The Problem
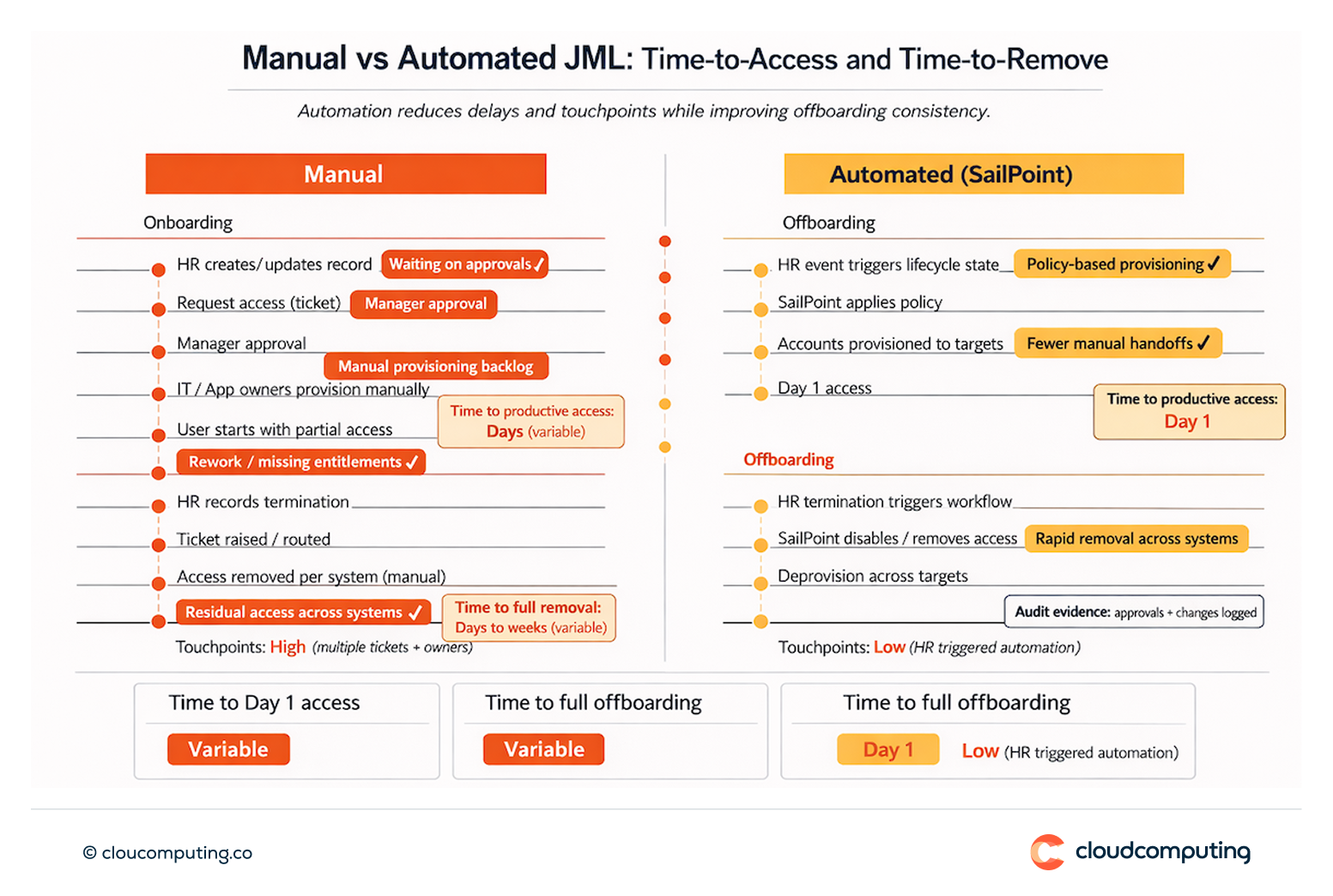
Slow onboarding and delayed access create productivity loss and workarounds. Role changes are handled inconsistently across systems, so entitlements accumulate over time and exceptions become permanent.
Offboarding is often incomplete, leaving residual access across SaaS, on-prem applications, and directories.
The end state is familiar to security and audit teams: access creep, orphan accounts, weak traceability, and recurring audit pressure.
How we solve it: lifecycle automation and rapid access removal
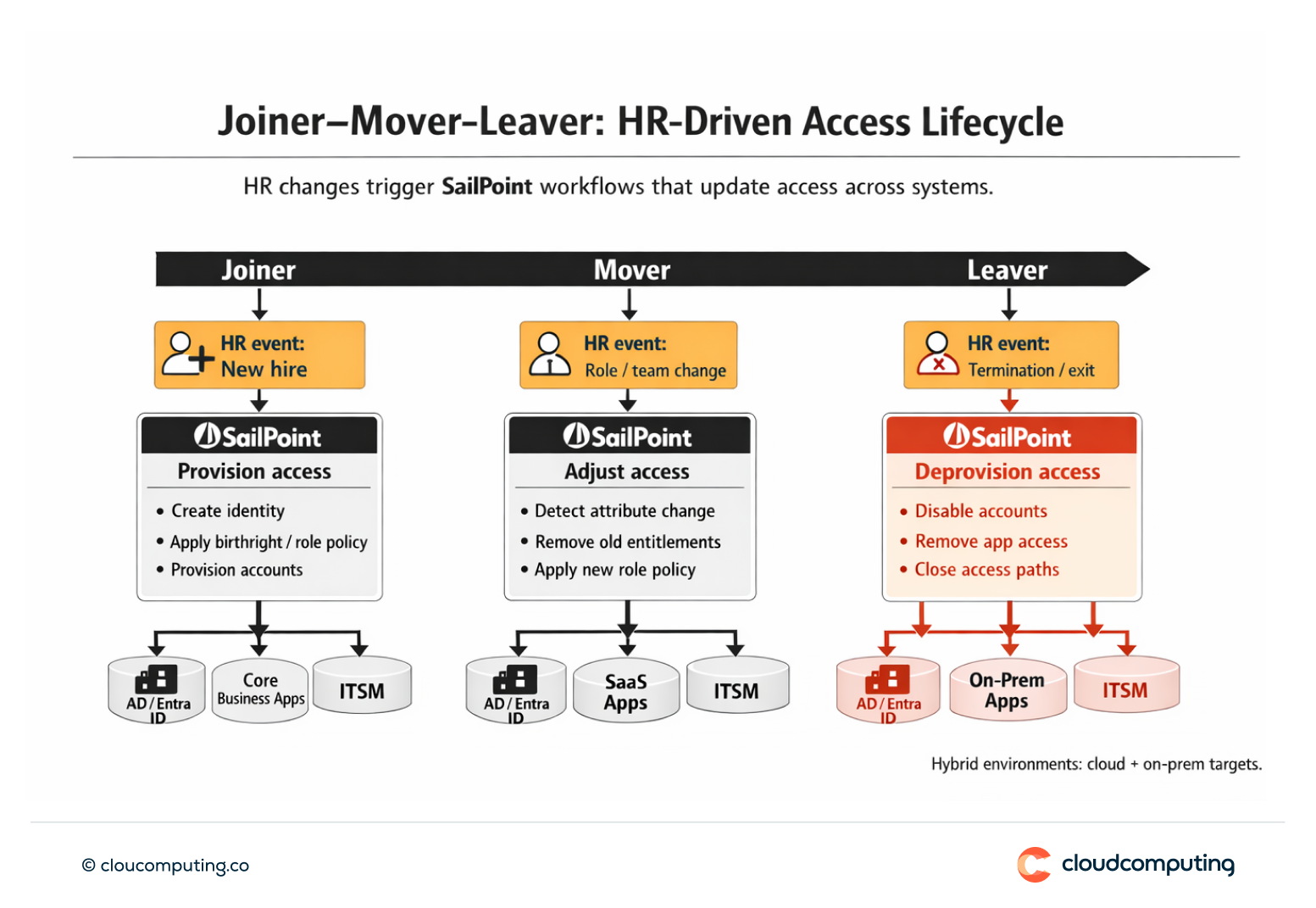
We implement SailPoint lifecycle governance so Joiner–Mover–Leaver events drive consistent access changes across hybrid and cloud environments.
- Lifecycle design anchored to HR truth
We align join, change, leave, leave-of-absence, and rehire scenarios to an authoritative source (HRIS), with clear lifecycle states and control requirements. - Policy-driven provisioning and deprovisioning
We design birthright access, role-based access, and attribute-driven rules so access is granted through policy, not ad hoc tickets. Offboarding enforces rapid removal across connected systems, with safeguards for high-risk applications.
- Integration patterns that scale
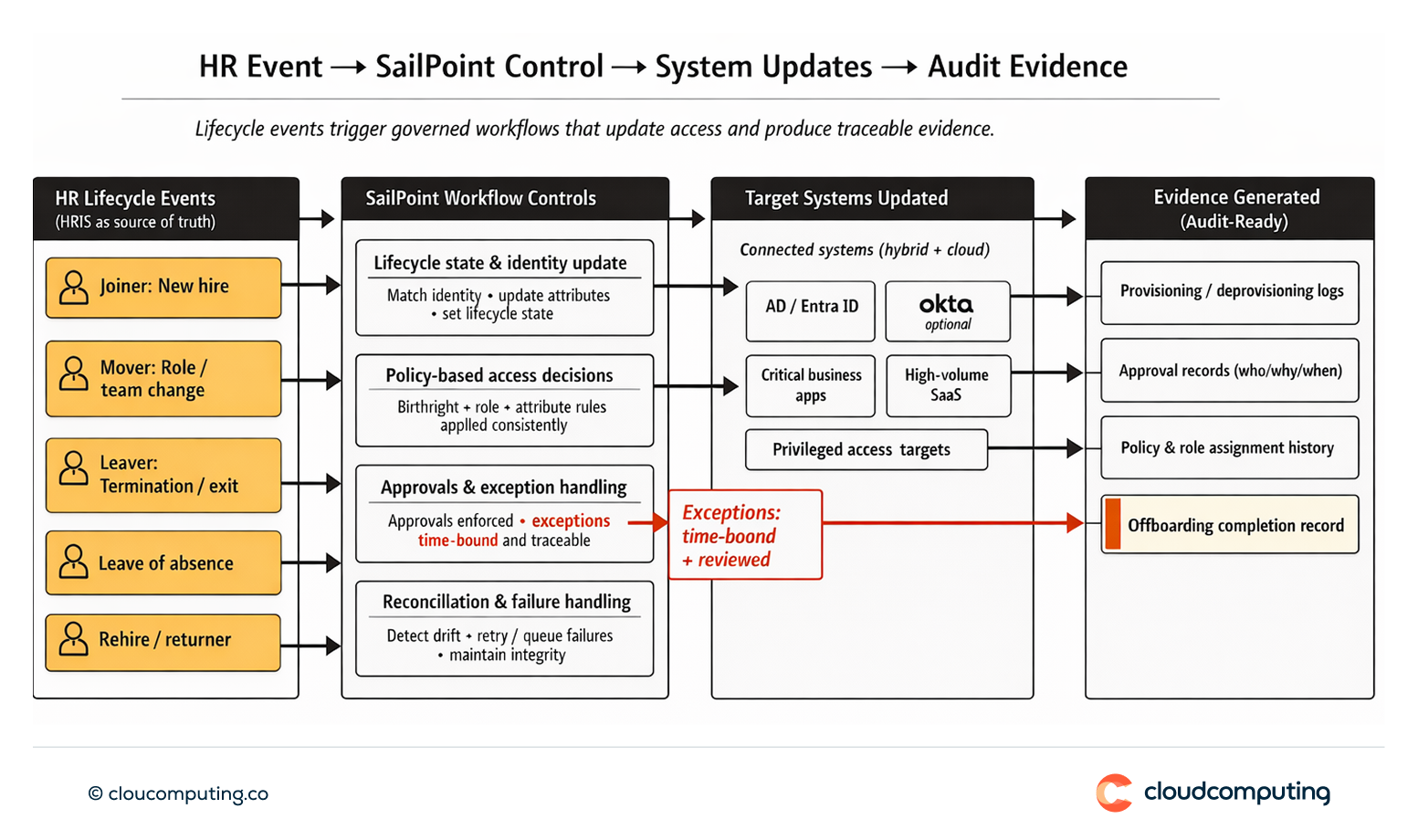
We connect SailPoint to priority targets (e.g., AD/Entra ID and critical applications), define reconciliation and failure handling, and roll out in waves to reduce operational risk. - Exception control and evidence
Where exceptions are necessary, we time-bound them, enforce approvals, and ensure every change produces traceable evidence suitable for audits. - Operationalisation and handover
We establish runbooks, ownership, SLAs, and reporting so lifecycle automation remains reliable after go-live.
Expected outcome
- Day 1 access without bypasses or informal workarounds
- Frictionless transitions when people change roles, teams, or locations
- Secure exits through fast, consistent offboarding across systems
- Reduced access creep and fewer orphan accounts
- Audit-ready traceability with consistent evidence of lifecycle-driven access changes
Quick Answers
What is JML automation?
JML automation is the implementation of identity lifecycle controls so onboarding, role changes, and offboarding trigger consistent access changes across systems.
Why does JML matter for risk?
Because lifecycle gaps are a common source of over-privileged access, orphan accounts, and audit findings.
What does SailPoint do in JML?
It orchestrates lifecycle events and access policies across connected systems, with traceability for approvals and changes.
FAQ
-
How do you handle contractors and fixed-term contracts in JML?
We model contractors as distinct worker types with start/end dates, sponsor ownership, and time-bound access policies. SailPoint enforces automatic expiry, periodic validation, and rapid deprovisioning at contract end (or early termination), across systems like AD/Entra ID, Okta, SaaS apps, and ITSM.
-
How do rehires and internal transfers avoid duplicate identities?
We implement identity matching rules (unique identifiers + HR attributes) and lifecycle states so rehires are reactivated rather than recreated. For internal transfers, SailPoint executes a controlled “mover” transition: removes old entitlements, applies the new role policy, and reconciles accounts to prevent duplicates across AD/Entra ID, Okta, and applications.
-
Which systems should be integrated first for maximum risk reduction?
Start with the systems that create the most residual risk and audit exposure: (1) core identity platforms (AD/Entra ID and/or Okta), (2) privileged access targets and critical business apps, (3) high-volume SaaS apps, then (4) ITSM and remaining long-tail systems. This sequencing reduces orphan accounts fastest and improves traceability early.
-
How do you manage exceptions without creating permanent access creep?
Exceptions are always time-bound (expiry by default), require explicit approvals, and are reviewed on a schedule. We separate policy-based access from exception-based access, enforce compensating controls for high-risk apps, and ensure every exception produces audit evidence (who approved, why, for how long, and what changed).
-
How do you prove offboarding completion to auditors?
We generate an auditable “offboarding completion” record showing: the HR trigger, SailPoint workflow execution, downstream actions per target (e.g., disable in AD/Entra ID, session/app access removed in Okta, accounts deprovisioned in key apps), reconciliation results, timestamps, and any failures with remediation proof. This evidence is exportable and consistent per user and per period.
