The Problem
Custom applications and APIs often evolve with inconsistent authentication patterns: different teams implement different libraries, token handling varies, and access policies are enforced unevenly across services.
Some internal apps rely on legacy session models or hard-coded secrets, while APIs expose endpoints without consistent authorisation checks.
The result is predictable friction and risk: developers spend time rebuilding auth, security teams struggle to enforce standards, and the business inherits uneven assurance across critical internal services.
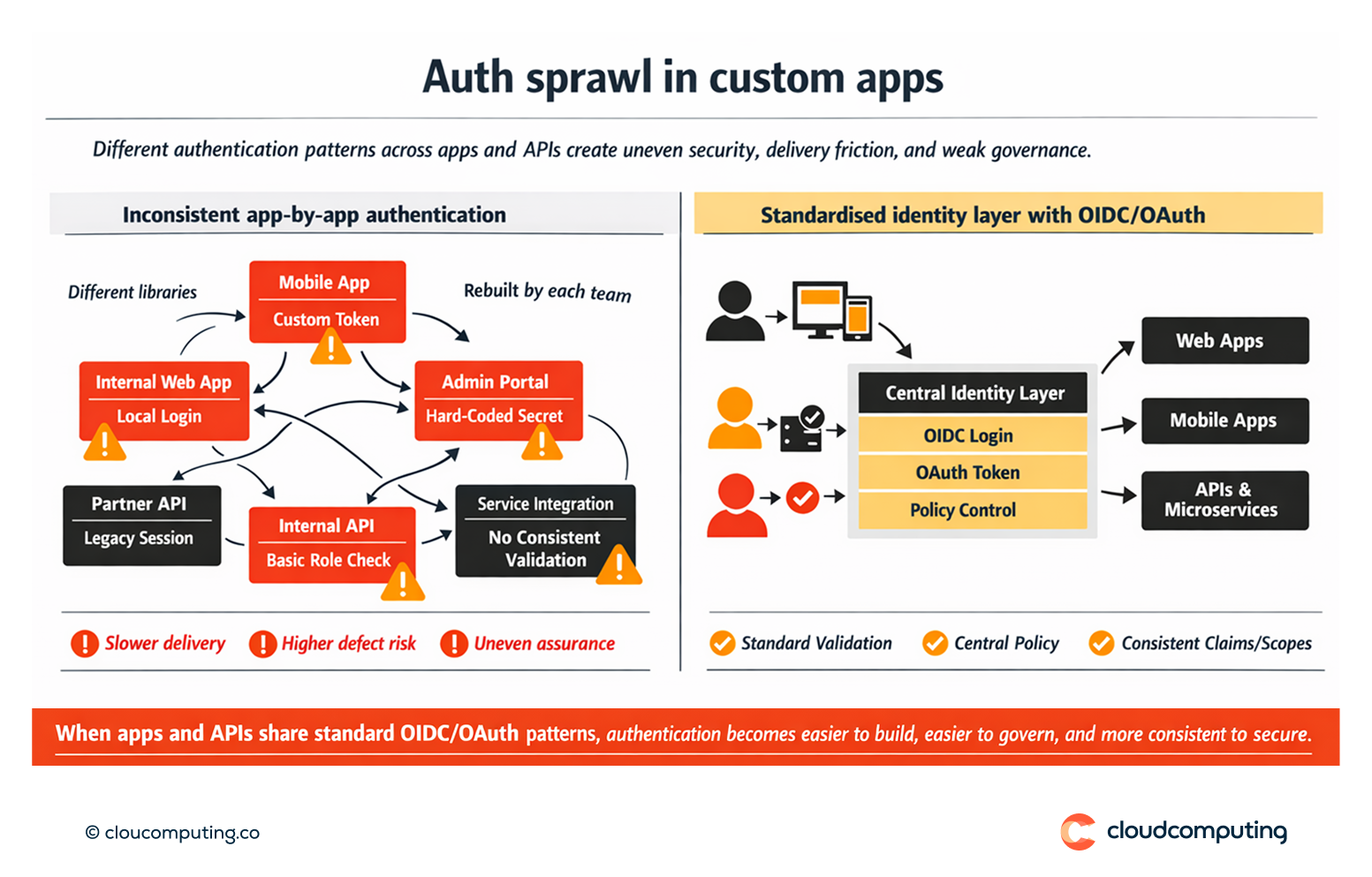
How we solve it: Standardise custom app and API authentication with OIDC/OAuth and centralised policy enforcement.
We implement a consistent identity pattern for developers – modern protocols, standard token flows, and central policy – so security is predictable and delivery is faster.
- Reference architecture for app and API access
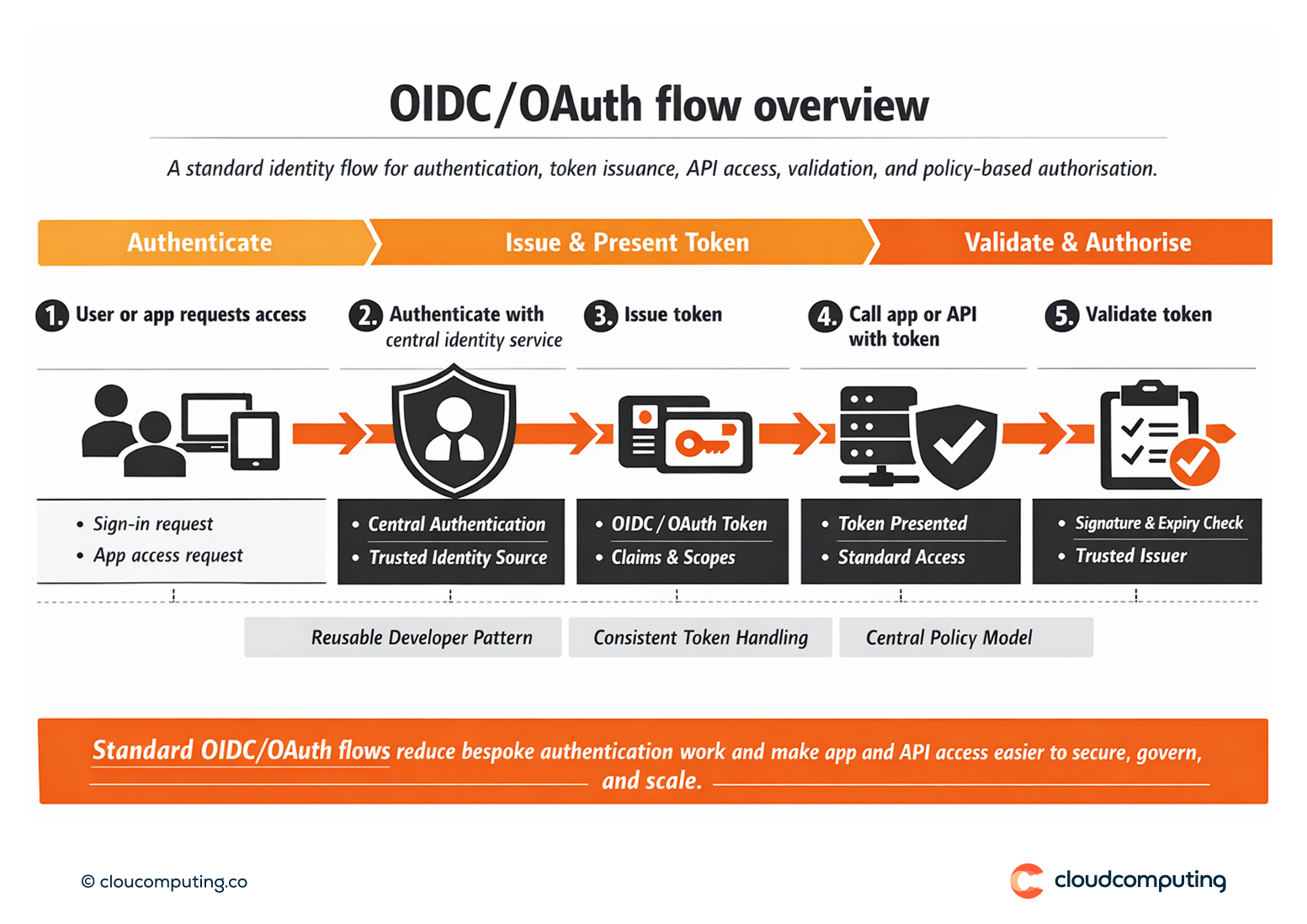
We define standard patterns for web apps, mobile apps, service-to-service access, and API gateways, aligning to OIDC/OAuth flows appropriate to each use case. - Centralised authentication and token issuance
We standardise how identities authenticate and how tokens are issued, validated, and refreshed, reducing bespoke implementations and configuration drift. - Consistent authorisation controls
We align authorisation models (claims, scopes, groups/roles) to business needs so apps and APIs enforce least privilege consistently. - Developer enablement and reusable components
We provide implementation guidance, templates, and onboarding patterns so teams can integrate quickly without repeated design cycles. - Operational governance and visibility
We define ownership, app onboarding standards, and monitoring so security teams can identify misconfigurations and risky exceptions early.
Expected outcome
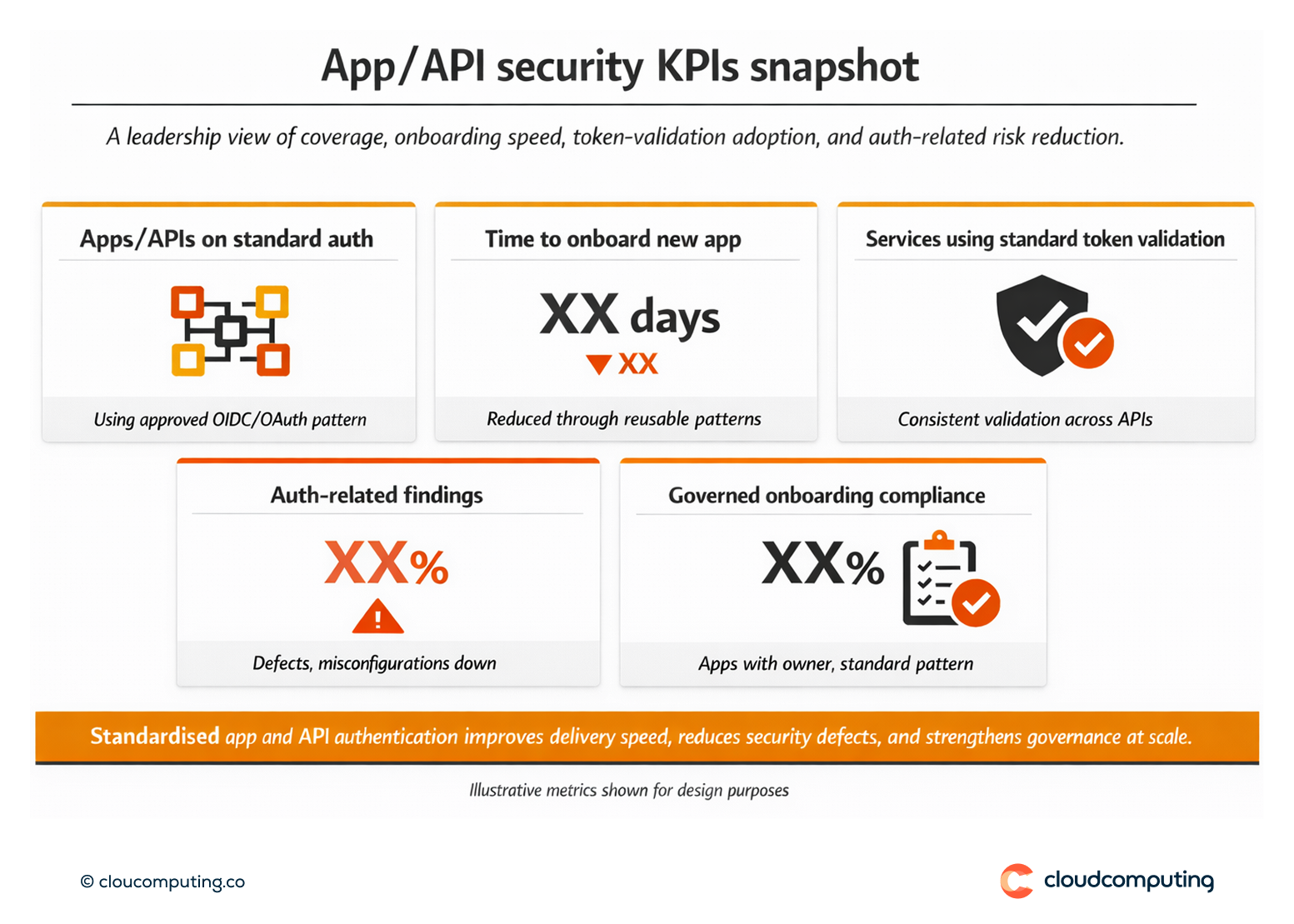
- Faster delivery for developers by reusing standard patterns and reducing custom auth work
- Consistent security for the business through centralised policy and predictable protocol usage
- Reduced auth-related defects via standard token handling and authorisation models
- Better audit and governance posture with clear ownership and consistent onboarding standards
Quick Answers
What do OIDC and OAuth solve for custom apps and APIs?
They provide standard protocols for authentication and authorisation so apps and APIs can rely on consistent token-based access patterns.
Why is inconsistent authentication a security risk?
Because policy enforcement varies, token handling errors occur, and security teams cannot reliably govern access across services.
How does central policy help developers?
It reduces the need to design auth from scratch and provides predictable, reusable patterns for secure delivery.