The Problem
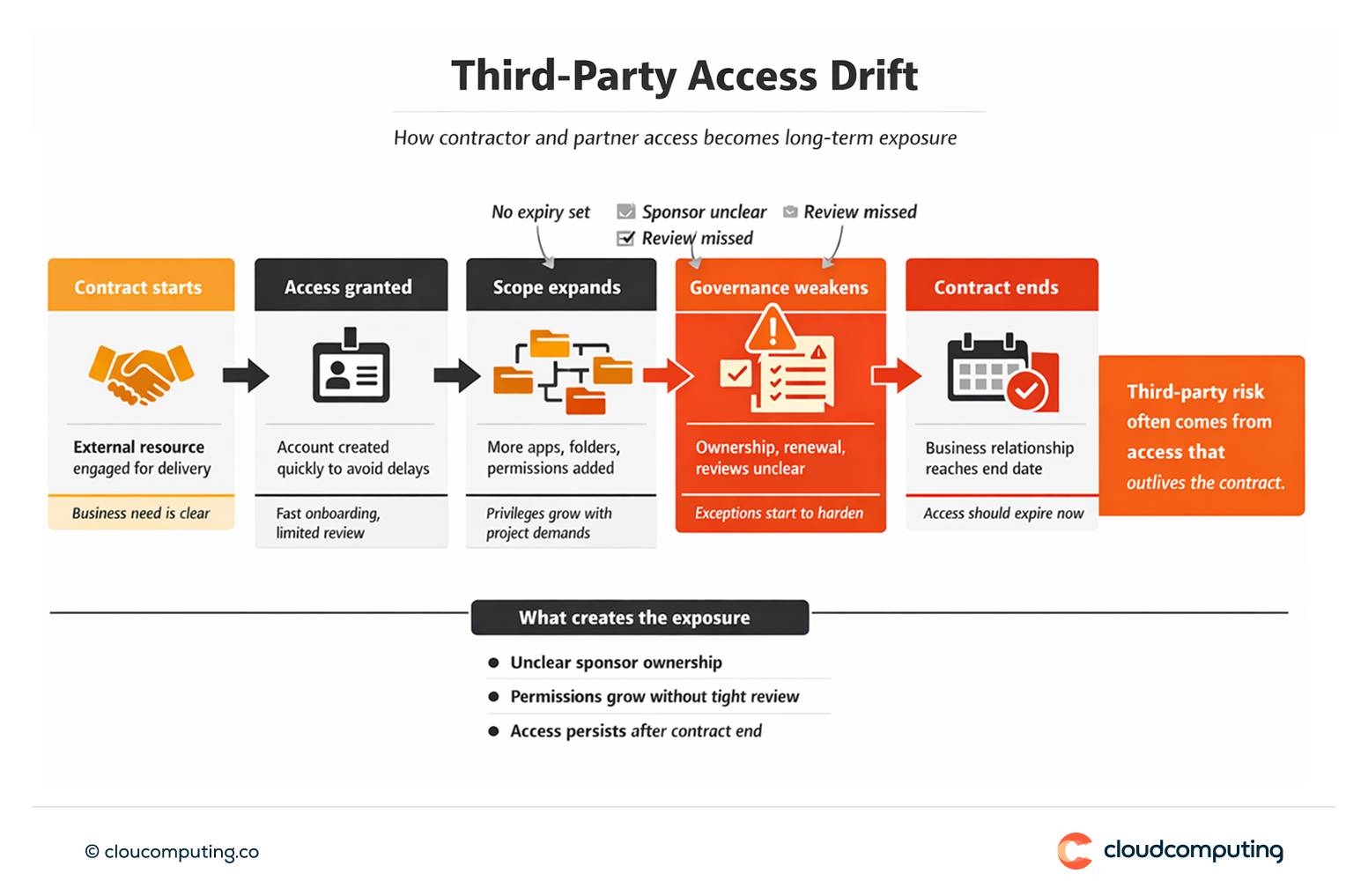
Third-party access is often treated as a special case – and becomes a long-term exposure.
Contractors and partners are onboarded quickly to meet delivery timelines, then access persists because offboarding depends on manual follow-up and unclear ownership. External users may authenticate outside the standard sign-in layer, bypassing consistent MFA and policy controls.
Over time, permissions expand, exceptions become permanent, and the organisation loses a reliable view of who is still entitled to access and why.
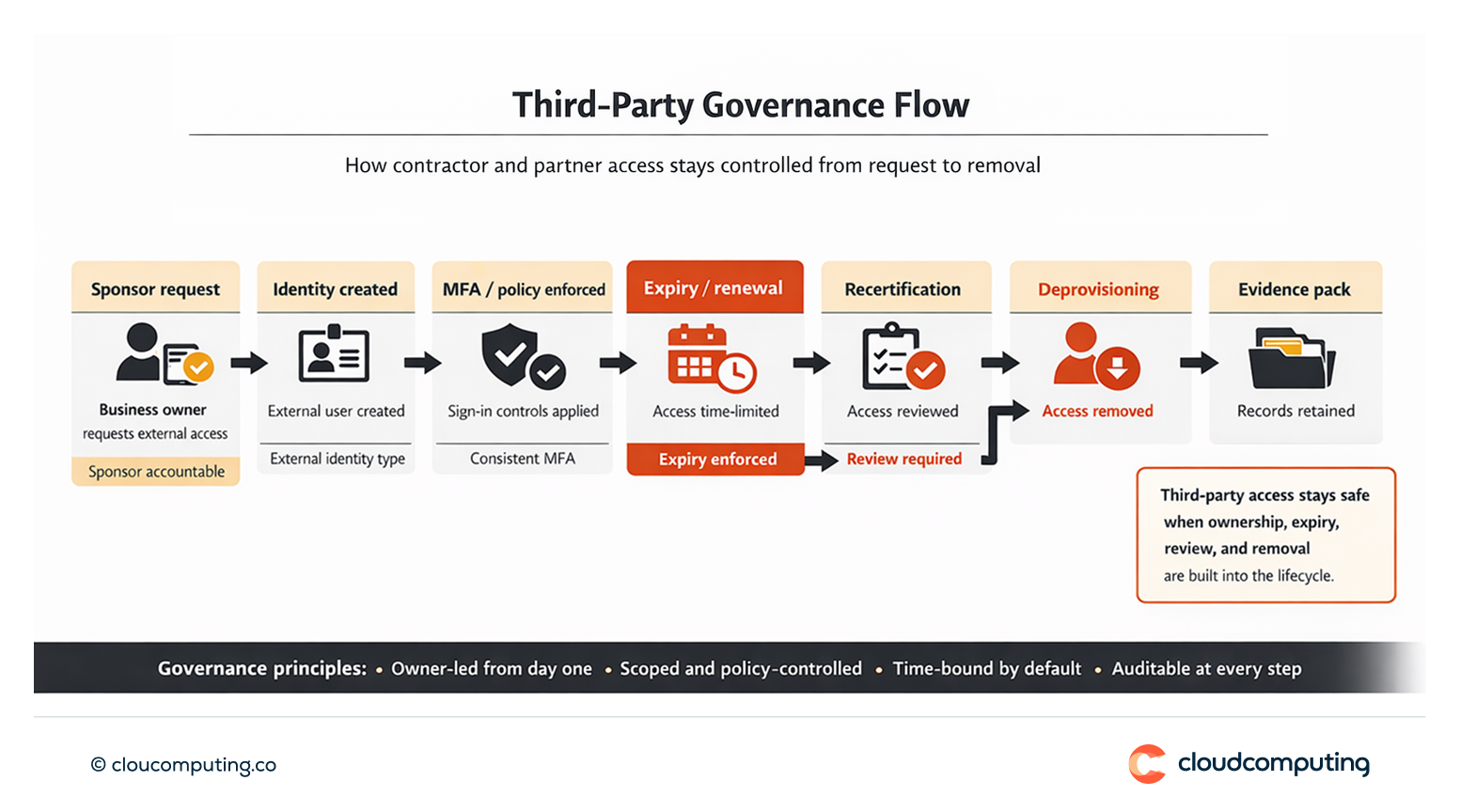
How we solve it: Control third-party onboarding, scope access tightly, and enforce expiration with periodic recertification.
We implement a third-party access model that is owner-led, time-bound, and governed through consistent identity controls, including enrolment, authentication, and review.
- Sponsor ownership and accountability
We enforce a sponsor model so every external identity has a business owner responsible for access scope, renewals, and offboarding. - Controlled onboarding and identity boundaries
We standardise onboarding workflows so third parties are created and managed under defined identity types and policies rather than ad hoc accounts and informal access paths. - Scoped access by design
We define what third parties can access, with least privilege defaults and clear separation between external and internal access paths. Elevated access becomes time-bound by default. - Expiration and recertification patterns
We set contract-based expiry and periodic recertification for continued access, ensuring access remains justified and is removed when no longer required. - Evidence and operational controls
We implement traceable approvals, renewal decisions, and removal evidence so third-party access is auditable without manual reconstruction.
Expected outcome
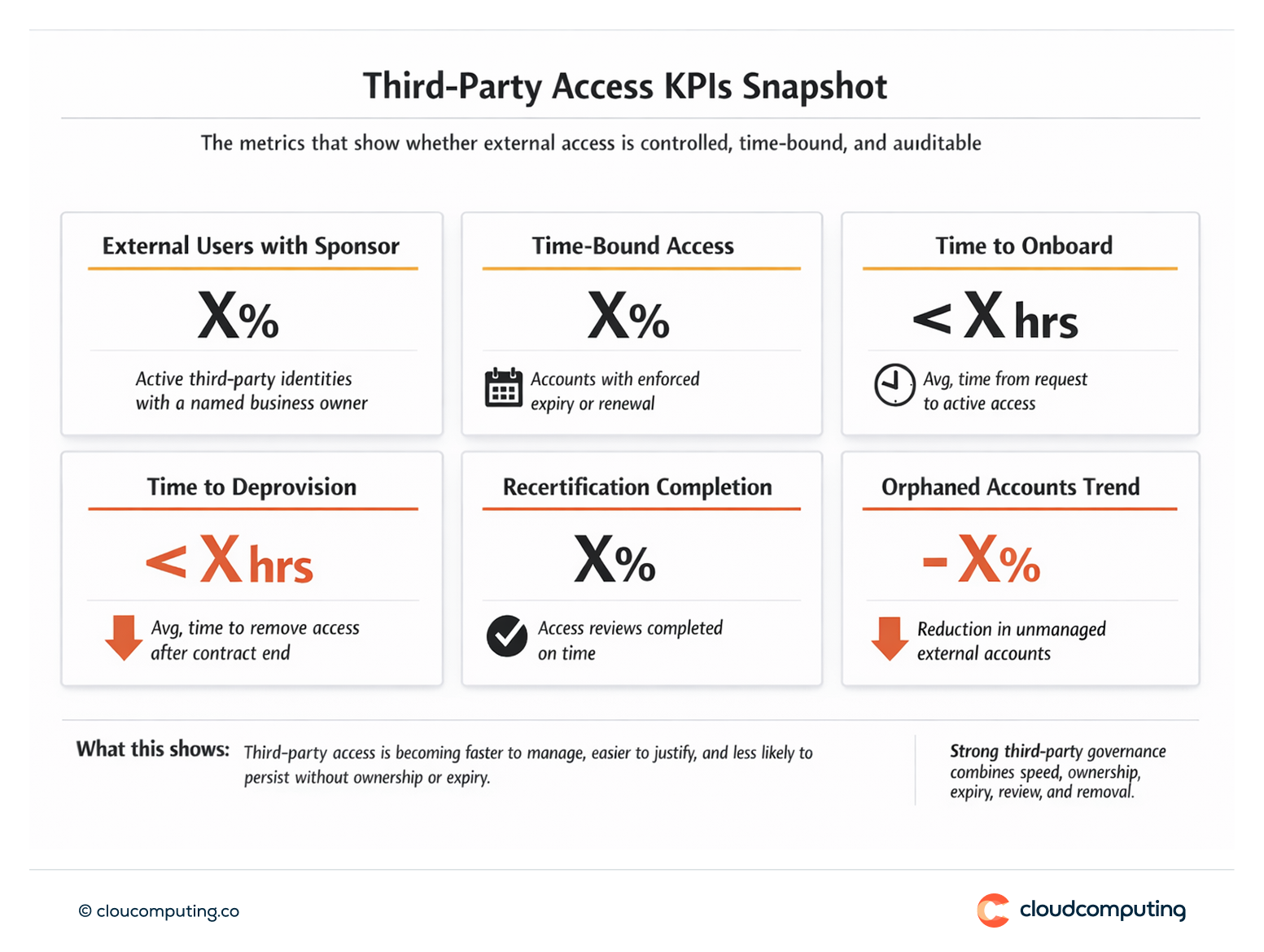
- Faster third-party onboarding through standardised workflows and clear ownership
- Less long-term risk via scoped access, enforced controls, and time-bound permissions
- Reduced access drift with expiry and recertification as default governance mechanisms
- Improved audit readiness through traceable approvals, renewals, and removal evidence
Quick Answers
Why does third-party access become risky over time?
Because ownership is unclear, offboarding is manual, and access often persists beyond contract end with accumulating permissions.
What does “clear boundaries” mean for contractors and partners?
Defined identity types, scoped access, enforced sign-in controls, and separation between external and internal access paths.
How do expiration and recertification reduce risk?
They ensure access must be renewed explicitly, remains justified, and is removed automatically when contracts end or reviews fail.
