The Problem
Sensitive files move without classification, controls, or guardrails.
Teams cannot consistently enforce who can send or receive what, which routes are allowed, and what controls apply.
Uncontrolled pathways increase data leakage risk and make accountability unclear.
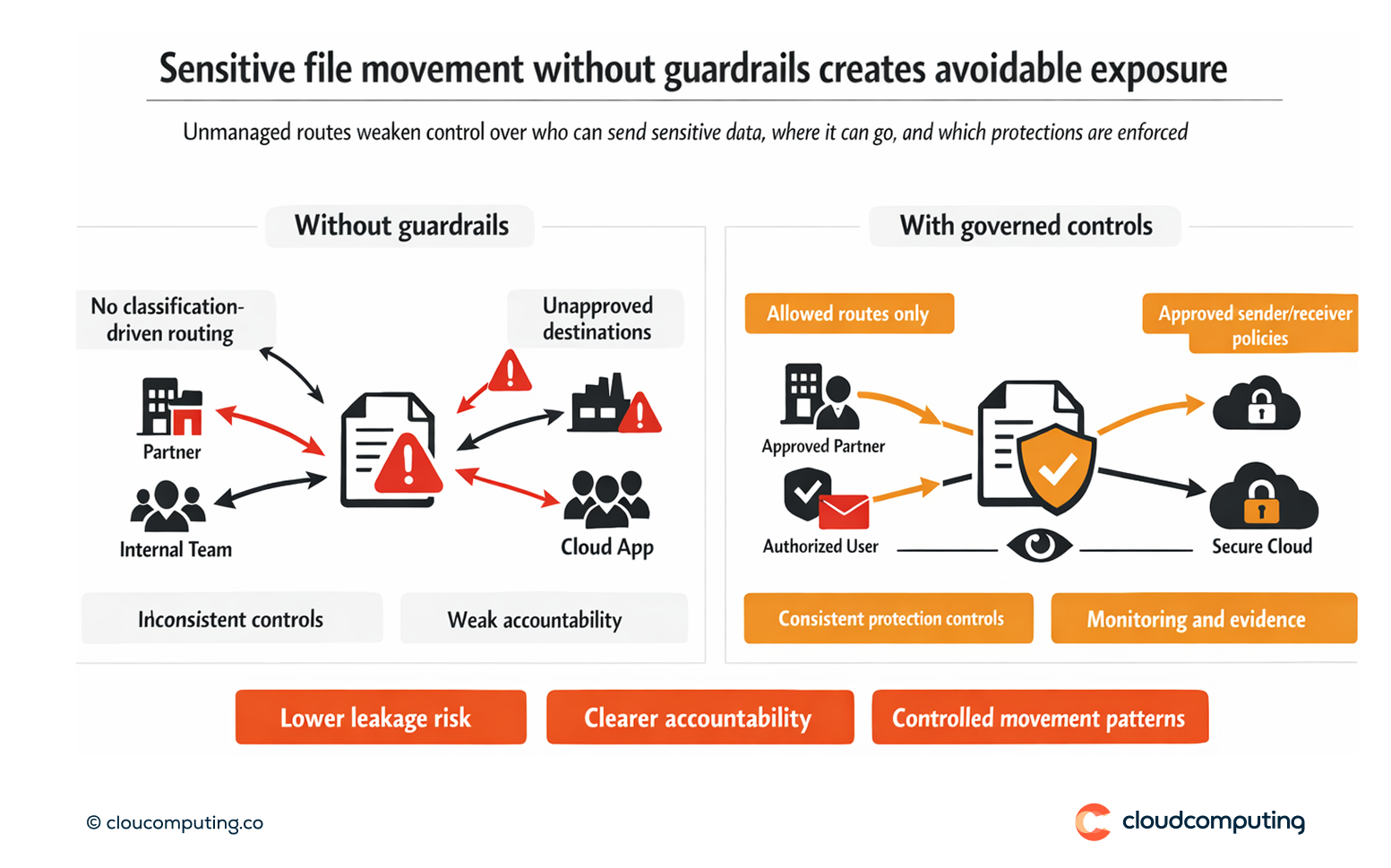
How we solve it: Enforce governance policies, integrate security controls, and reduce uncontrolled pathways for sensitive file movement.
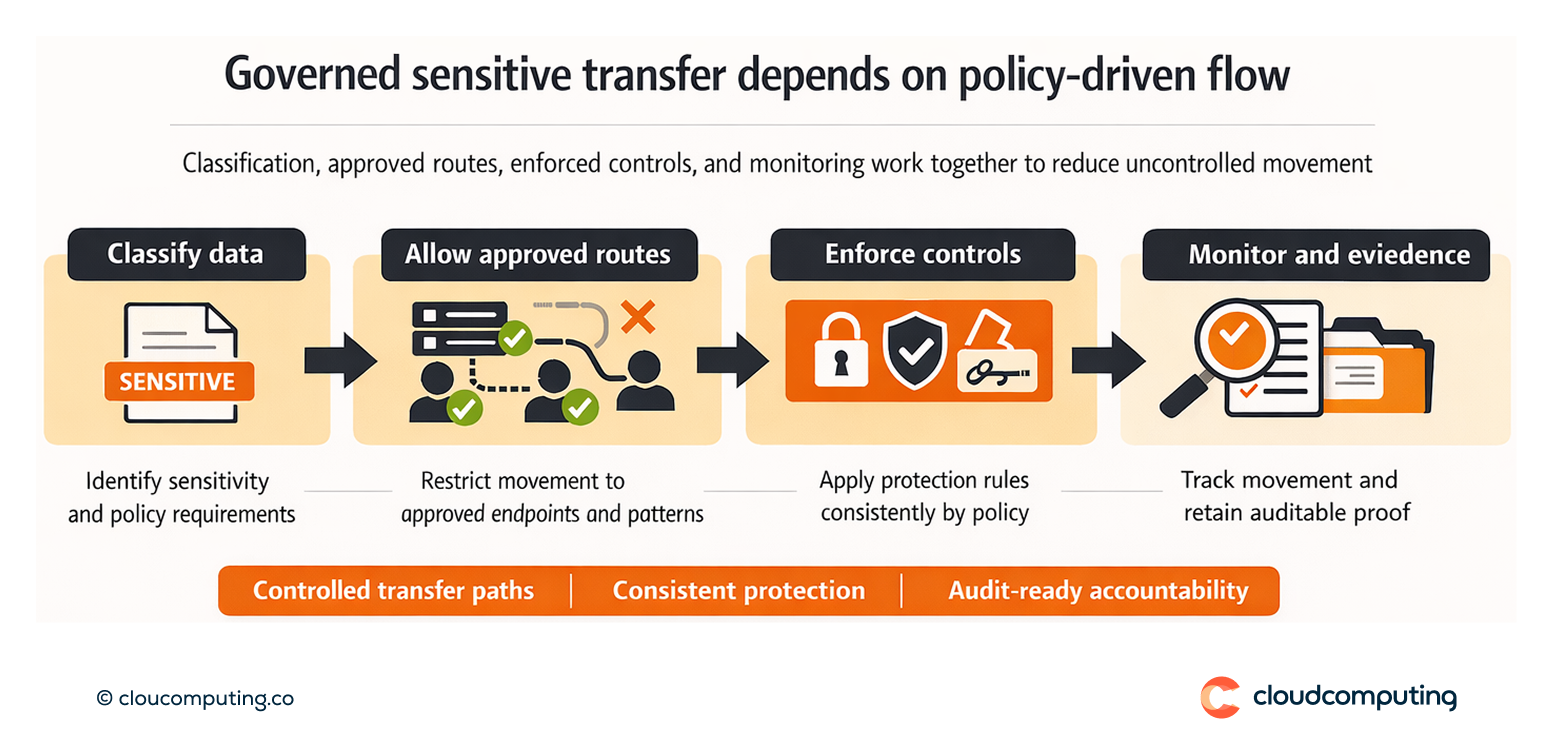
We implement policies that govern allowed routes, sender/receiver permissions, and security controls per data type.
- Policy governance model
Define who can send what to whom, using route templates and approved endpoints. - Control enforcement
Apply encryption, signing, and restrictions consistently for sensitive routes. - Operational accountability
Provide monitoring and evidence that supports accountability and investigation.
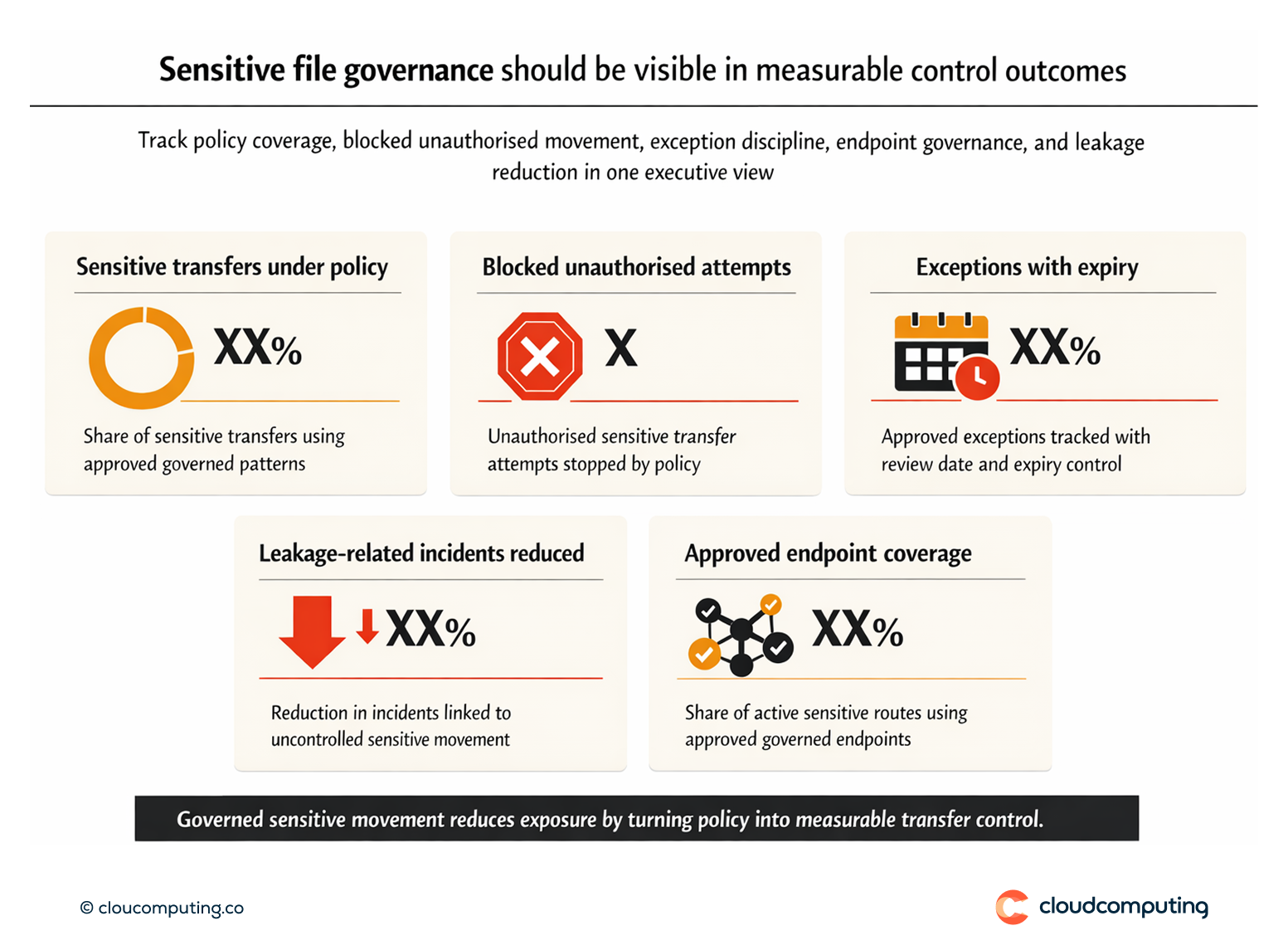
Expected outcome
- Lower data leakage risk through enforced guardrails and controlled endpoints
- Clearer accountability for sensitive file movement
- Reduced uncontrolled pathways by consolidating onto governed patterns
- Improved compliance posture with demonstrable data movement controls
Quick Answers
What is governance for sensitive file movement?
Policies that control who can transfer sensitive data, via which routes, with which security controls.
Why is unmanaged file movement risky?
It enables uncontrolled sharing, weak traceability, and inconsistent protection.
What is the first step to improve control?
Consolidate transfers onto a governed platform with standard templates and policy enforcement.
