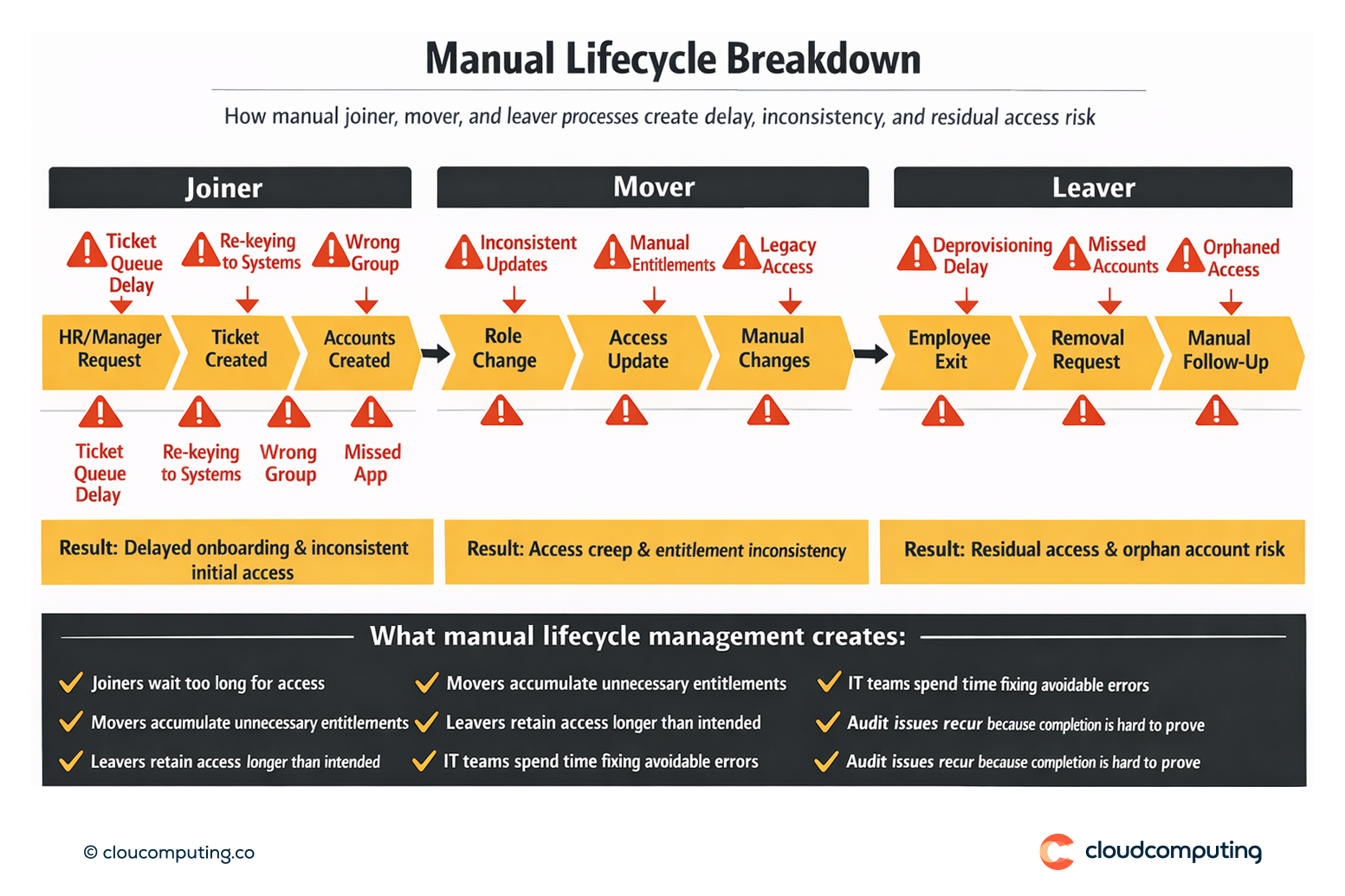
The Problem
Manual account creation and removal is slow, inconsistent, and difficult to validate across a growing SaaS estate.
Joiners wait days for access, movers accumulate entitlements through ad hoc changes, and leavers retain residual access because removals depend on manual follow-up. Each handoff introduces errors: wrong group assignments, missed applications, and incomplete deprovisioning.
Over time, this becomes a measurable risk driver—access creep, orphan accounts, and recurring audit findings—while IT teams absorb the operational load.
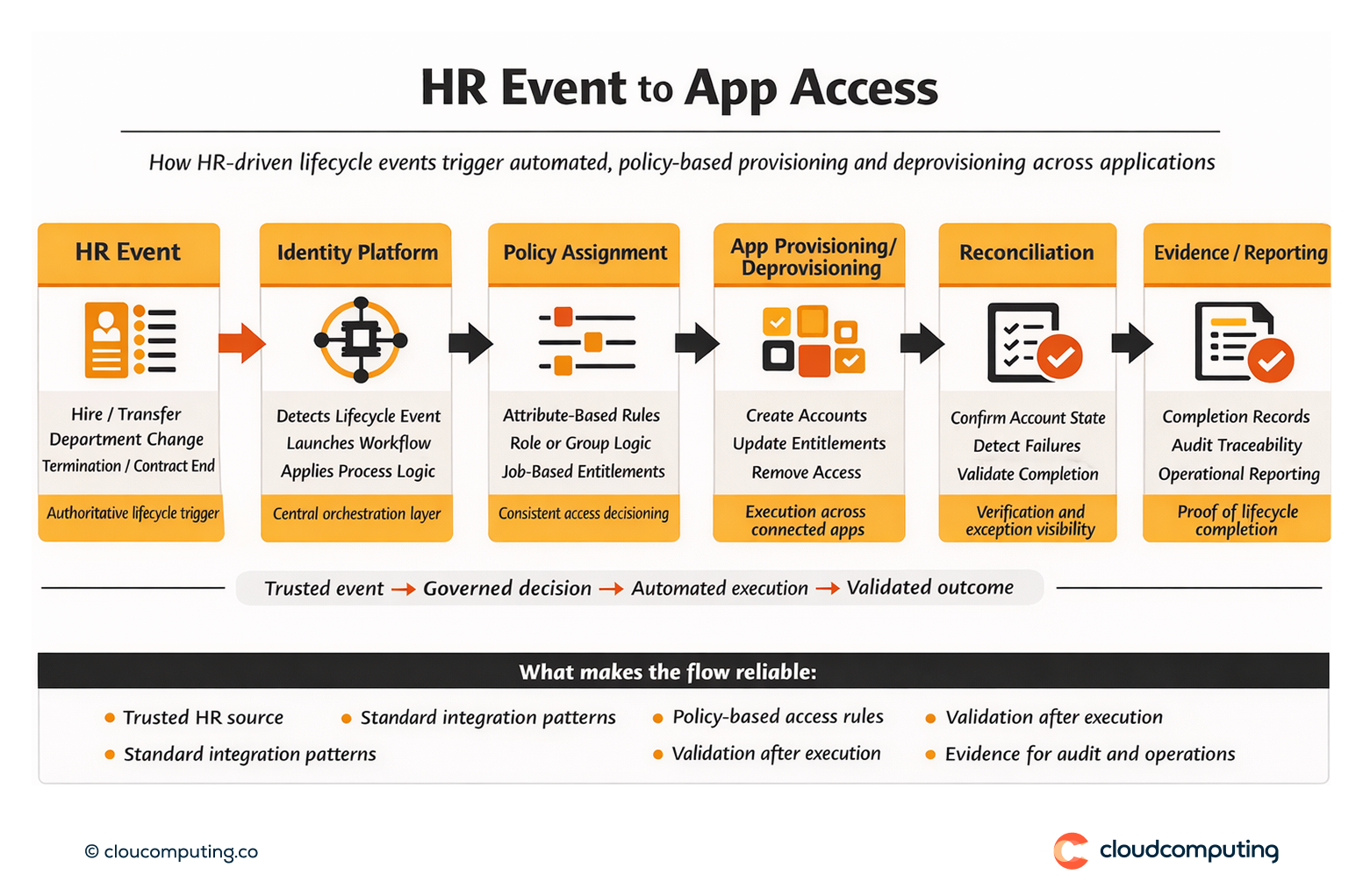
How we solve it: Automate provisioning with HR-driven triggers and standards-based integrations to deliver consistent access lifecycle control.
We implement automated lifecycle provisioning so HR and identity events drive consistent account creation, updates, and removals across applications—at scale.
- Define authoritative sources and lifecycle triggers
We align identity lifecycle to HR data and agreed triggers (hire, transfer, department change, termination, contract end) so access changes start from a trusted source of truth. - Standardise integration patterns
We use standards-based connectors and repeatable onboarding templates so applications can be integrated in waves with predictable effort and outcomes. - Policy-driven access assignment
We define attribute-based rules and group/role assignment patterns so access is granted consistently based on job function and entitlements are not built case-by-case. - Deprovisioning with validation
We implement removal logic that covers both direct assignments and group-based access paths, supported by reconciliation and reporting to confirm completion. - Operational controls and exception governance
We establish ownership, SLAs, failure handling, and controlled exceptions (time-bound and reviewable) so automation remains reliable after go-live.
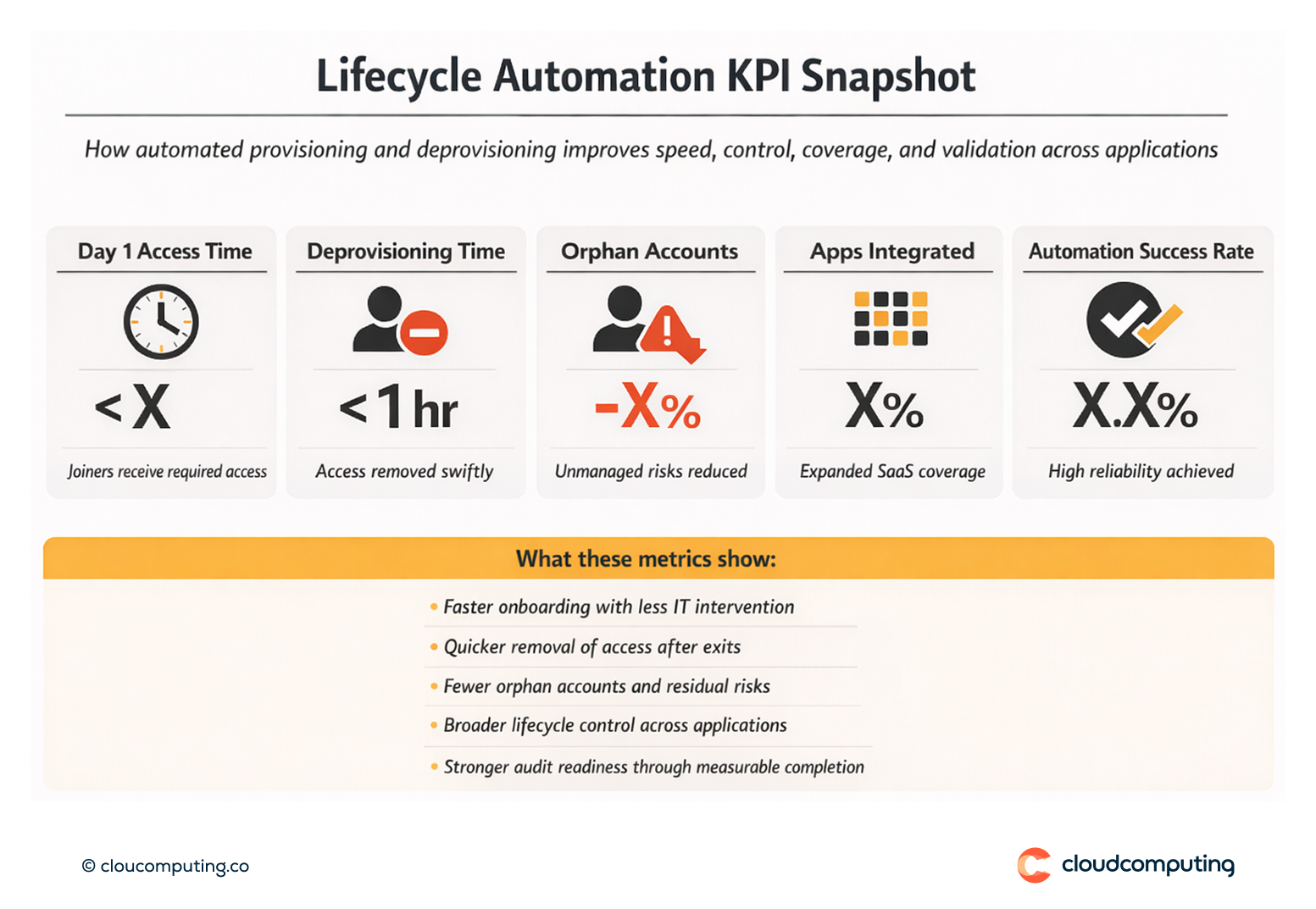
Expected outcome
- Day 1 access for joiners without manual chasing and rework
- Faster changes for movers with consistent updates across applications
- Fewer orphan accounts through reliable deprovisioning and validation
- Reduced access creep by replacing ad hoc changes with policy-driven assignments
- Improved audit readiness with traceability and completion evidence
Quick Answers
What is automated provisioning and deprovisioning?
The automated creation, update, and removal of accounts and access in applications based on identity lifecycle events and policy.
Why is HR-driven provisioning important?
Because HR is typically the authoritative source for workforce changes, enabling predictable access updates when people join, move, or leave.
How do you prevent orphan accounts?
By enforcing deprovisioning logic, running reconciliation, and reporting completion across integrated applications.
