The Problem
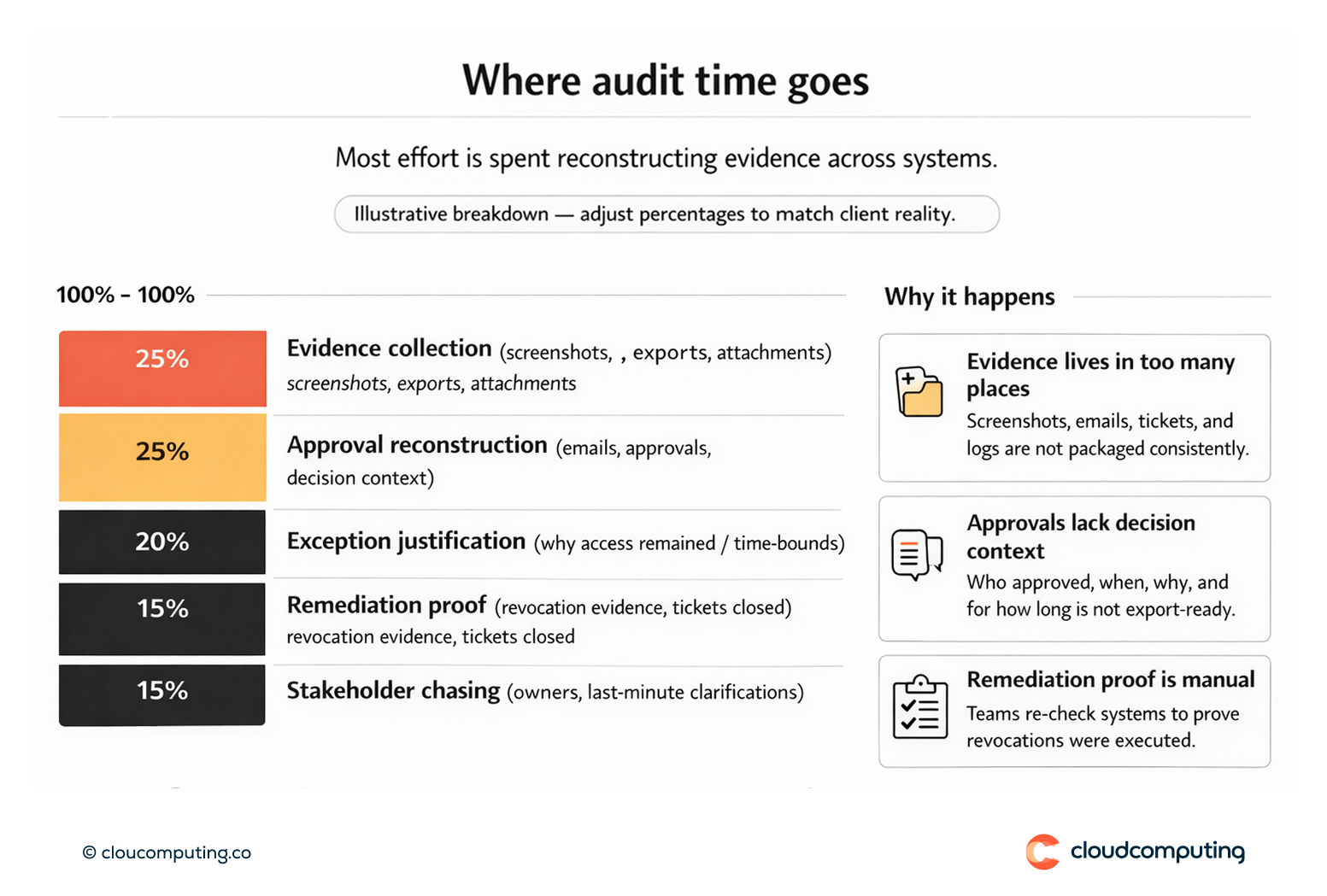
Audit requests are repetitive because evidence is inconsistent. Teams spend time pulling screenshots, reconstructing approvals from email threads, and correlating tickets across systems to explain who had access, why it was granted, and whether it was removed on time.
Security and IAM teams become the bottleneck, business owners are pulled into last-minute reviews, and audit windows disrupt normal operations. The underlying issue is rarely “lack of controls”; it is lack of traceability and a repeatable evidence pack.
How we solve it: Build approval trails, consistent evidence, and reporting that can be reused audit after audit.
We standardise evidence generation across identity processes so approvals, access changes, and review outcomes are traceable and exportable in a consistent format.
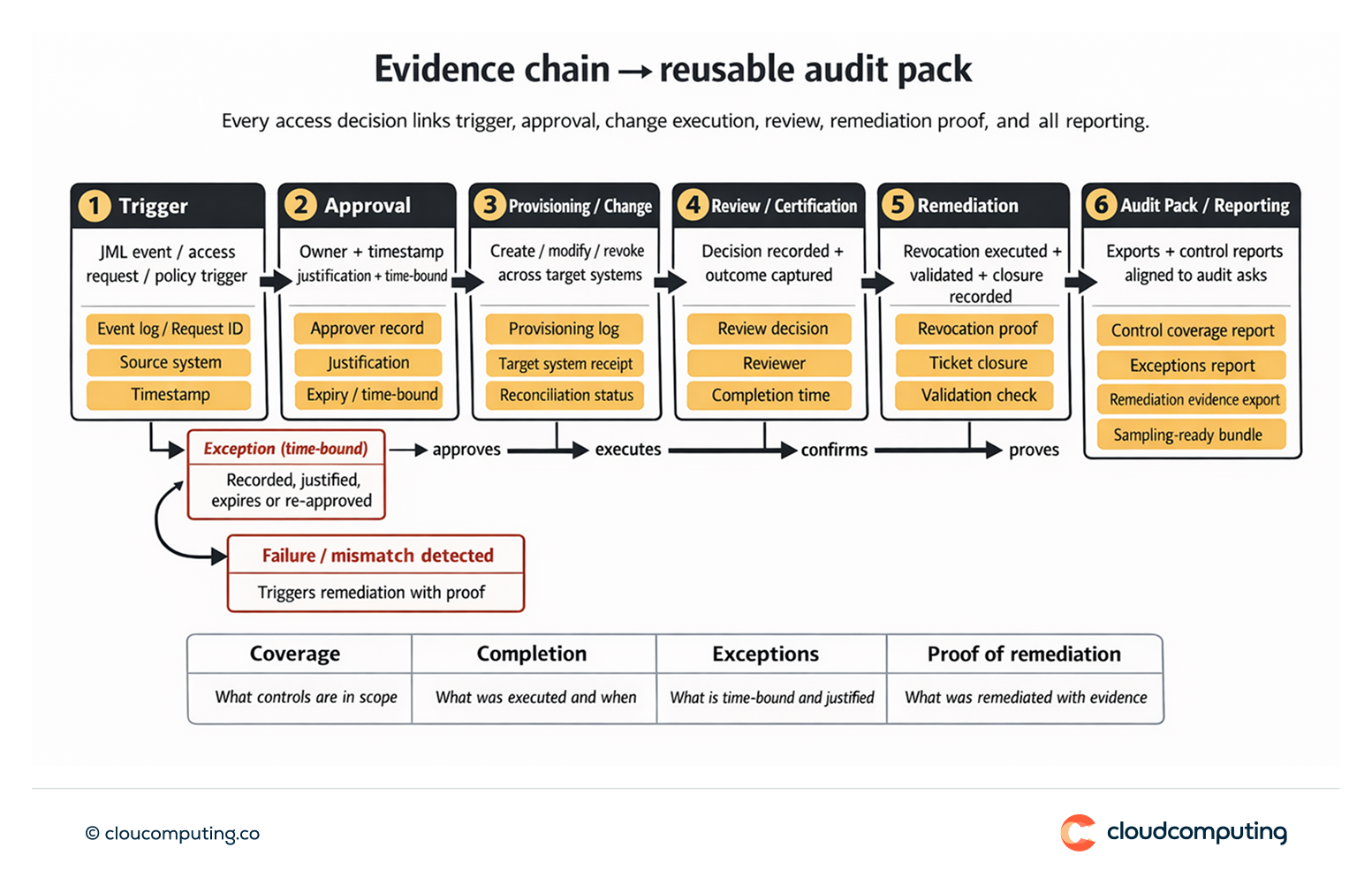
- Traceability by design
We ensure identity processes generate a complete chain of evidence: request or event trigger, approvals, provisioning actions, and any remediation or exception handling. - Consistent evidence packs
We define what “audit-ready” means for your environment and build repeatable evidence packs for core controls: JML, access requests, certifications, third-party access, and machine identities. - Approval trails and decision context
We make approvals defensible by ensuring owners are clear, decisions are time-stamped, justifications are captured where required, and time bounds are enforced for elevated access. - Reporting aligned to audit questions
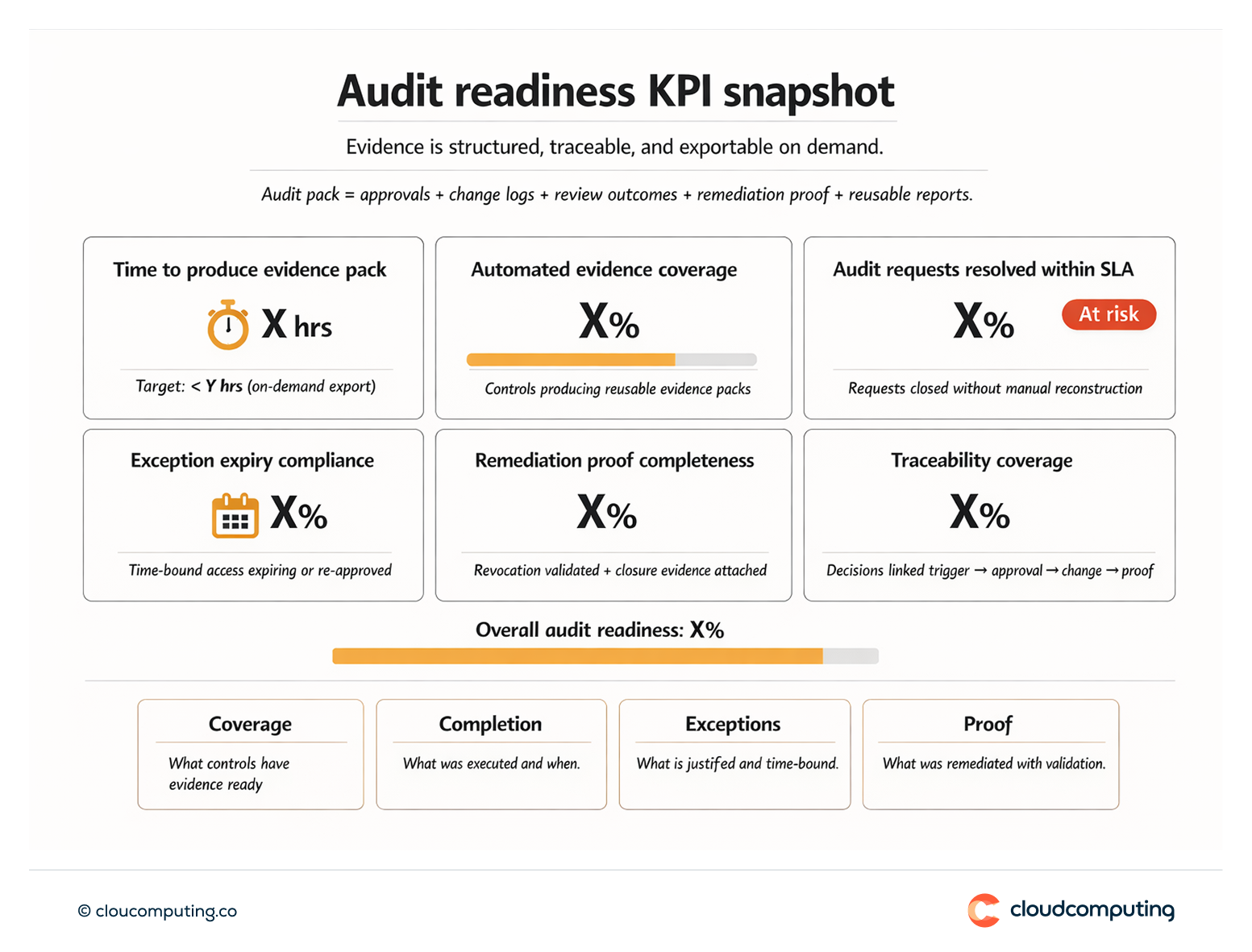
We implement reporting that answers common auditor asks quickly: coverage, completion, exceptions, and proof of remediation, without manual reconstruction. - Operational readiness
We establish runbooks and roles so evidence is generated continuously and can be produced on demand, reducing disruption during audit windows.
Expected outcome
- Faster audits because evidence is already structured and traceable
- Less friction with the business by reducing ad hoc requests to owners and last-minute reviews
- Lower operational disruption during audit windows through repeatable reporting
- Higher confidence in control narratives with consistent approval trails and remediation proof
Quick Answers
What causes audit fatigue in IAM programmes?
Manual evidence collection, inconsistent approval trails, and repeated requests to reconstruct decisions across systems.
What is “traceability” in identity governance?
The ability to link an access decision to its trigger, approvals, provisioning actions, and remediation outcomes with time-stamped evidence.
How does reporting reduce audit disruption?
By producing consistent evidence packs that answer common audit questions without manual work and stakeholder chasing.
