The Problem
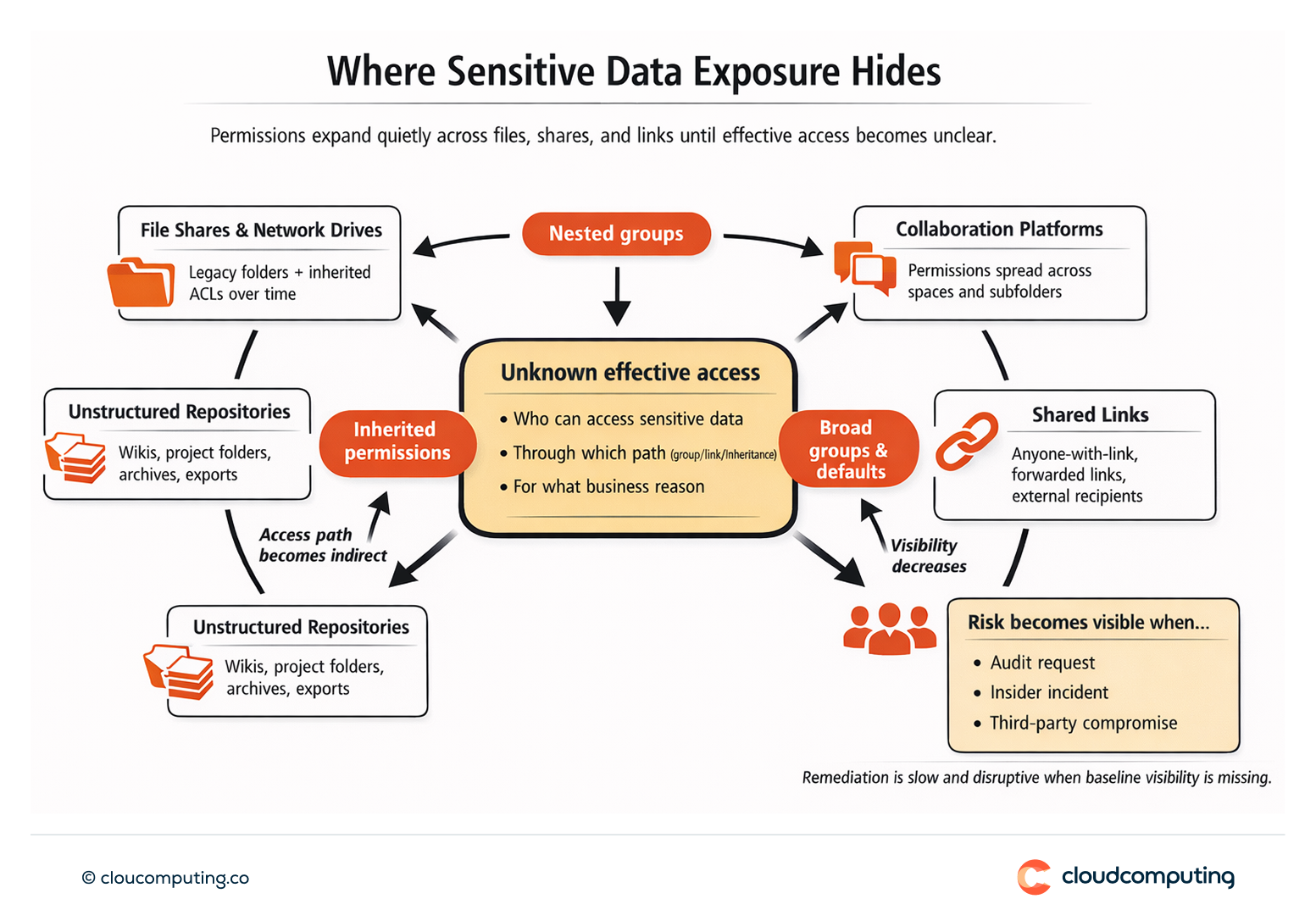
Sensitive data exposure often sits outside traditional identity governance.
File shares, collaboration platforms, and unstructured data repositories accumulate permissions over time, with limited visibility into who can access what and why. Group nesting, inherited permissions, and shared links can expand access far beyond intent.
The risk stays hidden until an audit request, an insider incident, or a third-party compromise forces investigation – at which point remediation is slow, disruptive, and difficult to validate.
How we solve it: Uncover sensitive data access risk and enforce least privilege through identity governance.
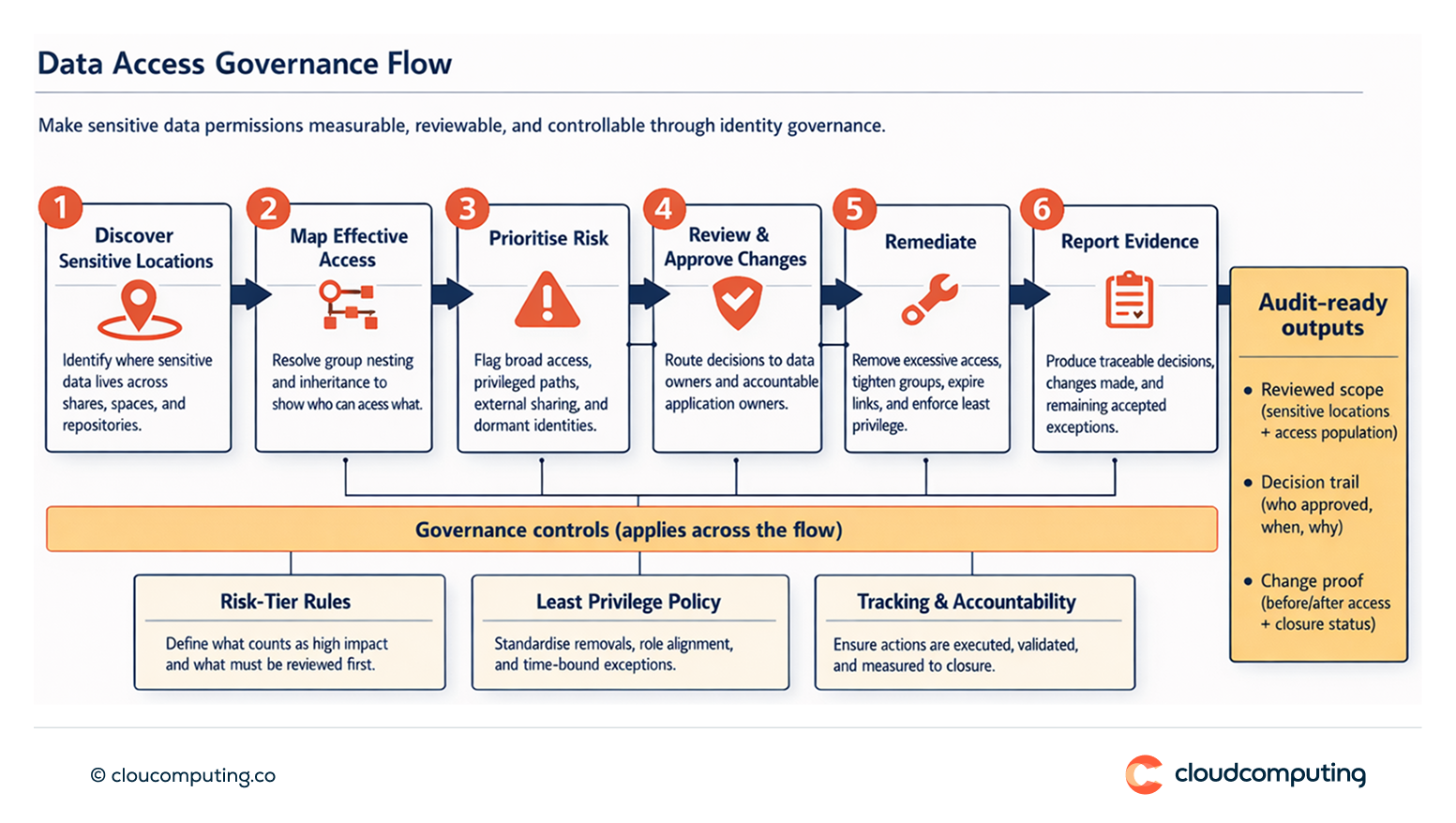
We connect data access visibility with identity governance so sensitive permissions become measurable, reviewable, and controllable through consistent processes.
- Visibility into sensitive data and permissions
We identify where sensitive data lives and map effective access, including inherited permissions and group-based access paths, to establish a defensible baseline. - Risk-tiering and prioritisation
We prioritise high-impact exposure first: broad access to sensitive locations, privileged paths, external sharing, and access held by non-employees or dormant identities. - Least privilege controls tied to identity
We reduce access surface by tightening entitlements and access paths, aligning access to roles and justified needs, and removing unnecessary broad groups and legacy permissions. - Governed reviews and remediation
We bring sensitive data access into certification and governance cycles, route reviews to the right owners (data owners and application owners), and ensure remediation actions are executed and tracked. - Evidence and operationalisation
We implement repeatable reporting so security and compliance teams can demonstrate ongoing control: what was reviewed, what changed, and what risks remain with accepted exceptions.
Expected outcome
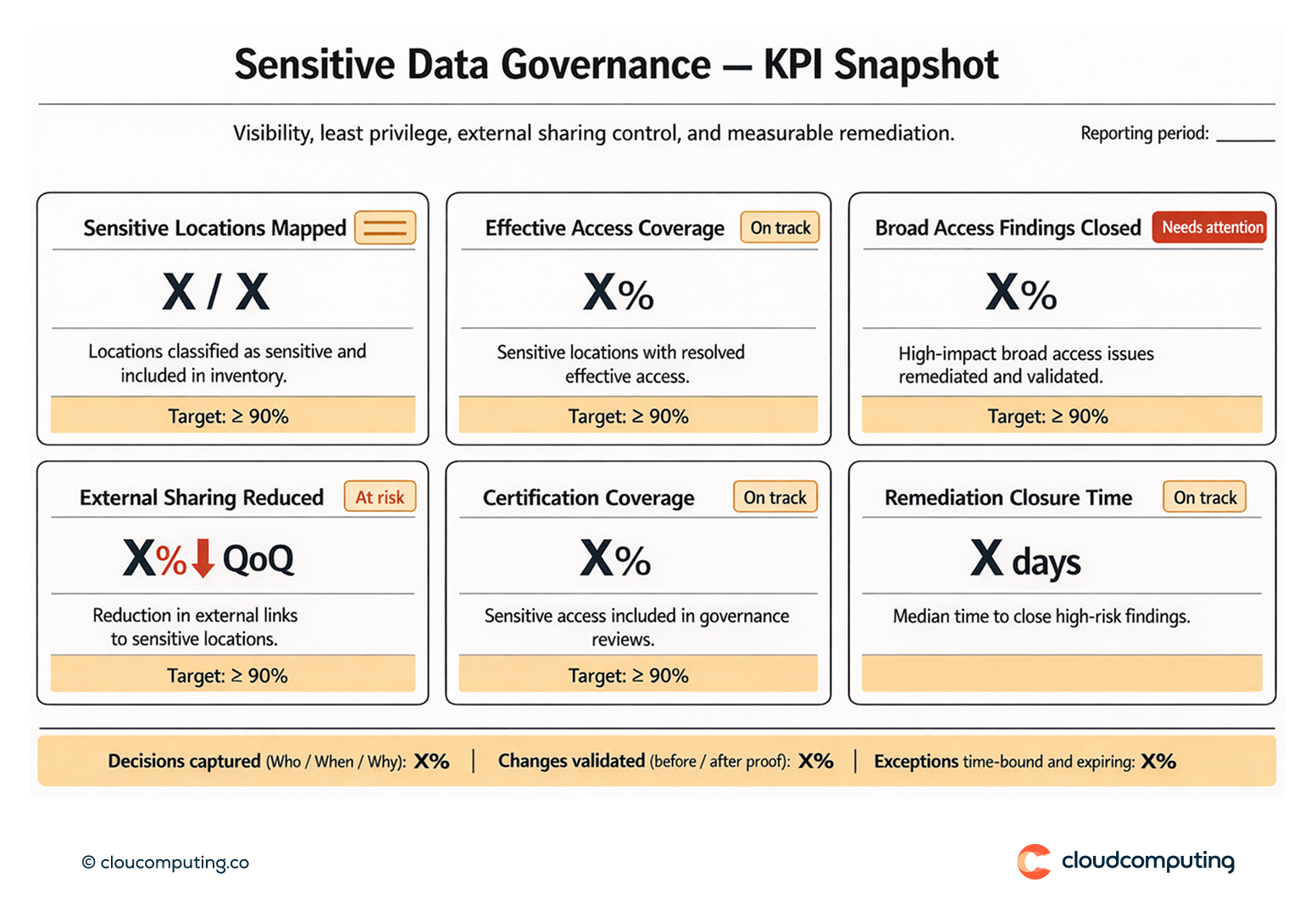
- Reduced exposure through targeted removal of unnecessary access to sensitive data
- Consistent control by bringing sensitive permissions into standard governance and review cycles
- Improved audit readiness with traceable decisions and measurable remediation
- Lower disruption by prioritising high-risk access first rather than attempting broad permission clean-ups
Quick Answers
What is data access security in identity governance?
A governance approach that makes access to sensitive files, shares, and unstructured data visible, reviewable, and controllable through identity-based controls and evidence.
Why is sensitive data exposure hard to detect?
Because access is often inherited through groups, nested permissions, and shared links, which obscures effective access paths.
How does least privilege apply to sensitive data?
Access is reduced to what is necessary for a defined role or purpose, with justified exceptions that are time-bound and traceable.