The Problem
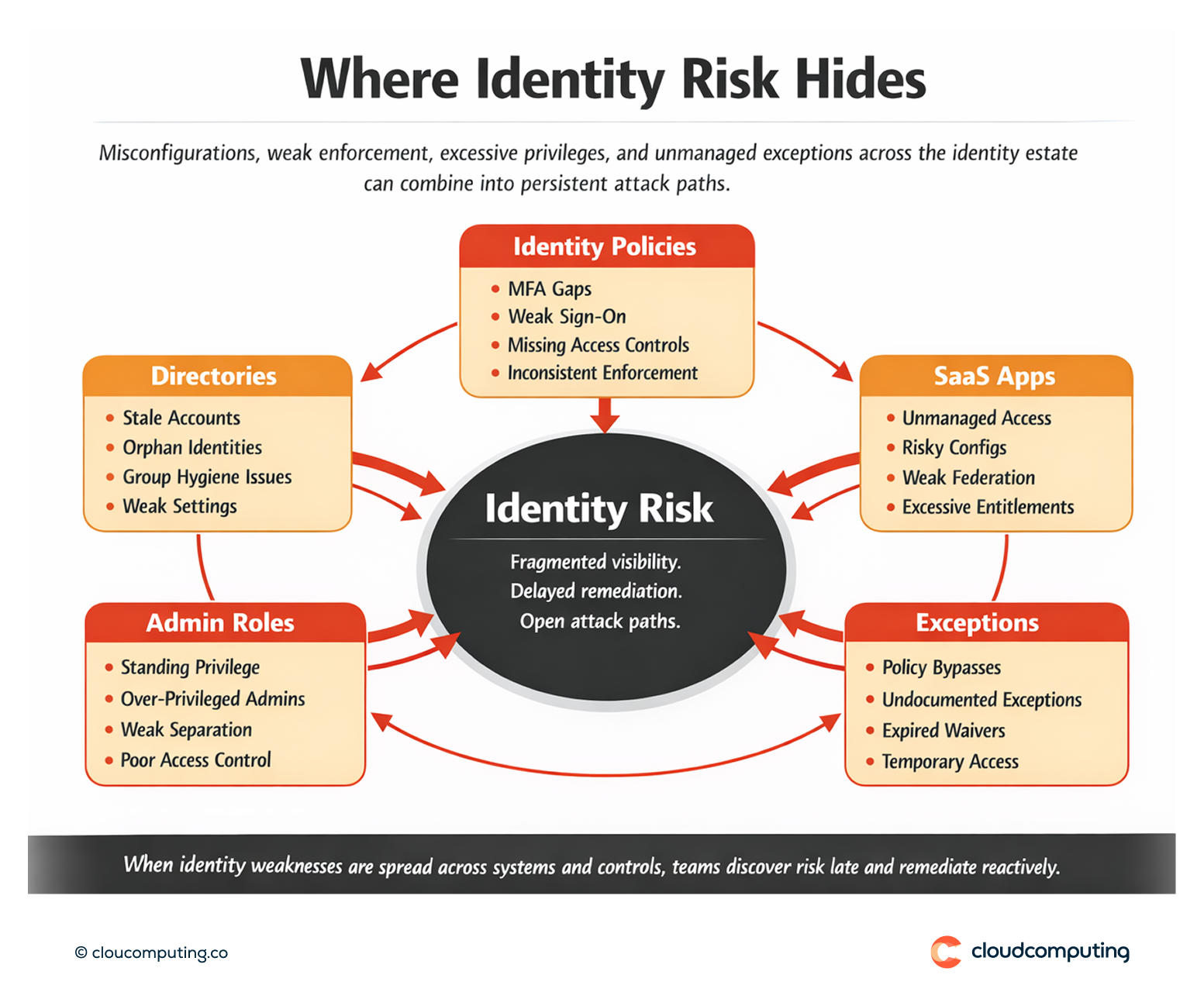
Identity risk is rarely contained in one place. Misconfigurations, weak policies, excessive privileges, and inconsistent controls are spread across directories, SaaS applications, and identity platforms.
Visibility is fragmented, so teams discover gaps late -during audits, after incidents, or when a point-in-time review misses a fast-moving change.
The result is predictable: identity-based attack paths remain open longer than they should, remediation is reactive, and leadership lacks a measurable view of identity posture over time.
How we solve it: Use Okta ISPM to continuously assess identity posture, prioritise exposures, and drive remediation with actionable recommendations.
We implement Okta Identity Security Posture Management (ISPM) as a continuous control layer that identifies risky configurations and exposures, prioritises what to fix first, and supports measurable posture improvement.
- Continuous posture assessment
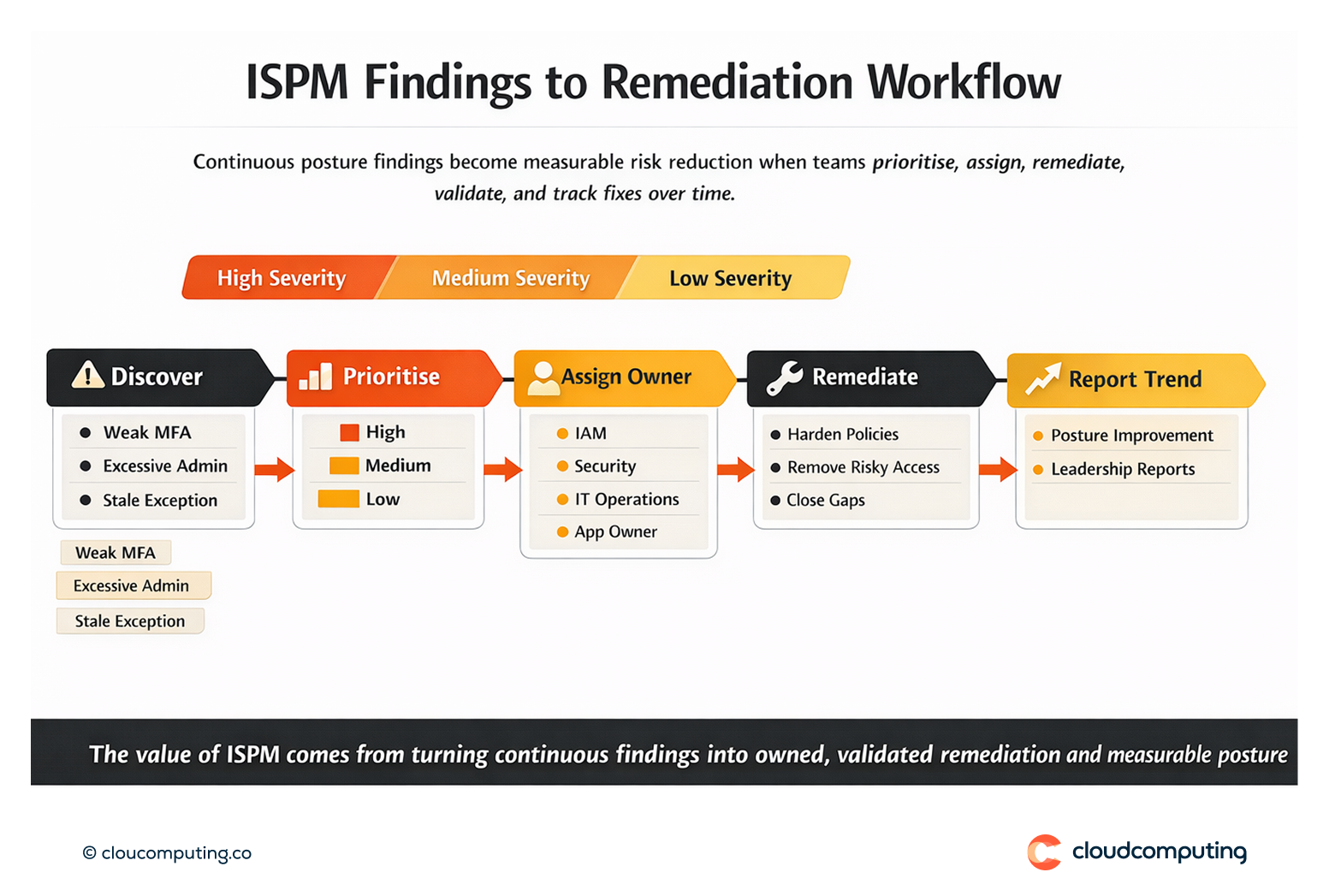
We establish ongoing posture visibility across identity configuration and control coverage, reducing reliance on periodic reviews and audit-driven discovery. - Risk-based prioritisation
We focus attention on the findings that materially increase exposure—misconfigurations, weak enforcement, excessive privileges, and risky exceptions—so teams spend effort where it reduces attack paths. - Actionable remediation guidance
We translate findings into remediation actions: policy changes, control hardening, reduction of risky access, and closure of configuration gaps. - Operational workflows and ownership
We define who owns which classes of remediation (IAM, security, IT operations, application owners) and how fixes are tracked to completion. - Metrics and governance
We establish posture metrics and reporting that leadership can use: trend over time, remediation velocity, and reduction in high-risk exposures.
Expected outcome
- Continuous visibility of identity risk across configuration, policy enforcement, and control gaps
- Faster remediation through prioritised findings and clear ownership
- Stronger compliance readiness by addressing issues before audits force discovery
- Measurable reduction in identity-based attack paths through posture improvement tracked over time

Quick Answers
What is Identity Security Posture Management (ISPM)?
A continuous approach to assessing identity configuration and control effectiveness, identifying exposures and misconfigurations, and tracking remediation over time.
Why do identity risks persist even with SSO and MFA?
Because misconfigurations, exceptions, excessive privileges, and inconsistent policy enforcement can still create attack paths across apps and directories.
What does Okta ISPM change operationally?
It provides continuous visibility and prioritised findings so teams can remediate the highest-impact identity exposures before audits or incidents reveal them.
