The Problem
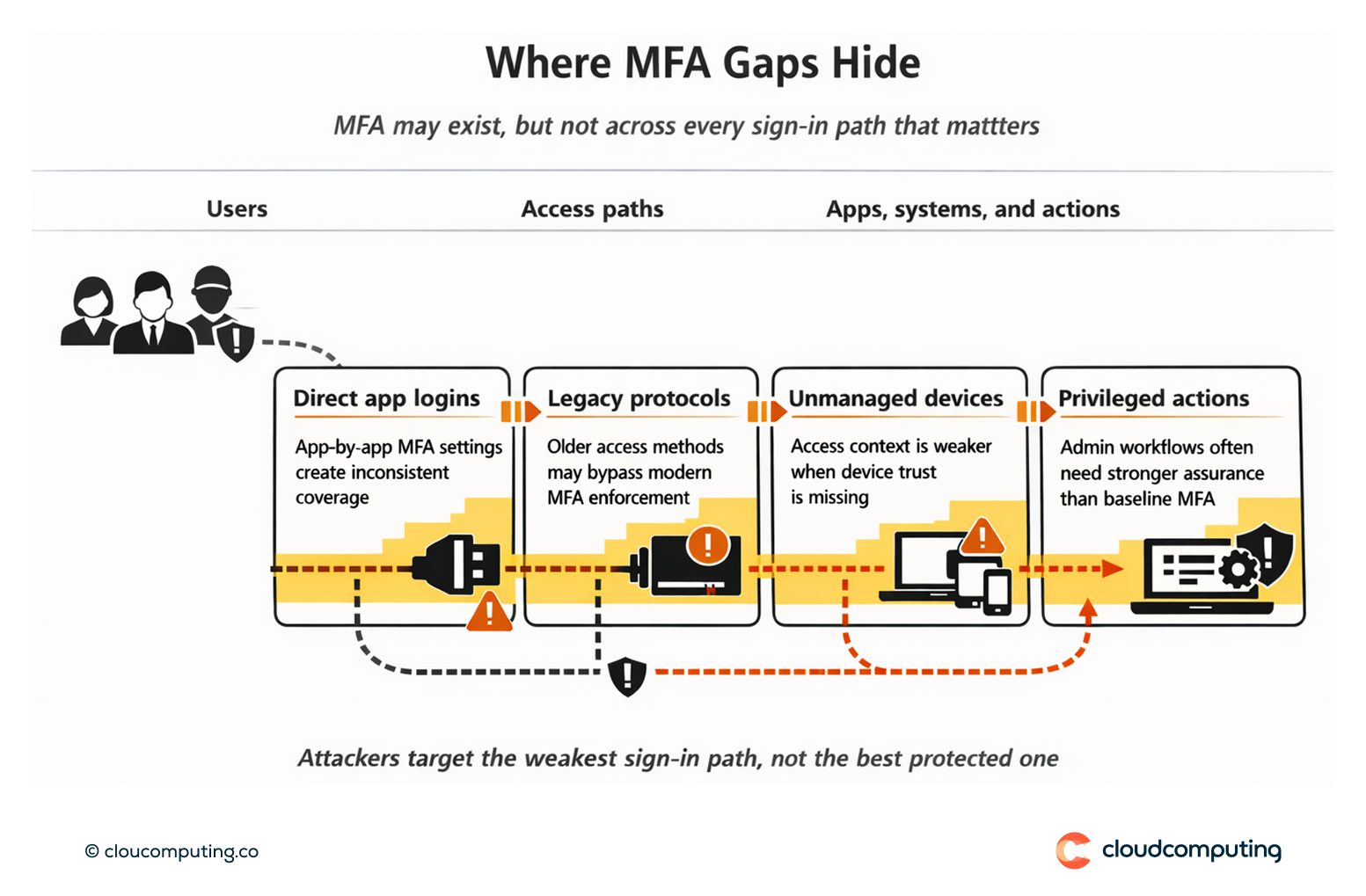
Most organisations have MFA, but not everywhere it matters. Coverage gaps across cloud apps, legacy access paths, and admin workflows leave openings for credential theft and phishing-based account takeover.
In parallel, inconsistent MFA policies create user friction in low-risk scenarios while still failing to raise assurance for high-risk actions.
The outcome is predictable: attackers target the weakest sign-in path, and security teams inherit incidents that could have been prevented with consistent policy and stronger authentication for sensitive access.
How we solve it: Enforce consistent MFA policies and use phishing-resistant methods where assurance must be highest.
We implement MFA as a coherent programme across applications and access paths, raising assurance for sensitive actions while reducing unnecessary prompts for low-risk access.
- MFA baseline coverage across the estate
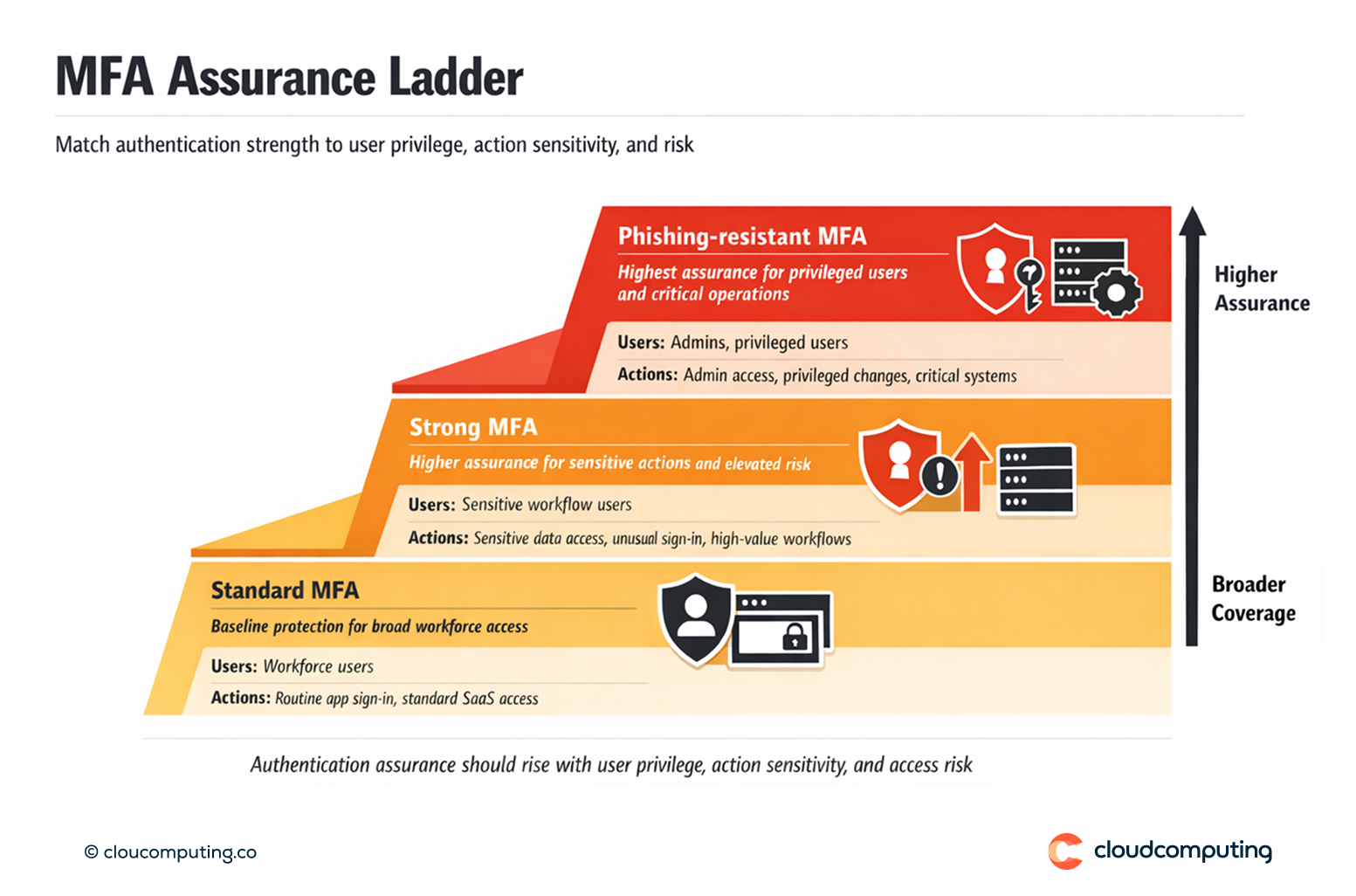
We establish consistent MFA requirements across workforce apps under a central identity layer, closing gaps created by app-by-app configurations. - Phishing-resistant MFA for privileged and high-impact access
We apply higher-assurance methods for admins, privileged users, and sensitive systems, reducing exposure to phishing and token theft techniques. - Step-up authentication for sensitive actions
We increase assurance when risk is higher: privileged changes, access to regulated data, unusual sign-in context, or high-value applications. - Policy enforcement and exception handling
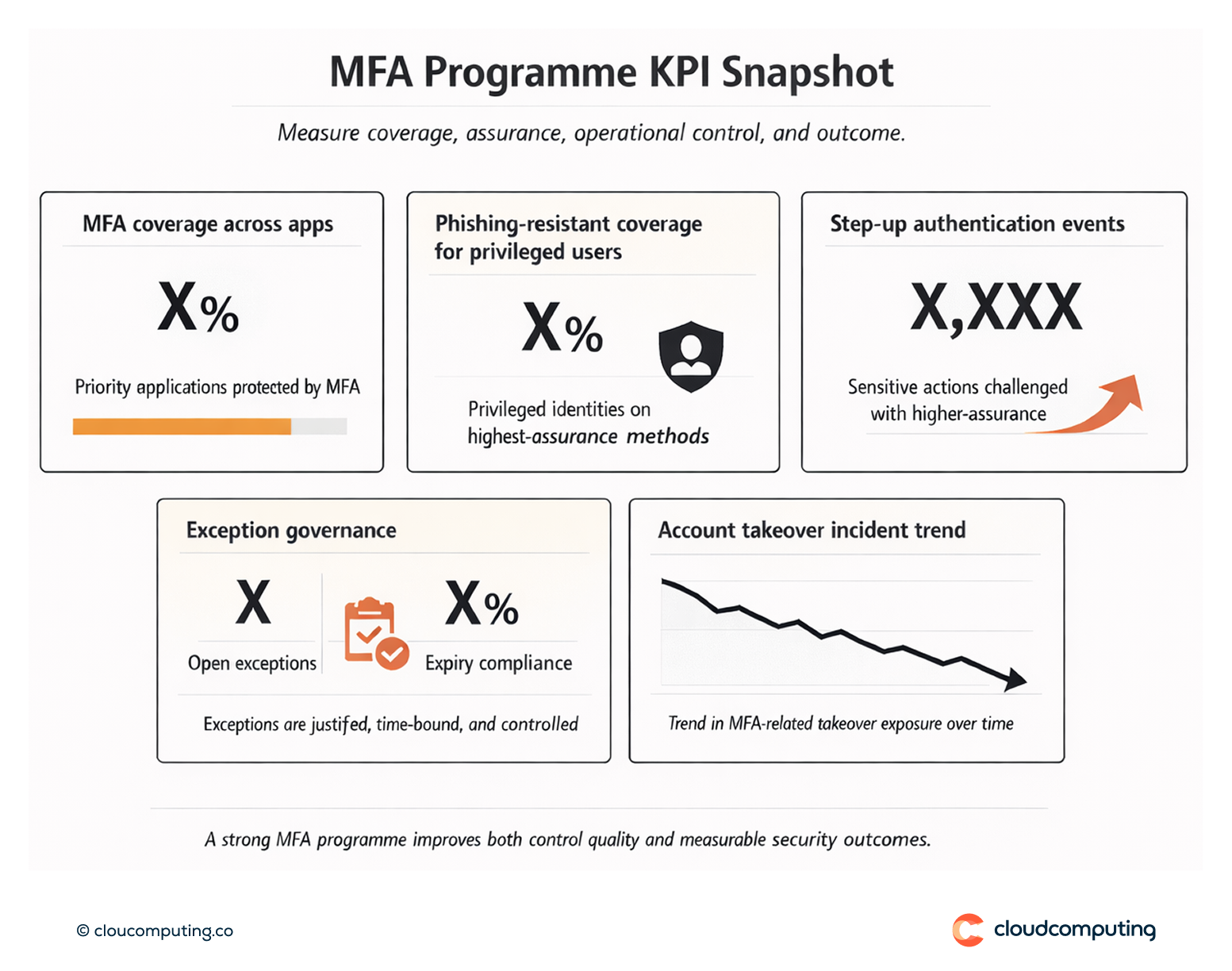
We define controlled exceptions with governance: justified, time-bound, and reviewable. MFA becomes predictable for users and defensible for audits. - Adoption and operational readiness
We plan enrolment, user comms, support workflows, and metrics so MFA rollout does not stall at the “last mile.”
Expected outcome
- Reduced account takeover risk by removing MFA gaps and increasing assurance where it matters most
- Lower user friction by avoiding unnecessary prompts in low-risk scenarios and applying step-up only when required
- Consistent enforcement across SaaS and priority access paths through centralised policy
- Improved audit defensibility with documented controls, exception governance, and traceable policy outcomes
Quick Answers
What does “strong MFA everywhere” mean?
Consistent MFA enforcement across applications and sign-in paths, with higher-assurance methods applied to privileged and sensitive access.
What is phishing-resistant MFA?
Authentication methods designed to resist common phishing techniques by binding authentication to the legitimate service and reducing replayable factors.
How do you reduce friction while strengthening MFA?
By applying risk-based policies and step-up authentication—raising assurance for sensitive actions and keeping low-risk access simpler.
