The Problem
It is difficult to prove who sent what, when, and to whom—especially under audit pressure.
Logs may be incomplete, spread across systems, or not tamper-evident.
Chain-of-custody evidence is often reconstructed manually, increasing audit fatigue and operational disruption.
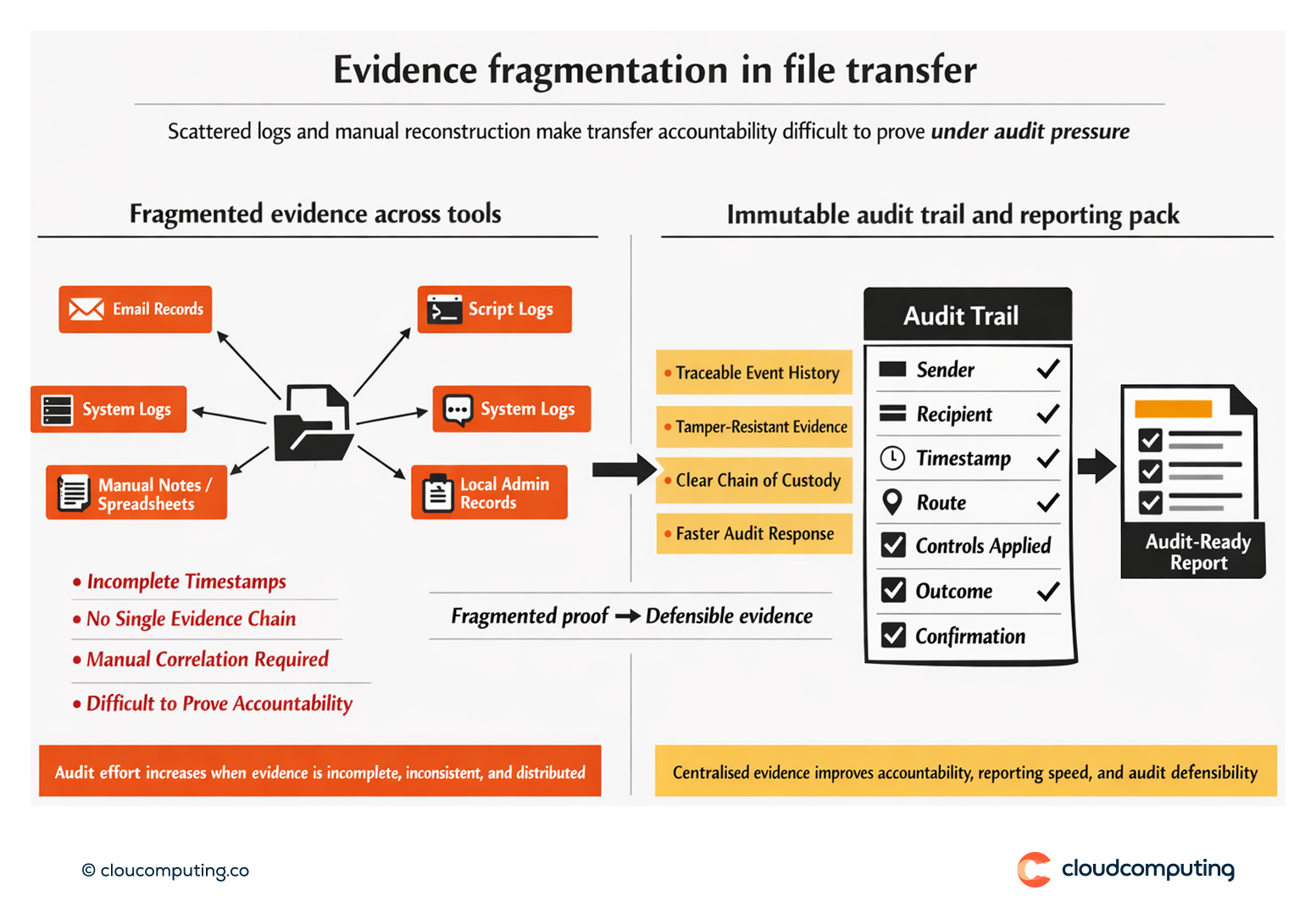
How we solve it: Enable immutable logs, chain-of-custody evidence, and audit-ready reporting in Axway MFT.
We implement an evidence model that produces traceable, tamper-resistant logs and reporting aligned to compliance needs.
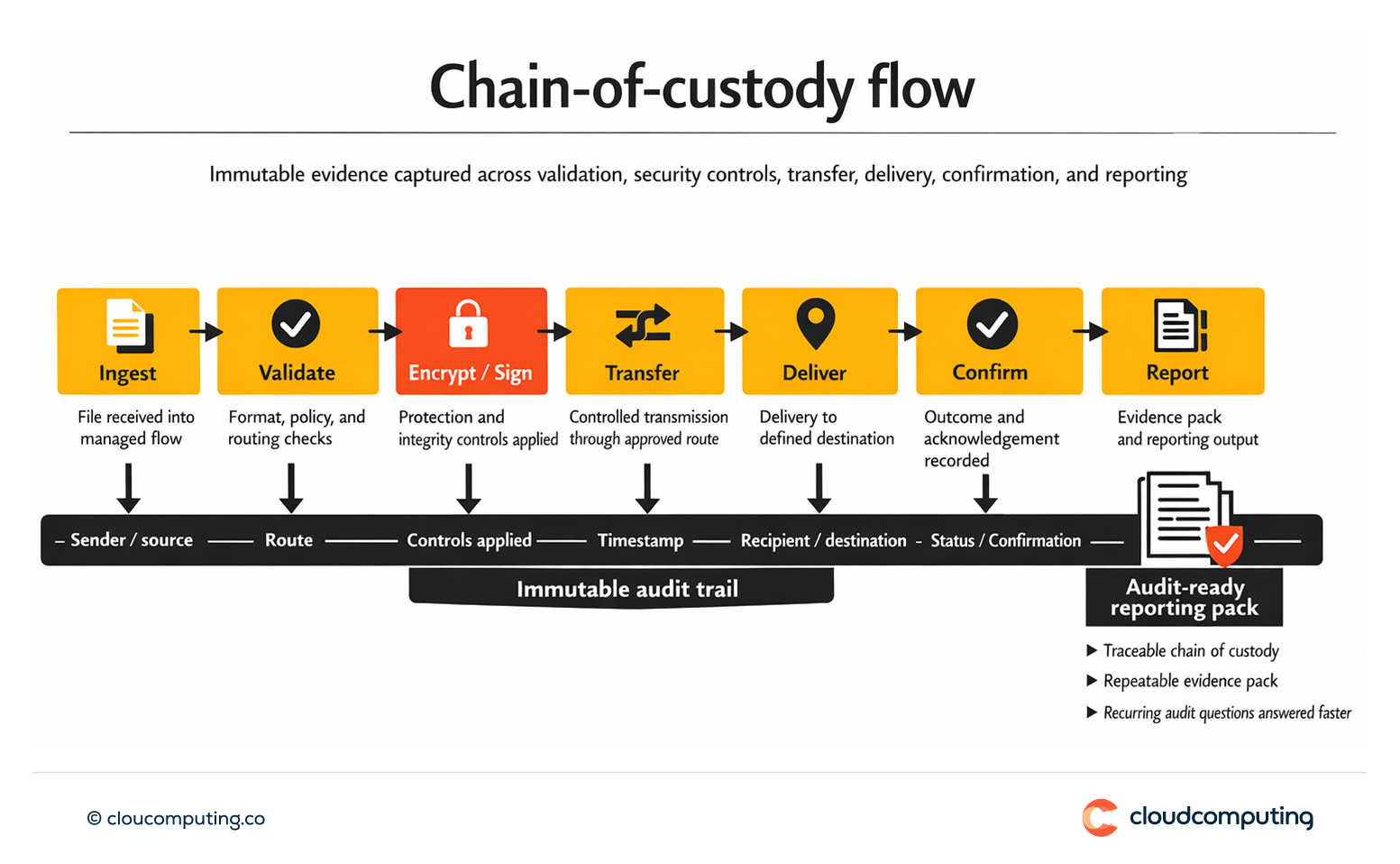
- Immutable audit trail configuration
Enable logging that captures sender, recipient, route, timestamps, controls applied, and outcomes. - Chain-of-custody evidence
Maintain end-to-end traceability across steps, including retries and downstream handoffs where integrated. - Audit-ready reporting packs
Provide standard reports for recurring audit questions, reducing manual reconstruction.
Expected outcome
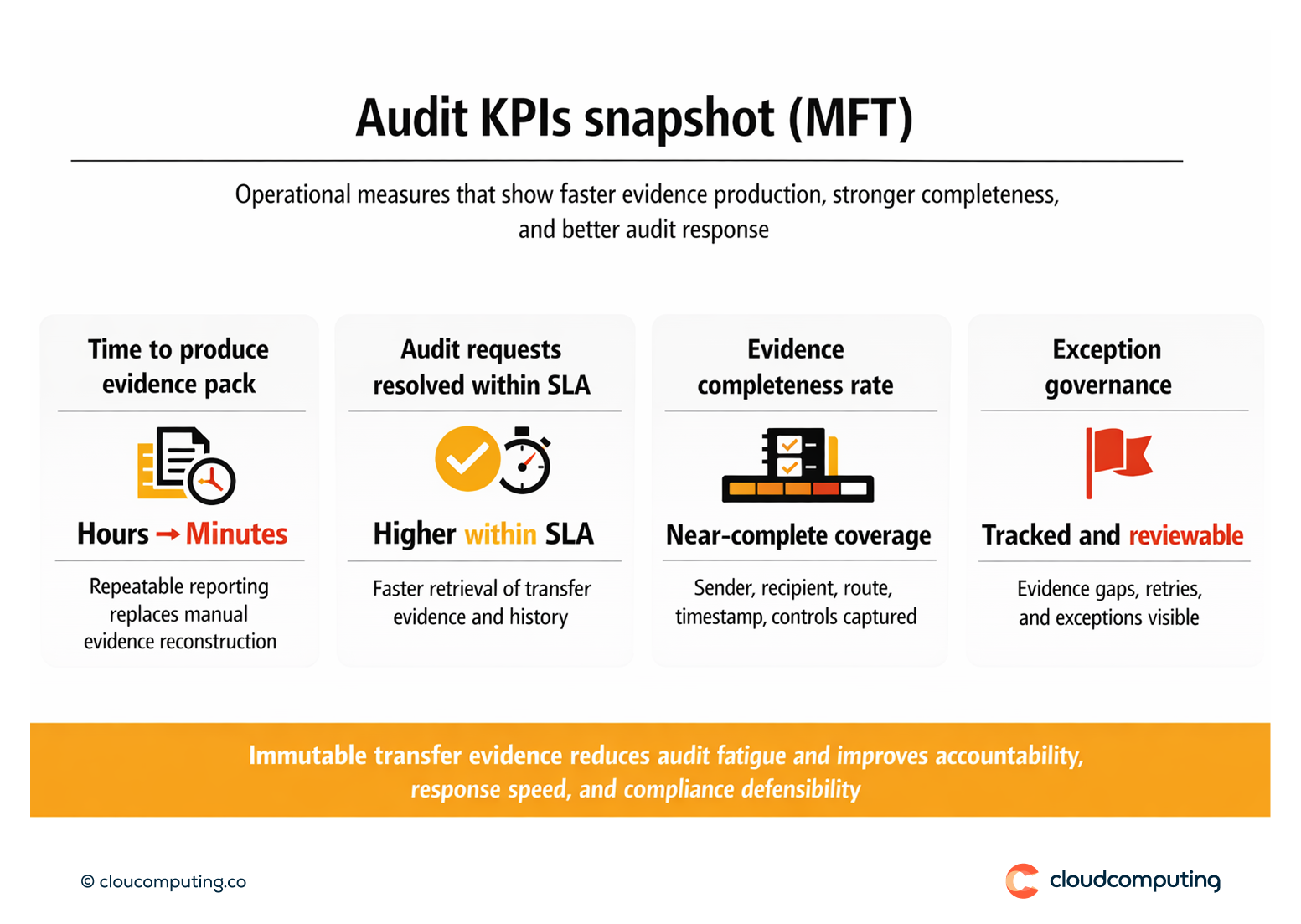
- Faster audits through repeatable reporting and clear evidence packs
- Stronger evidence of transfer accountability and control enforcement
- Reduced audit fatigue by removing manual log correlation
- Improved compliance posture through defensible chain-of-custody
Quick Answers
What is non-repudiation in file transfer?
Evidence that a transfer occurred with attributable sender and recipient, with integrity controls where required.
Why are audits hard with unmanaged transfers?
Because logs are incomplete, inconsistent, and often not tamper-evident, requiring manual reconstruction.
What changes with Axway MFT reporting?
Audit evidence becomes repeatable, centralised, and aligned to compliance needs.
