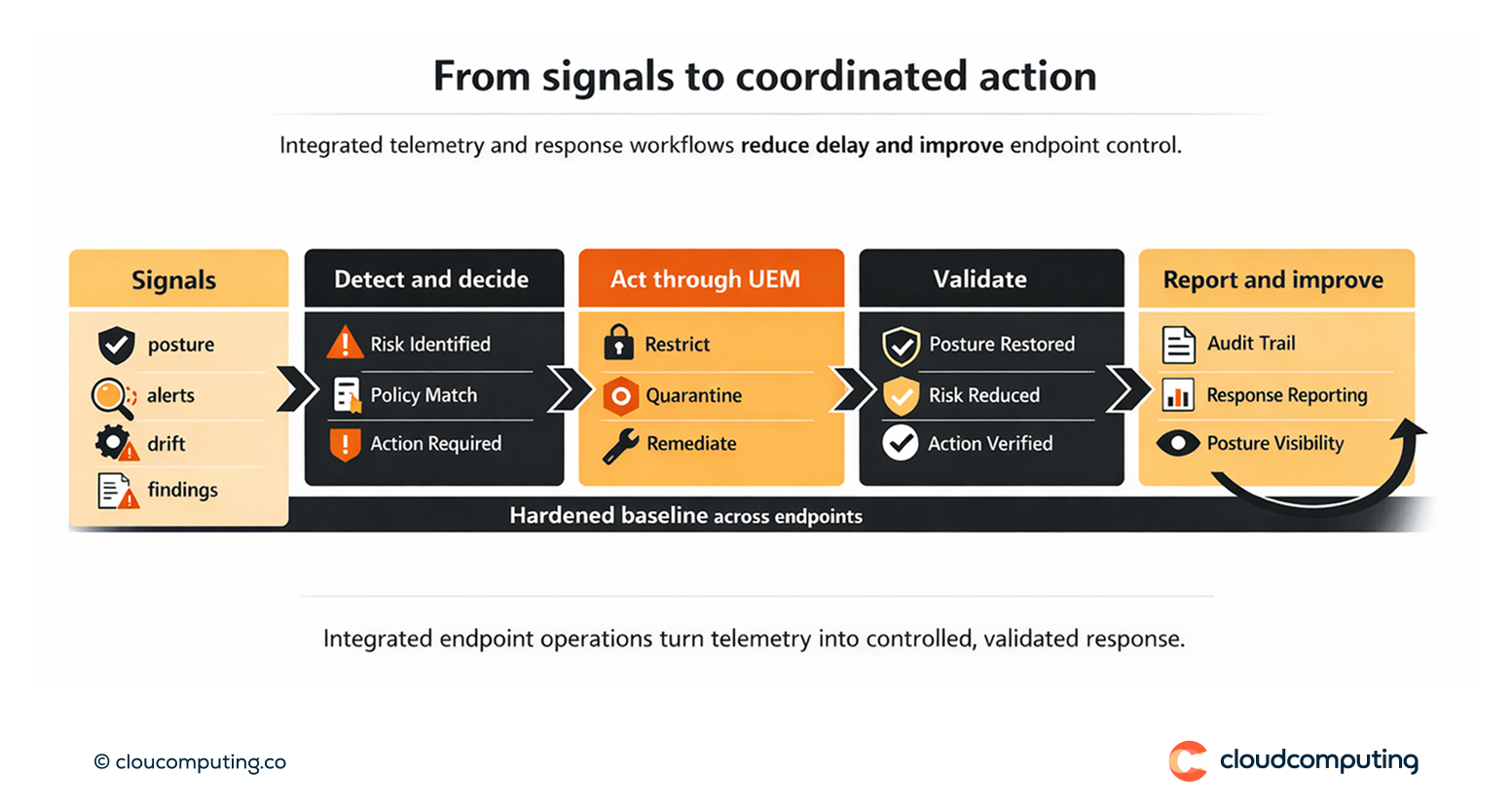
We implement a hardened baseline and integrate device posture with security operations workflows.
- Baseline hardening
We define baseline controls such as encryption, firewall settings, restrictions, and secure configurations. - Tool integration
We integrate telemetry and response actions with endpoint security tools to coordinate detection and remediation. - Coordinated response playbooks
We define response patterns such as quarantine, restrict access, trigger remediation, and escalate incidents.
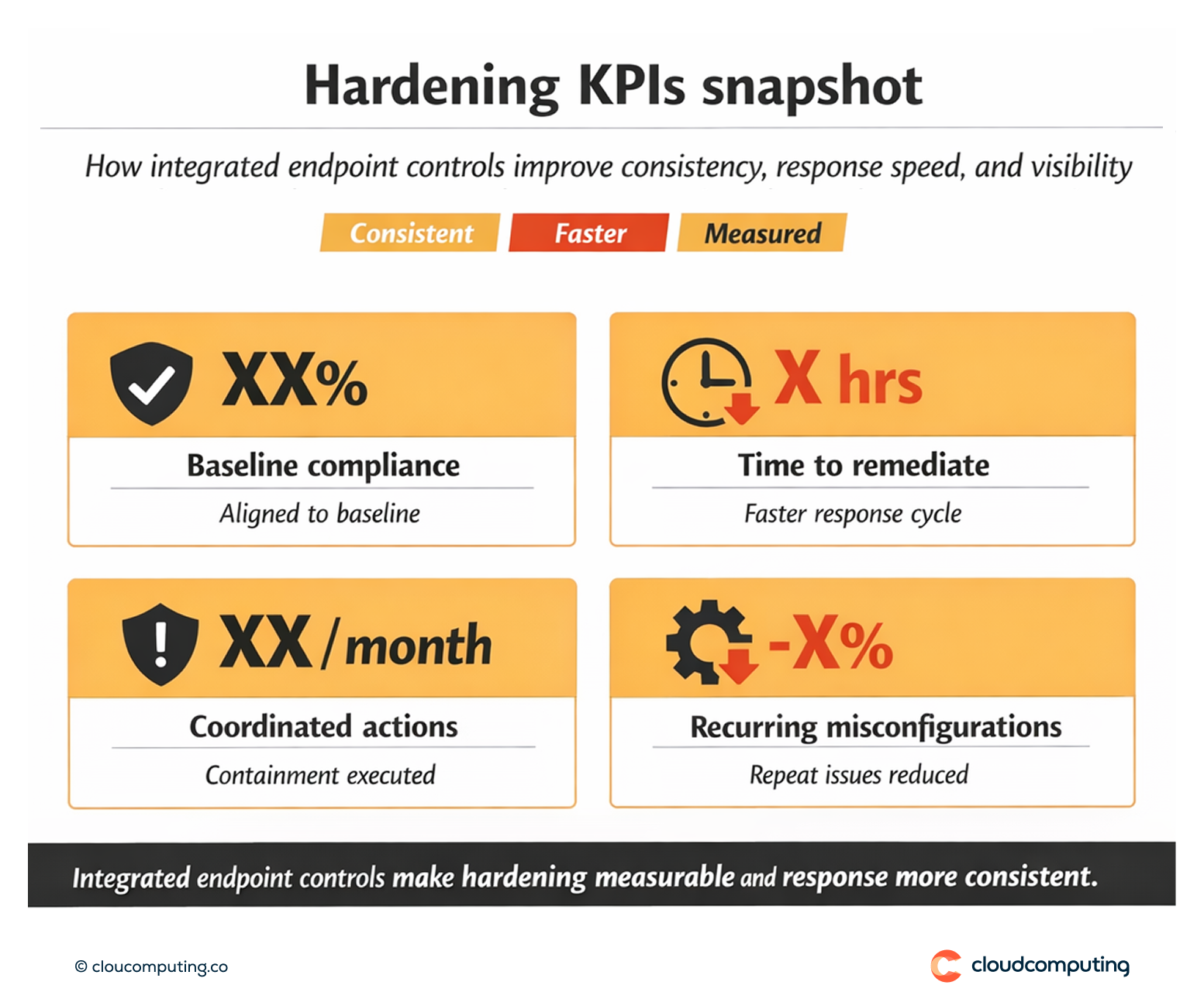
Expected outcome
- Fewer attack paths through consistent hardening and reduced configuration gaps
- Faster response via coordinated actions between UEM and security tools
- More consistent controls across endpoints and platforms
- Improved operational visibility with unified posture and response reporting
Quick Answers
What is endpoint hardening in device management?
Applying consistent baseline security settings across endpoints to reduce attack surface.
Why integrate UEM with security tools?
It enables coordinated detection and response, reducing blind spots and accelerating remediation.
What actions can be automated safely?
Restricting access, enforcing compliance settings, initiating guided remediation, and isolating high-risk devices under defined policies.
