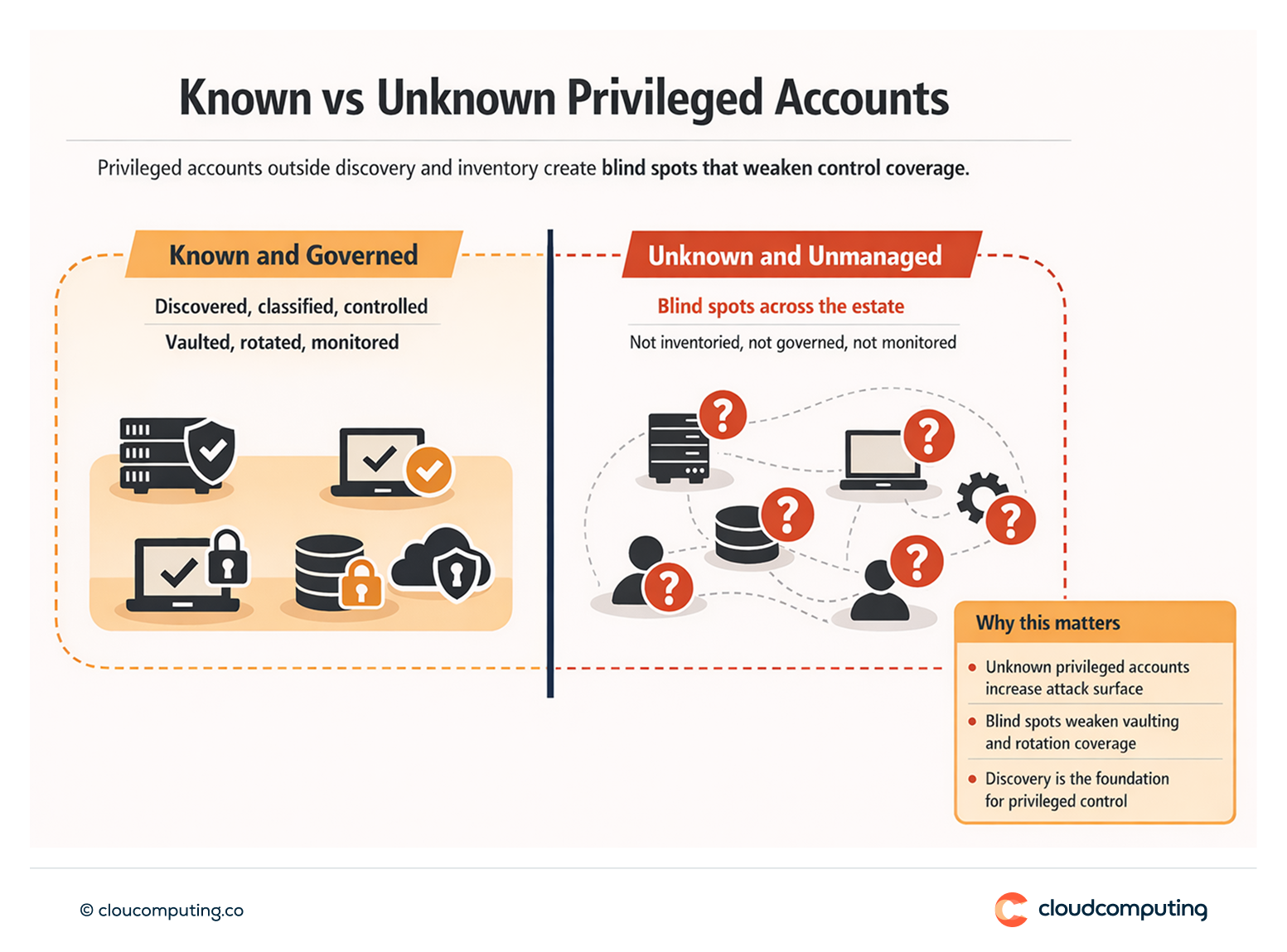
The Problem
Unknown privileged accounts remain unmanaged.
Local admins, machine accounts, service identities, and legacy admin accounts create blind spots that attackers exploit.
Without discovery and inventory, organisations cannot confirm control coverage.
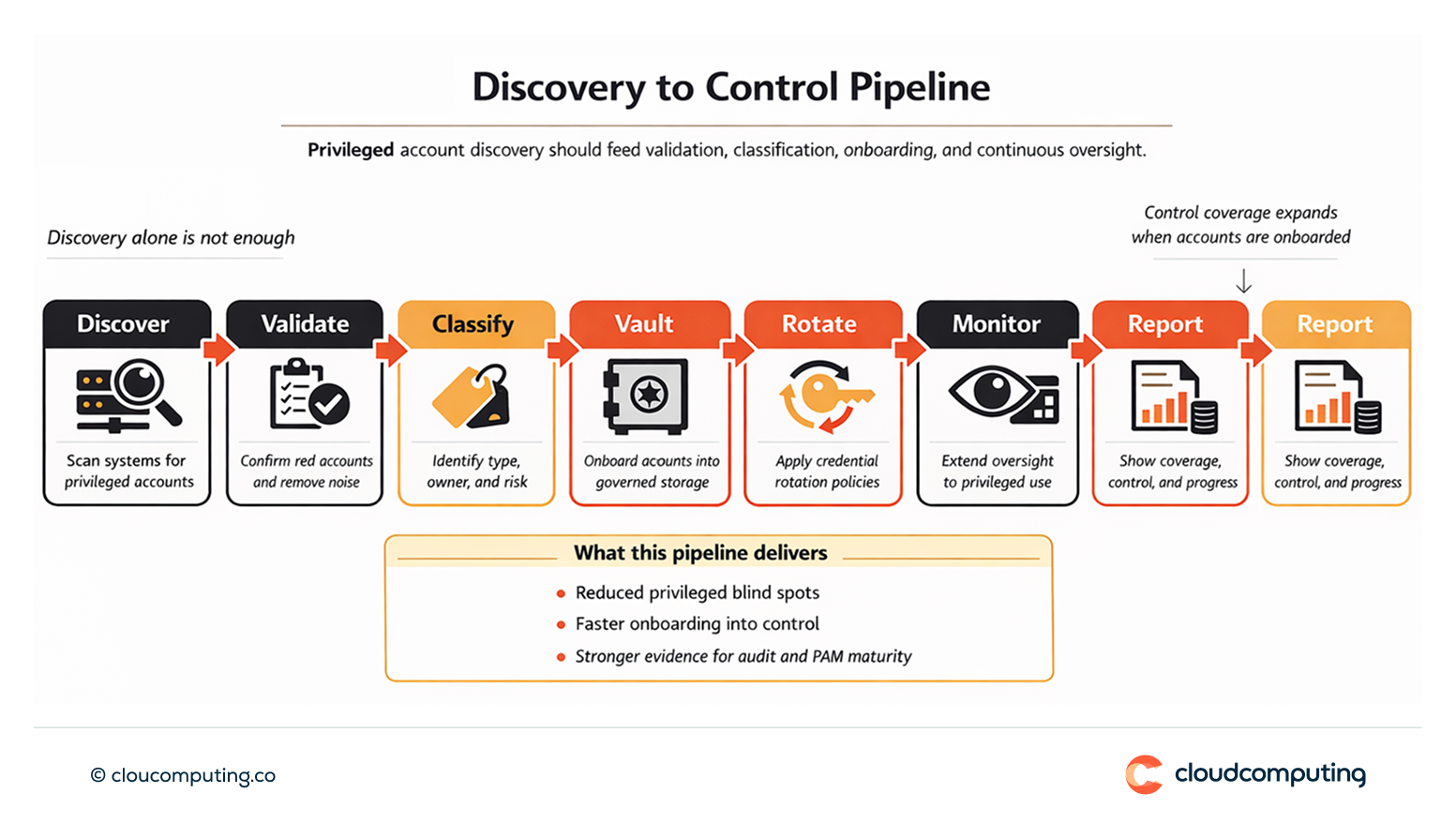
How we solve it: Use Secret Server discovery to identify privileged accounts and onboard them into vaulting, rotation, and monitoring.
We run discovery as a structured pipeline that results in controlled privileged access, not just inventory.
- Discovery scope and validation
Define what to scan first and validate results to prioritise real risk. - Onboard into vaulting and rotation
Bring discovered accounts into Secret Server with consistent governance policies. - Extend oversight
Include newly governed accounts in monitoring and reporting to maintain coverage.
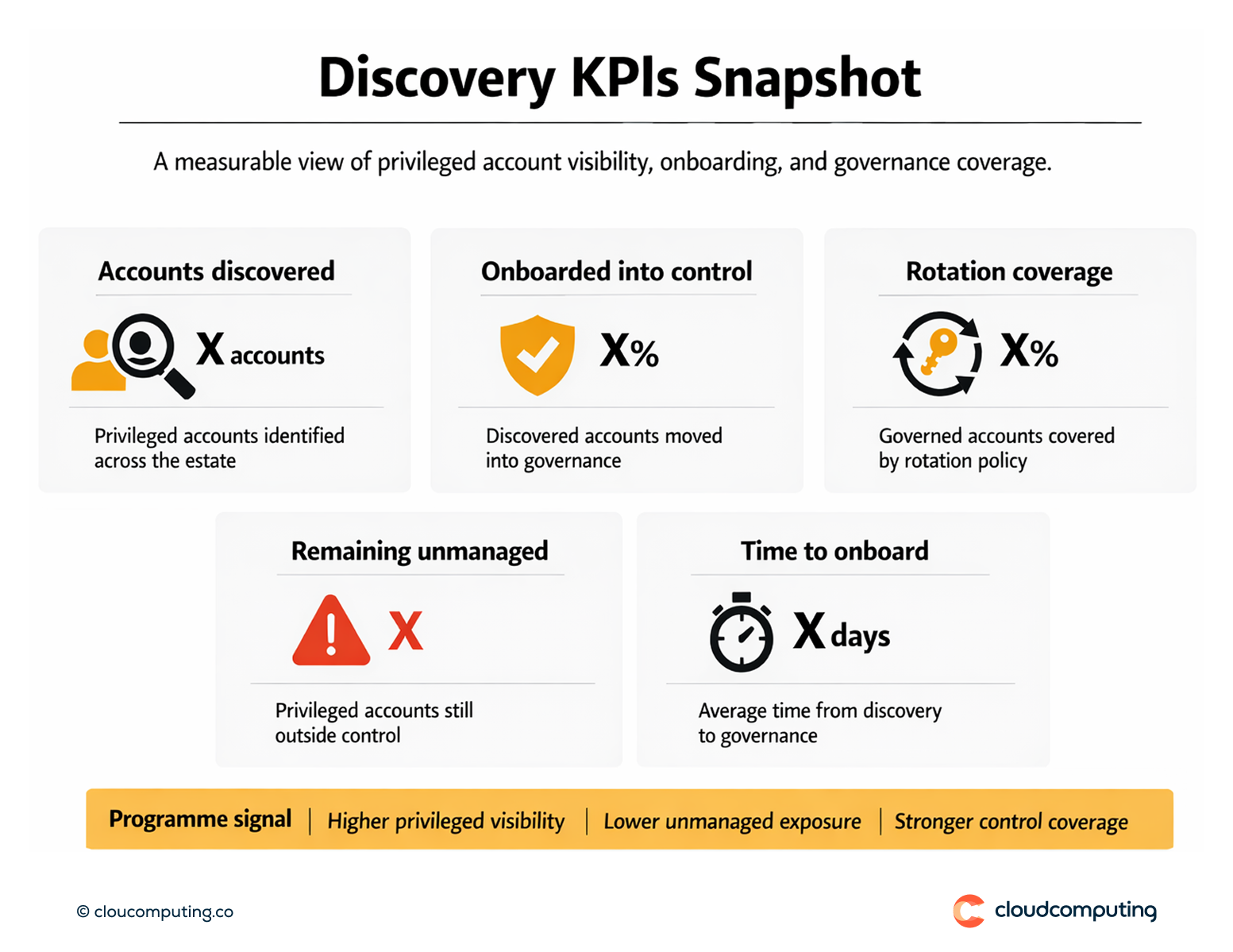
Expected outcome
- Complete privileged inventory with classification and ownership
- Fewer blind spots by onboarding unmanaged accounts into controls
- Stronger control coverage across vaulting, rotation, and session oversight
- Better prioritisation for PAM improvements and remediation
Quick Answers
What is privileged account discovery?
Identifying privileged accounts across systems so they can be governed consistently.
Why is discovery essential?
Controls only work if they cover the full privileged attack surface, including legacy and non-human accounts.
What should discovery lead to?
Onboarding into vaulting, rotation, monitoring, and reporting—otherwise blind spots persist.