The Problem
Sensitive files often move without consistent encryption, signing, or policy enforcement.
Different teams apply different rules, and controls vary per route, partner, or protocol. This increases confidentiality and integrity risk and creates compliance exposure when governance cannot prove consistent enforcement.
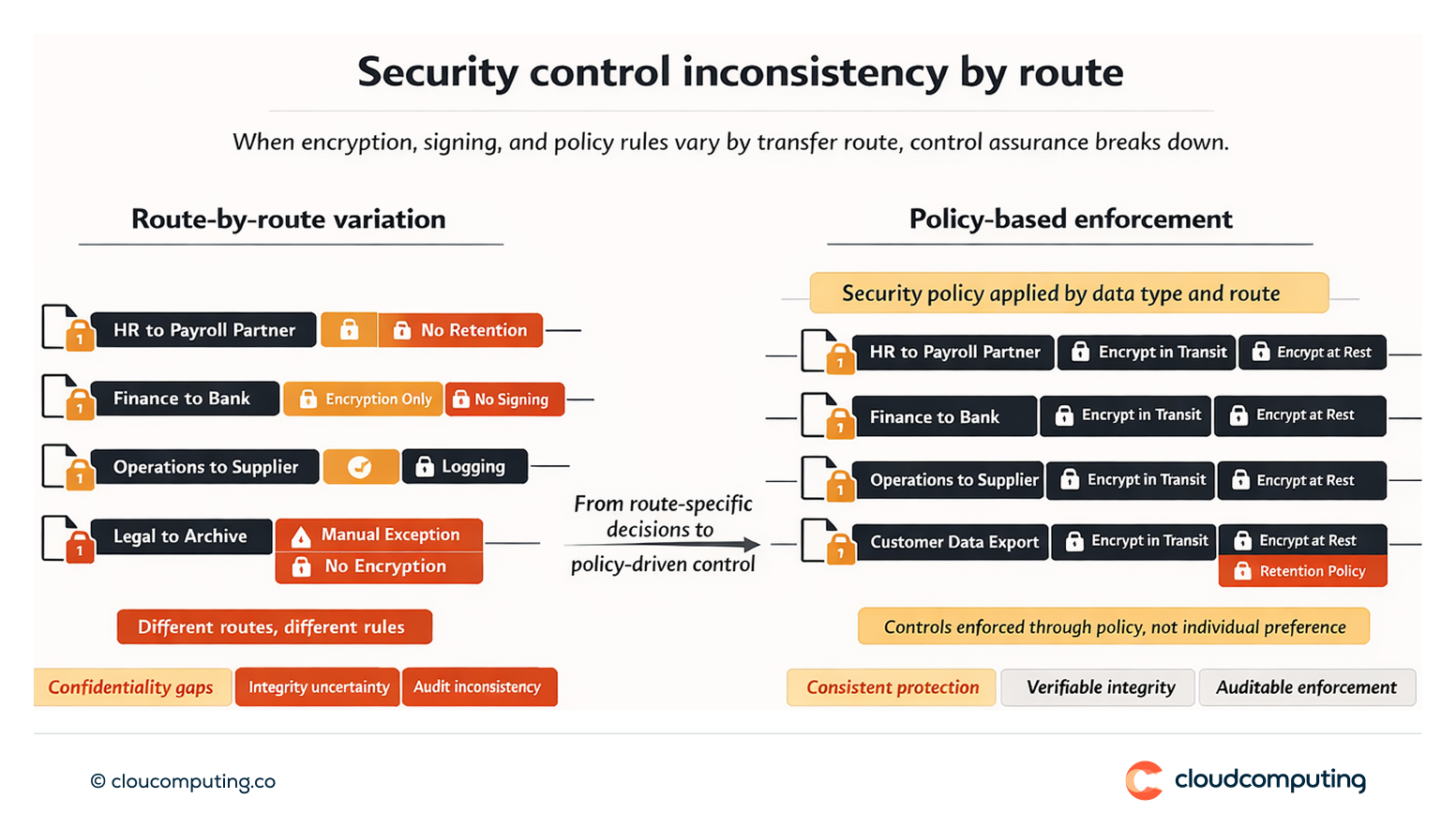
How we solve it: Enforce encryption in transit and at rest, signing, and policy controls per data type and route using Axway MFT.
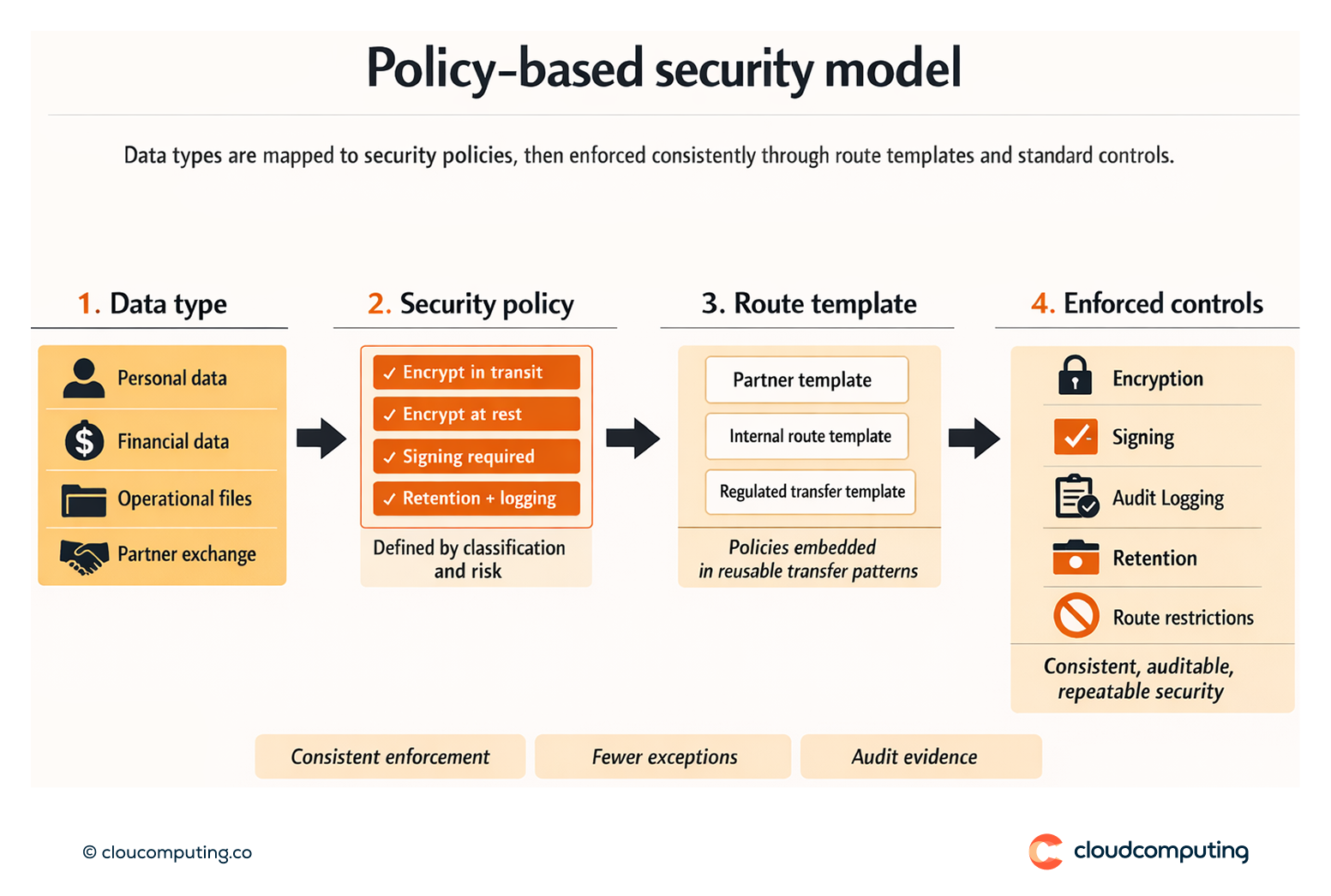
We implement a policy-driven security model so controls are applied consistently, regardless of protocol or partner.
- Data classification to policy mapping
Define which data types require which controls (encryption, signing, retention, routing constraints). - Encryption and signing standards
Enforce encryption in transit, encryption at rest, and signing where integrity and non-repudiation are required. - Policy enforcement by route
Apply policies to transfer routes and templates so security is consistent and auditable.
Expected outcome
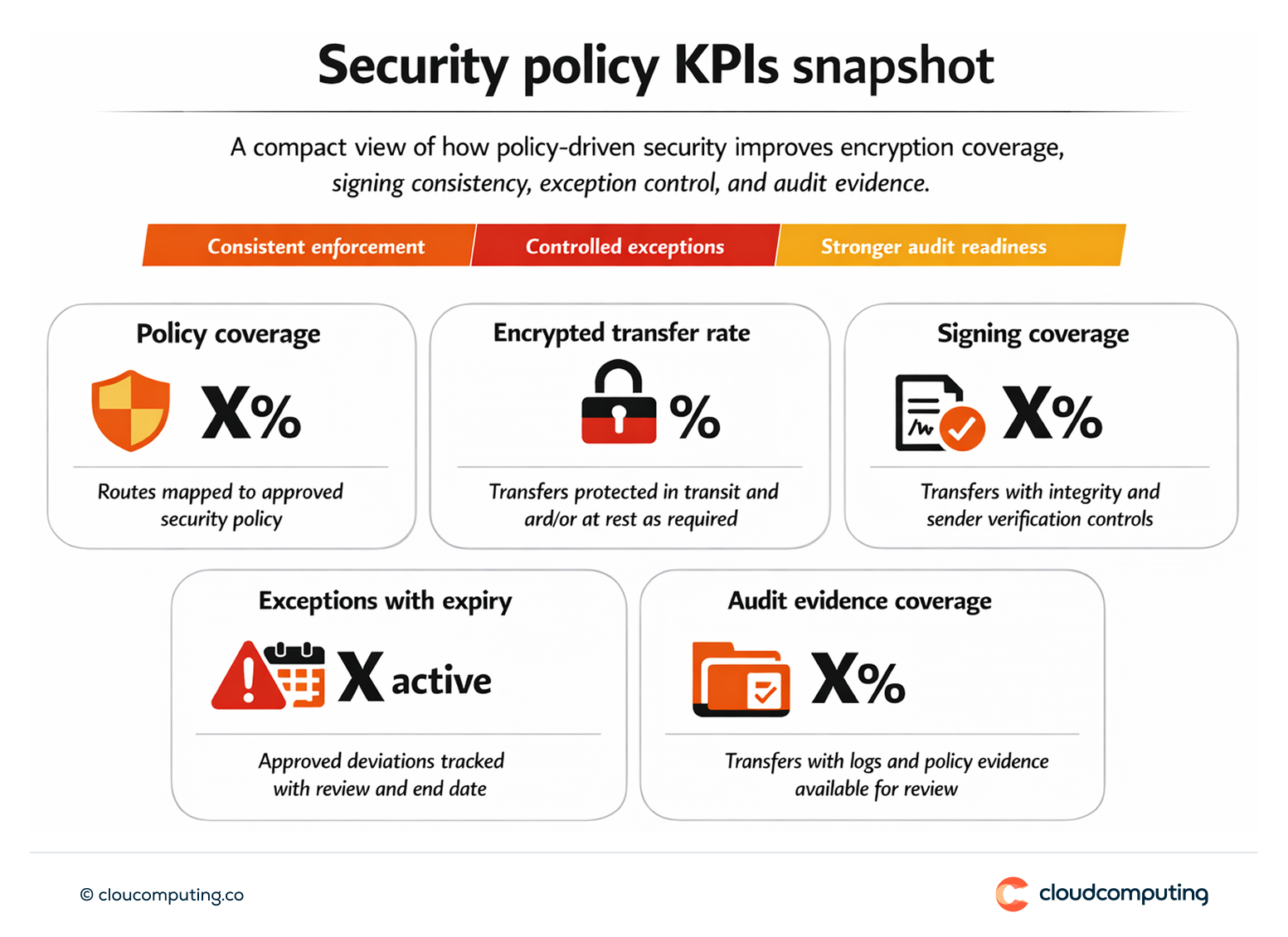
- Stronger confidentiality and integrity through consistent encryption and signing
- Reduced compliance risk with enforced policies and evidence
- Fewer security exceptions due to standard templates and controls
- Improved operational predictability through repeatable security patterns
Quick Answers
What is end-to-end encryption in MFT?
Encryption applied consistently for file movement, including protection in transit and at rest where required.
Why use policy-based security?
It ensures security controls are consistent across routes, partners, and teams, reducing drift.
When is signing needed?
When integrity and non-repudiation requirements demand proof that files were not altered and originated from a known sender.