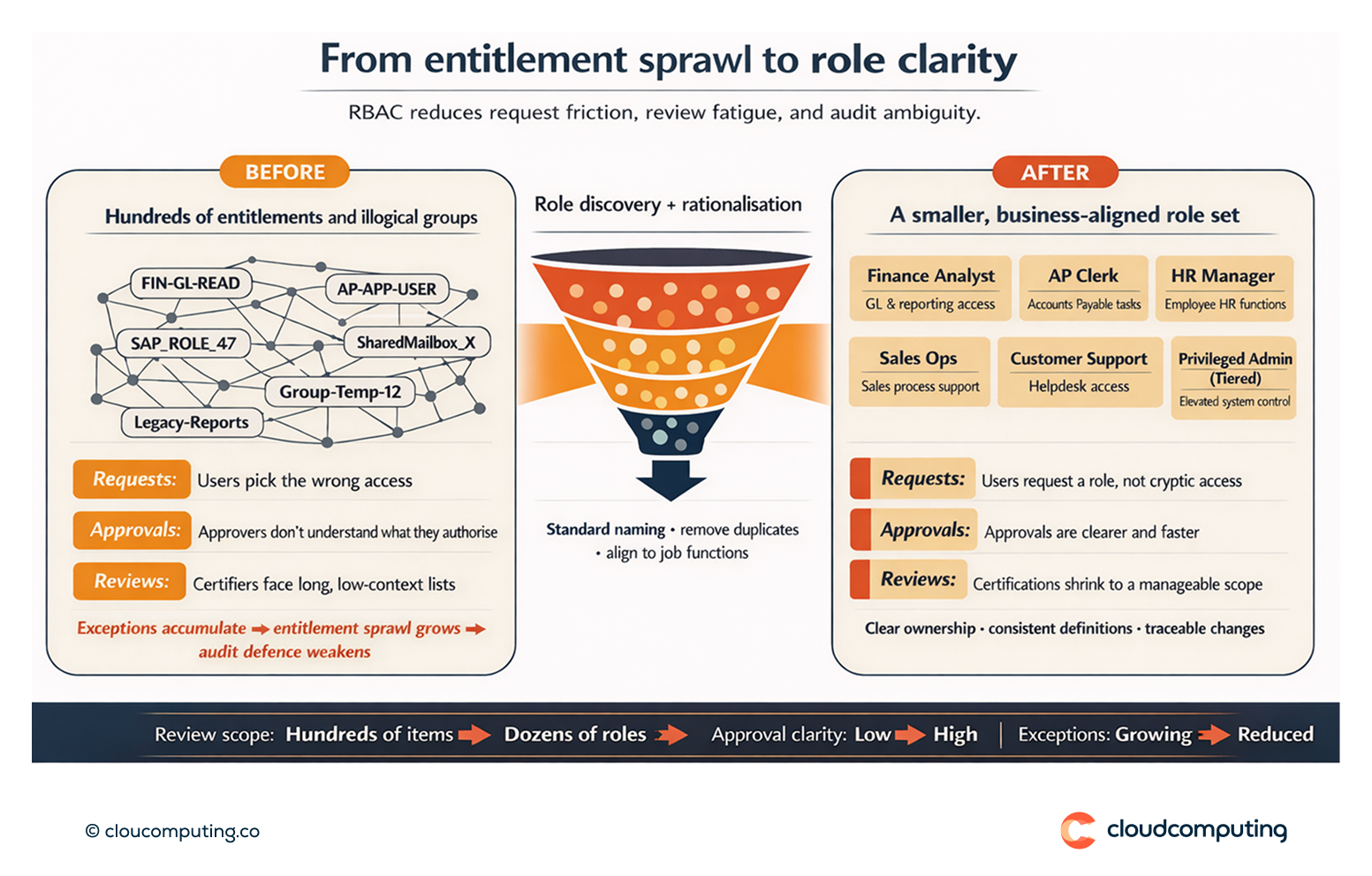
The Problem
When access is built on cryptic entitlements and illogical groups, governance slows down across the board.
Users request the wrong access because request options are unclear. Approvers struggle to understand what they are authorising. Reviews become painful because certifiers face long lists of low-context permissions rather than a manageable set of business-relevant roles.
Over time, exceptions accumulate, entitlement sprawl increases, and access governance becomes difficult to operate and difficult to defend in audits.
How we solve it: Role design and cleanup, including dynamic roles, to reduce complexity at scale.
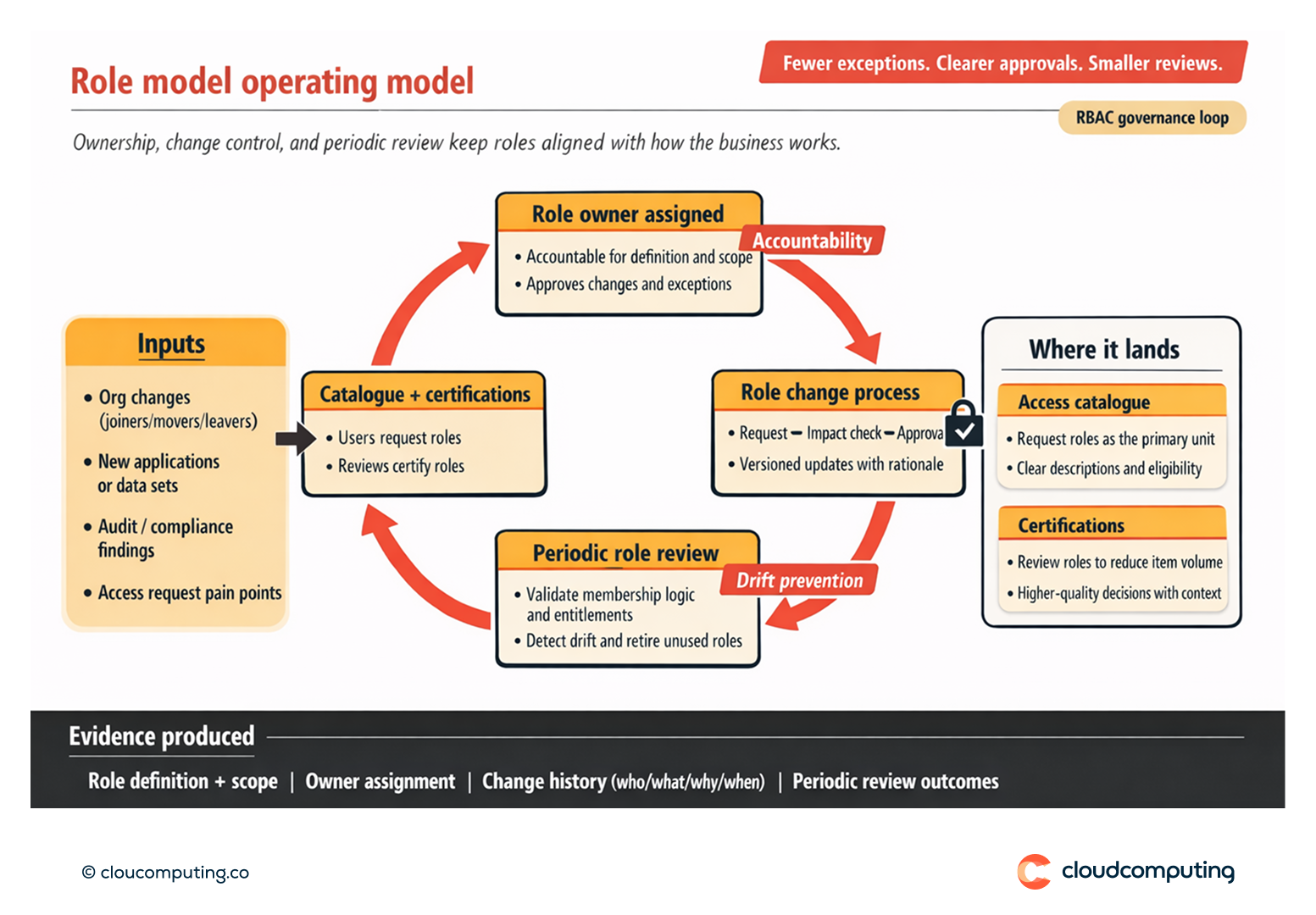
We design and operationalise a role model that reflects how the organisation works, reduces entitlement sprawl, and makes access decisions simpler for users, owners, and auditors.
- Role discovery and rationalisation
We analyse current entitlements, groups, and access patterns to identify candidates for roles, remove duplicates, and standardise naming so access is intelligible and governable. - Business-aligned role design
We define roles around job functions and responsibilities (e.g., department, location, seniority, regulated function), so access aligns to business reality rather than legacy technical structures. - Dynamic roles and attribute-driven assignment
Where appropriate, we implement dynamic role assignment using identity attributes (from HR and directories), reducing manual requests and ensuring role changes trigger immediate access adjustments. - Role lifecycle governance
We establish ownership and change control for roles, including who can request role changes, how roles are approved, and how role drift is prevented over time. - Integration with requests and certifications
We refactor the access catalogue so users request roles rather than low-level entitlements where possible, and we structure certifications around roles to reduce reviewer workload while improving decision quality.
Expected outcome
- Simpler access requests because users request clear, business-relevant roles instead of confusing entitlements
- Faster approvals with improved clarity and reduced back-and-forth
- More efficient certifications through smaller, higher-quality review scope
- Reduced entitlement sprawl and fewer permanent exceptions
- Stronger audit defensibility with clearer ownership, consistent role definitions, and traceable changes

Quick Answers
What is RBAC in identity governance?
Role-Based Access Control (RBAC) assigns access through defined roles that match job responsibilities, reducing reliance on individual entitlements and ad hoc exceptions.
Why do entitlements and groups create governance pain?
They are often technical, inconsistent, and hard to review, which increases approval friction, review fatigue, and audit risk.
What do dynamic roles change?
They allow role membership to be driven by identity attributes (e.g., department, location, employment status), reducing manual requests and keeping access aligned with organisational changes.