The Problem
Shared administrator passwords, weak governance, and credentials that never rotate create persistent privileged exposure.
Access often outlives role changes, credentials are reused across systems, and offboarding does not reliably remove privilege.
Teams struggle to demonstrate control because evidence is fragmented across tickets, spreadsheets, and local knowledge.
How we solve it: Centralise privileged credentials in Delinea Secret Server with discovery and automated rotation policies.
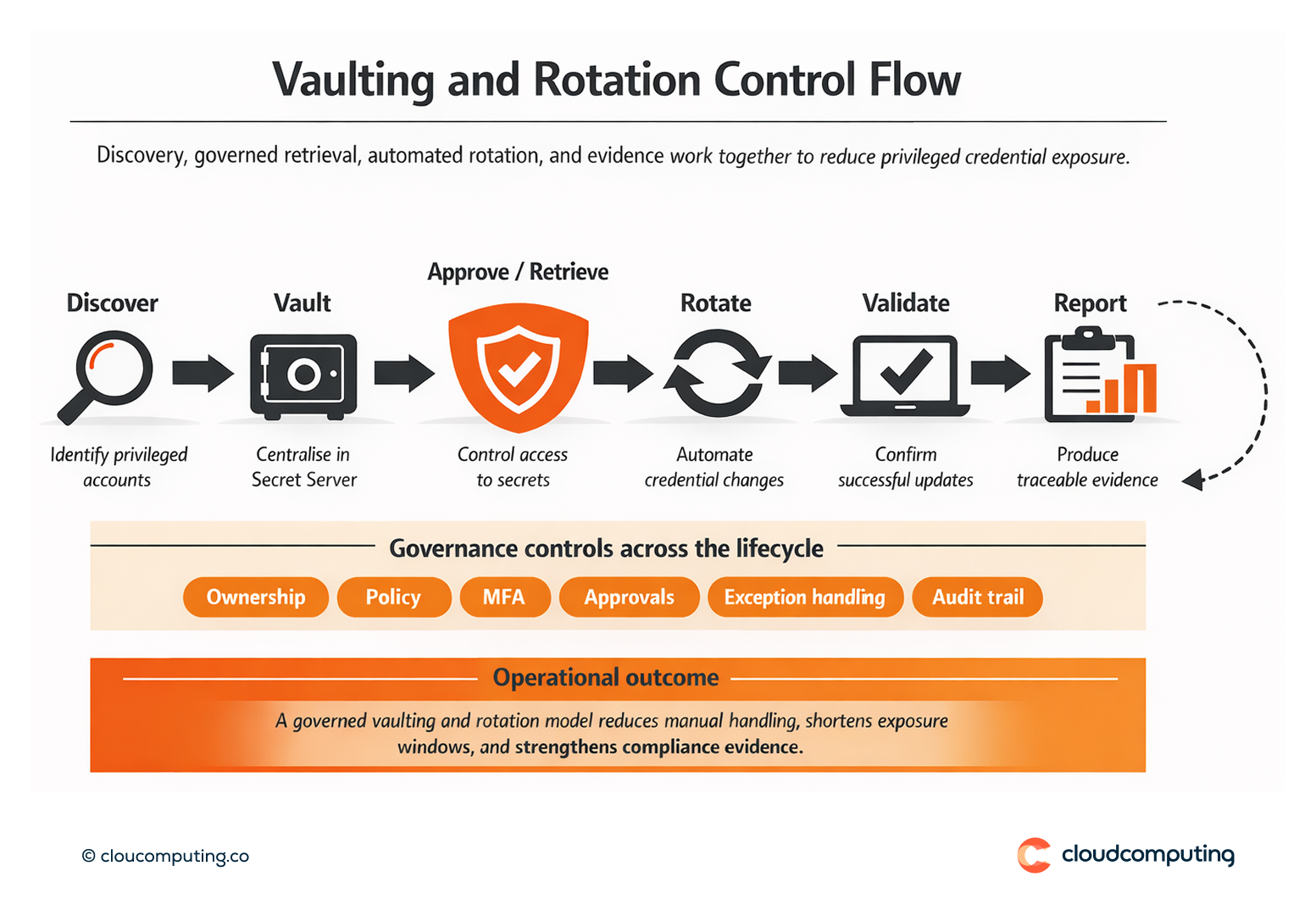
We implement Delinea Secret Server as the control plane for privileged credentials, onboarding accounts, enforcing controlled retrieval, and automating rotation aligned to policy.
- Discovery and onboarding
Identify privileged accounts across platforms and bring them under vault governance with ownership and classification. - Central vaulting and access control
Enforce role-based access, strong authentication, and approvals where required for secret retrieval. - Automated rotation and validation
Apply rotation schedules and triggers, validate updates, and reduce reliance on manual password changes. - Evidence and exception governance
Standardise break-glass paths with traceability and reporting aligned to compliance needs.
Expected outcome
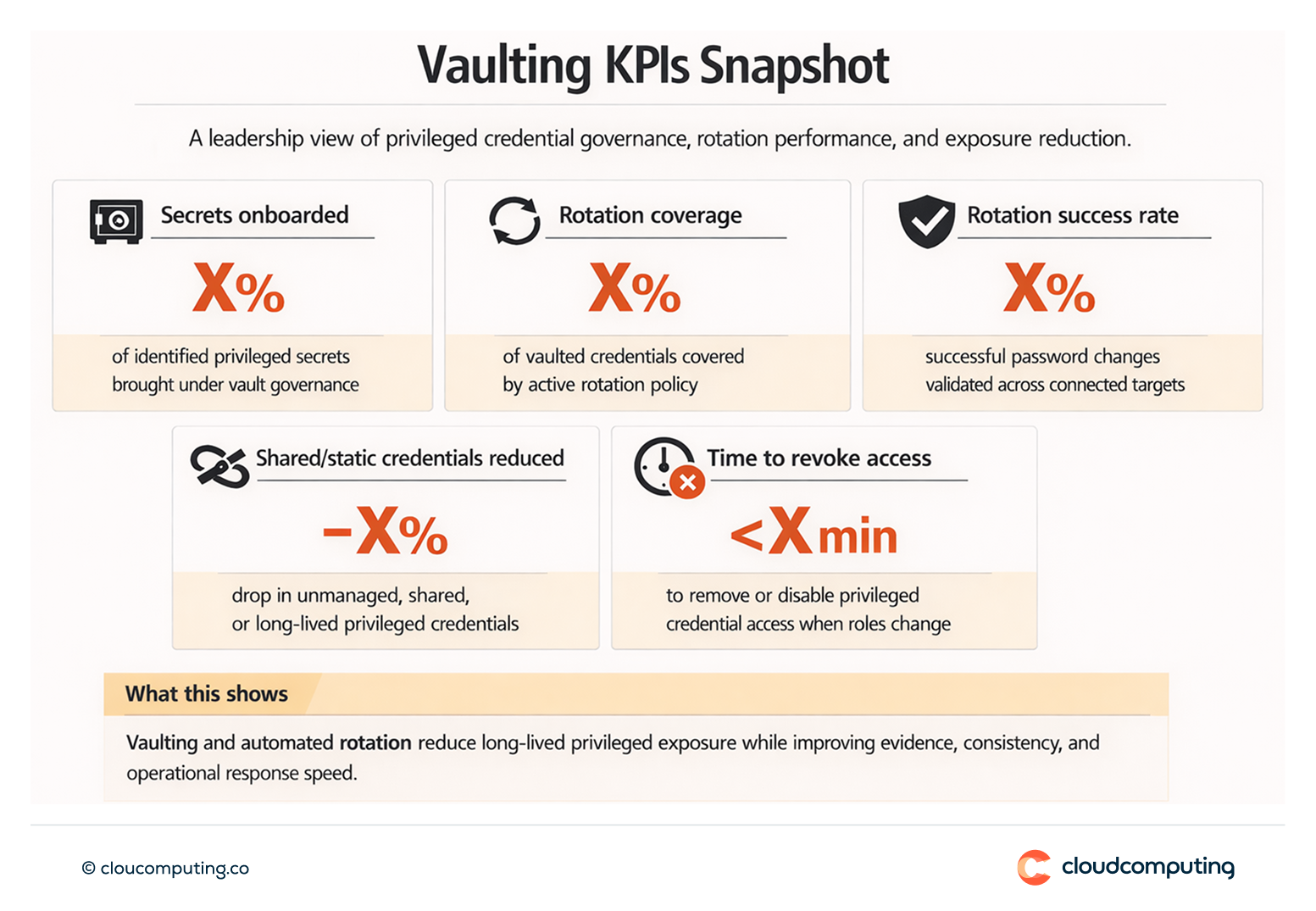
- Reduced credential exposure through controlled storage and automated rotation
- Consistent controls across privileged accounts and platforms
- Stronger compliance posture with traceable access and rotation evidence
- Lower operational risk by reducing manual secret handling and reuse
Quick Answers
What is privileged credential vaulting?
Centralising privileged secrets in a controlled vault so access is governed and auditable.
Why is rotation important?
Static credentials create long-lived exposure and increase the impact of compromise.
What does discovery add?
Visibility of unmanaged privileged accounts so controls can be applied comprehensively.