The Problem
Static access policies force a poor choice: either apply strict controls everywhere and slow the business down, or keep policies permissive and accept gaps where it matters most.
A “one-size-fits-all” approach cannot account for real-world context: unmanaged devices, unusual locations, risky networks, and sensitive actions performed by privileged users.
Attackers exploit this rigidity by targeting the weakest scenario, while employees experience unnecessary friction in low-risk situations.
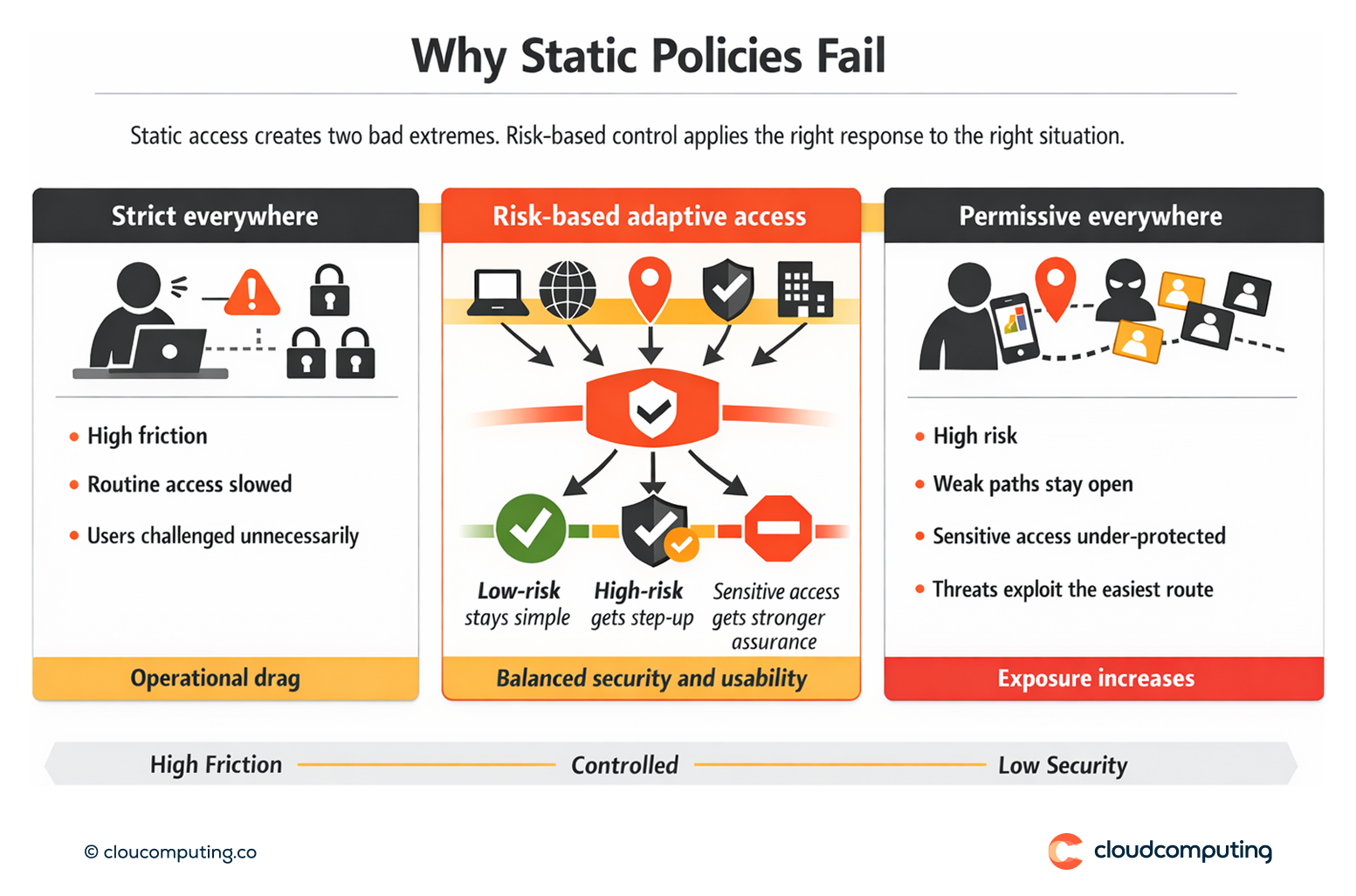
How we solve it: Apply contextual access policies and trigger step-up authentication only when risk or sensitivity increases.
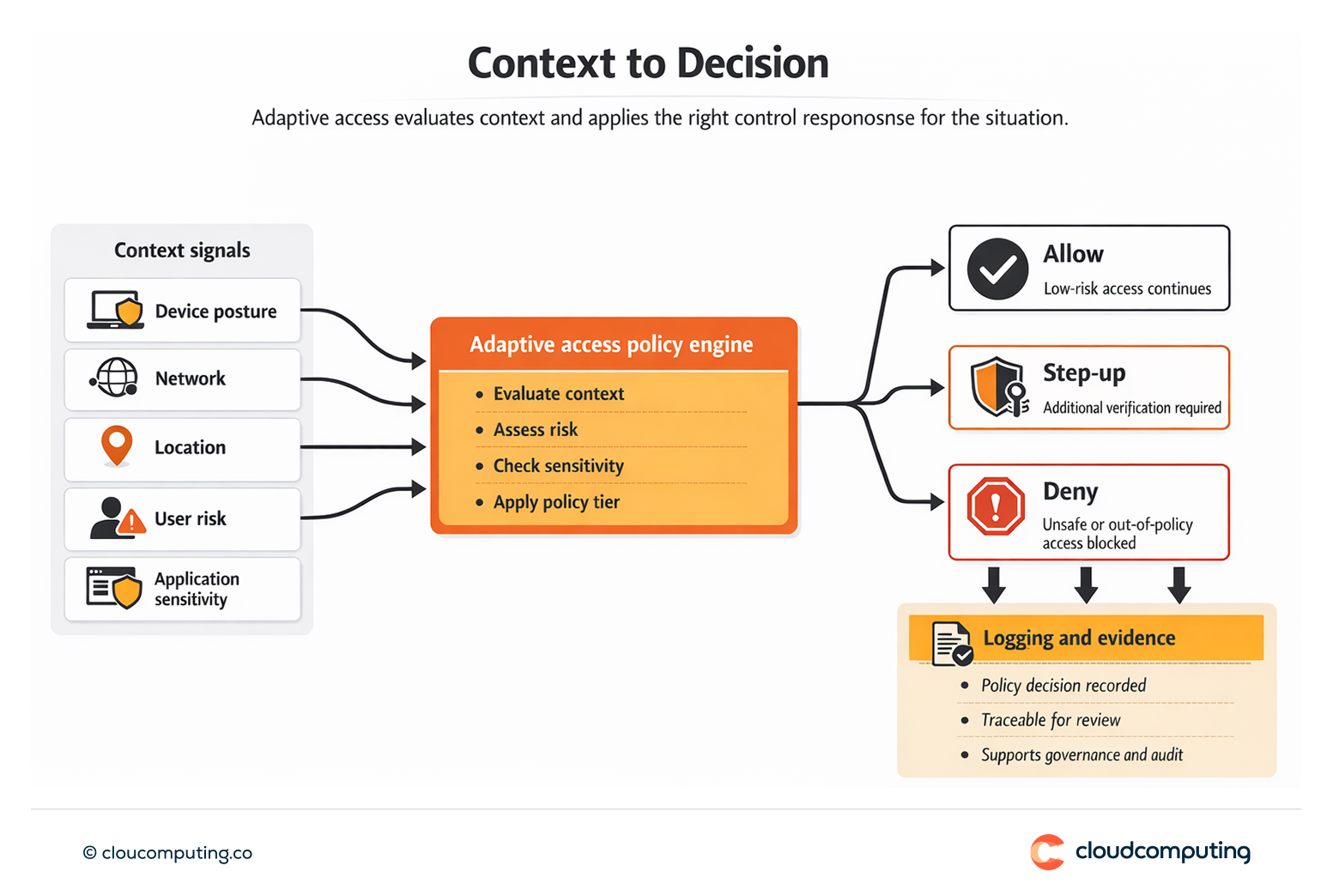
We implement adaptive access controls that evaluate context at sign-in and during sensitive actions, using step-up authentication to raise assurance when it matters.
- Define risk signals and control objectives
We align the programme to your threat model and business priorities, selecting relevant signals such as device posture, network, location, user risk, and application sensitivity. - Policy design that matches real use
We create policy tiers for standard access versus sensitive access, so everyday workflows remain smooth while high-impact access is controlled. - Step-up authentication for sensitive actions
We trigger additional verification for privileged operations, access to regulated systems, high-risk sign-in contexts, and anomalous behaviour—without applying the same friction to every session. - Exception governance and operational safety
We implement controlled bypass paths for operational continuity (e.g., travel, device replacement), with time bounds, approvals where required, and traceable evidence. - Measurement and continuous tuning
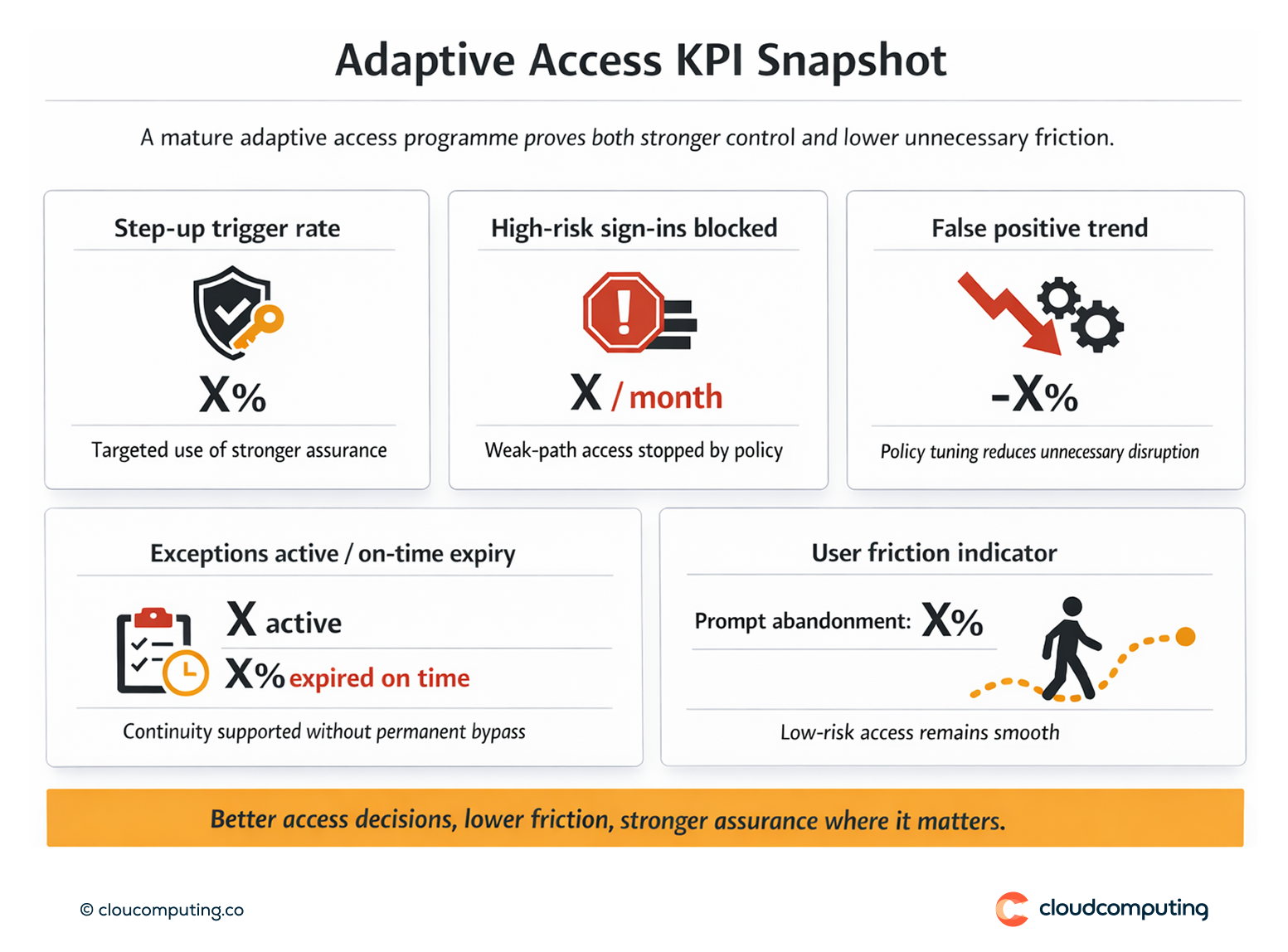
We monitor policy outcomes, false positives, and user friction indicators, then tune policies so they remain effective as the environment changes.
Expected outcome
- Stricter access when it matters through targeted step-up for high-risk contexts and sensitive actions
- Lower friction for users by keeping low-risk access simple and predictable
- Reduced exposure to account takeover by raising assurance dynamically and removing “weak path” opportunities
- Better operational reliability through controlled exception handling and policy tuning
Quick Answers
What is adaptive access?
An access approach that evaluates context—such as device posture, network, location, and risk—and applies the right control level for the situation.
What is step-up authentication?
An additional verification requirement triggered only when risk increases or a user attempts a sensitive action.
Why does risk-based access reduce friction?
Because it avoids applying maximum controls to every session while still raising assurance for high-impact access paths.