The Problem
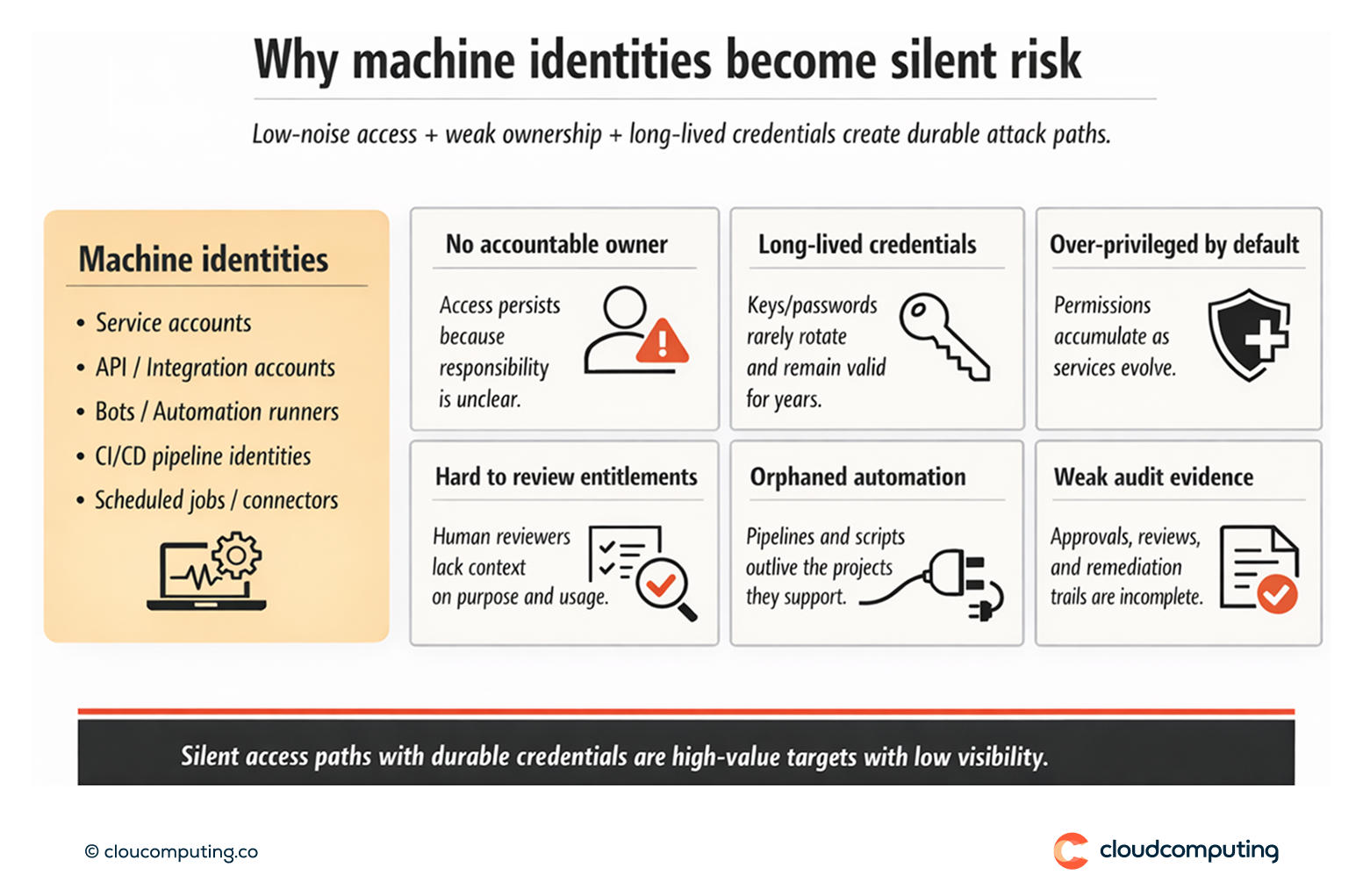
Machine identities – service accounts, APIs, bots, automation runners, and integration accounts – often outnumber human identities and operate with persistent access. Many have no clear owner, unclear purpose, and excessive privileges accumulated over time.
Credentials may be long-lived, poorly rotated, or embedded in scripts and pipelines. Because these accounts operate quietly in the background, governance gaps can persist for years, creating a high-impact attack path with limited visibility and weak audit defensibility.
How we solve it: Include machine accounts in certification and governance cycles.
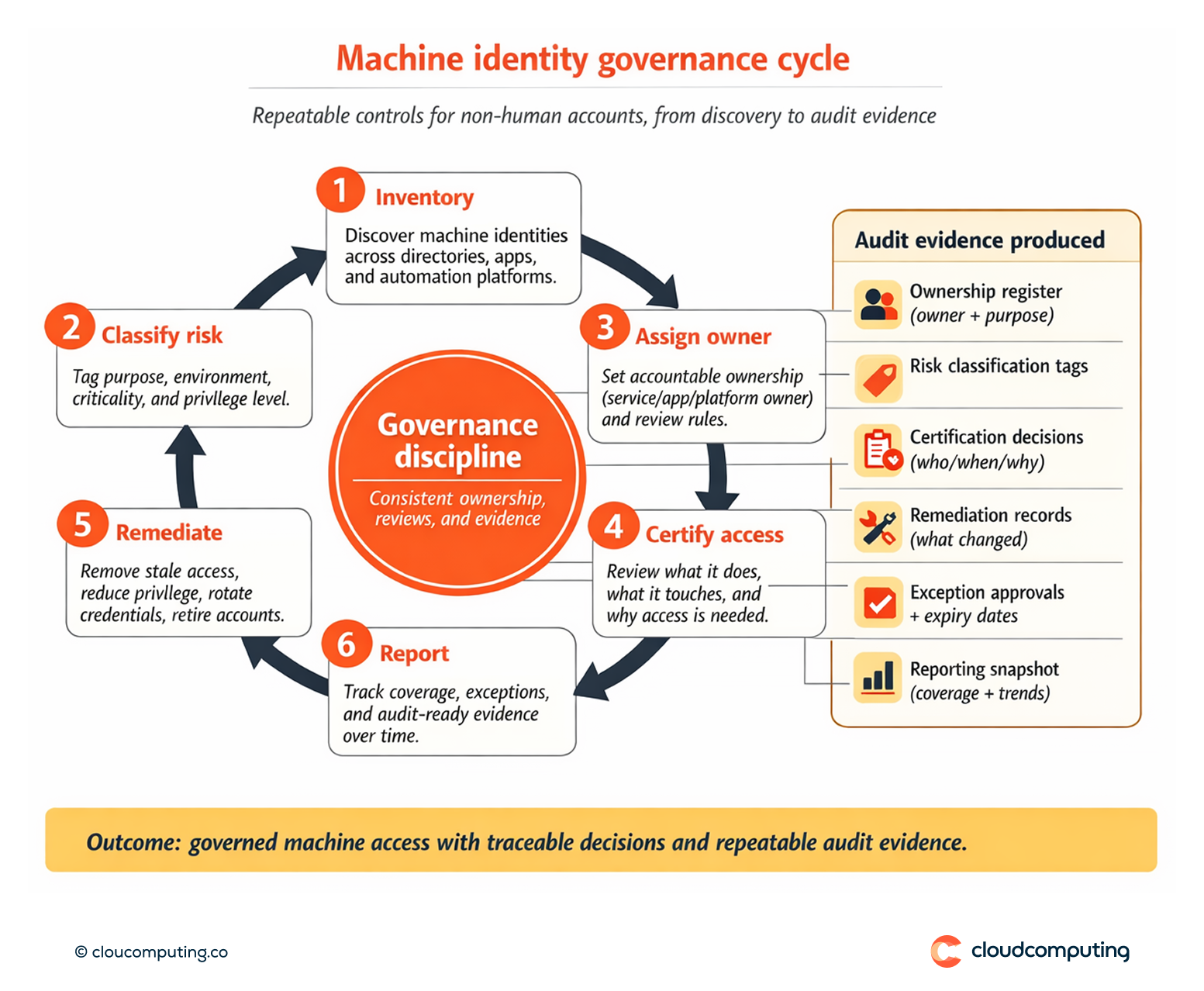
We bring machine identities into the same governance discipline as workforce identities by establishing ownership, classifying risk, certifying access, and producing traceable evidence for audits.
- Machine identity inventory and classification
We identify machine identities across key systems (directories, applications, automation platforms) and classify them by purpose, environment, and access risk. - Ownership model and accountability
We assign accountable owners to each machine identity (service owner, application owner, or platform owner), including rules for shared services and platform accounts. - Governance controls embedded into lifecycle
We define join/change/retire processes for machine identities, including naming conventions, documentation requirements, and decommissioning procedures. - Certification campaigns tailored to machine access
We include machine identities in certification cycles with reviewer context that supports defensible decisions: what the account does, what it touches, why it exists, and what “good” access looks like. - Evidence, reporting, and exception controls
We standardise evidence outputs (ownership, approvals, reviews, remediation) and enforce time bounds and exception handling for elevated machine access.
Expected outcome
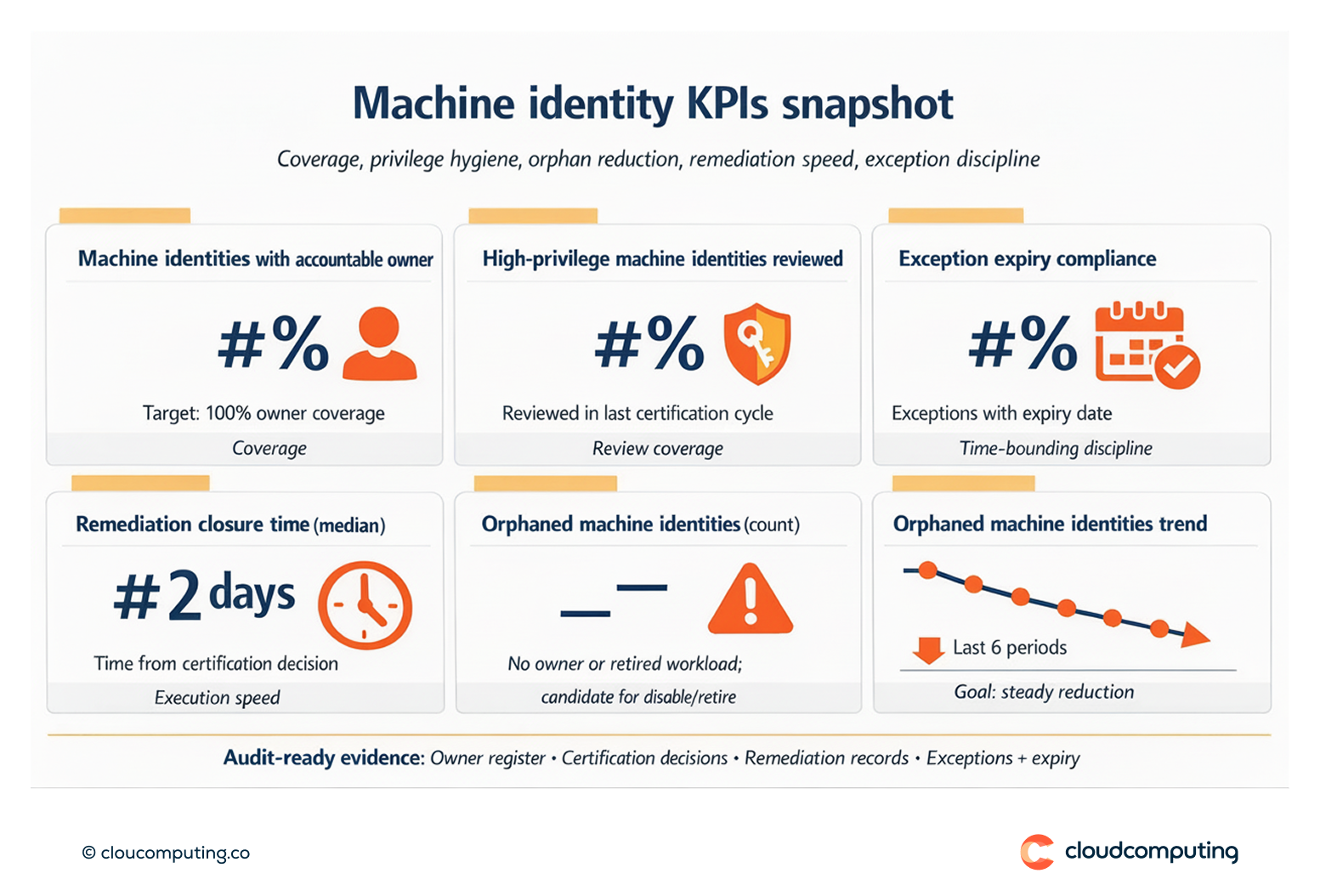
- Clear ownership for machine identities, including service accounts and automation bots
- Traceability for access decisions through approvals, certifications, and remediation evidence
- Reduced exposure by removing stale, over-privileged, or orphaned machine access
- Improved audit readiness with consistent reporting and governance coverage beyond human users
Quick Answers
What is a machine identity?
A non-human account used by applications, services, automation, or integrations to authenticate and access systems.
Why are machine accounts a security risk?
They often have persistent access, unclear ownership, and elevated permissions, and can be exploited as low-noise pathways into critical systems.
What does governance for machine identities require?
Inventory, accountable ownership, risk-based certification, and traceable evidence of access decisions and remediation.