The Problem
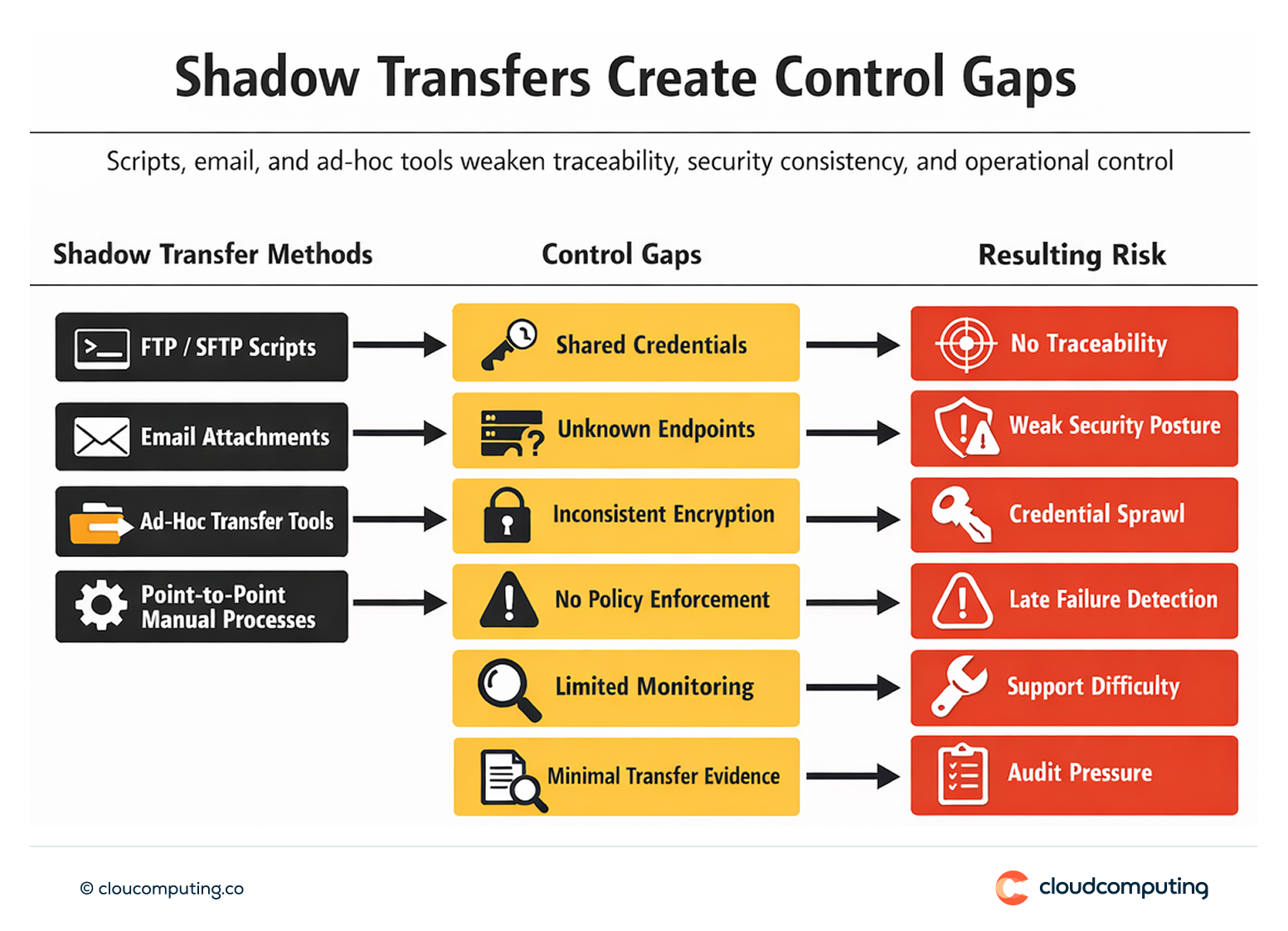
Uncontrolled file transfers create systemic risk.
Scripts and point-to-point FTP/SFTP flows rely on shared credentials, informal endpoints, and inconsistent encryption. Email and ad-hoc tools provide limited traceability and weak governance.
When something fails, teams often discover it late, with limited evidence of what was sent, to whom, and under which controls.
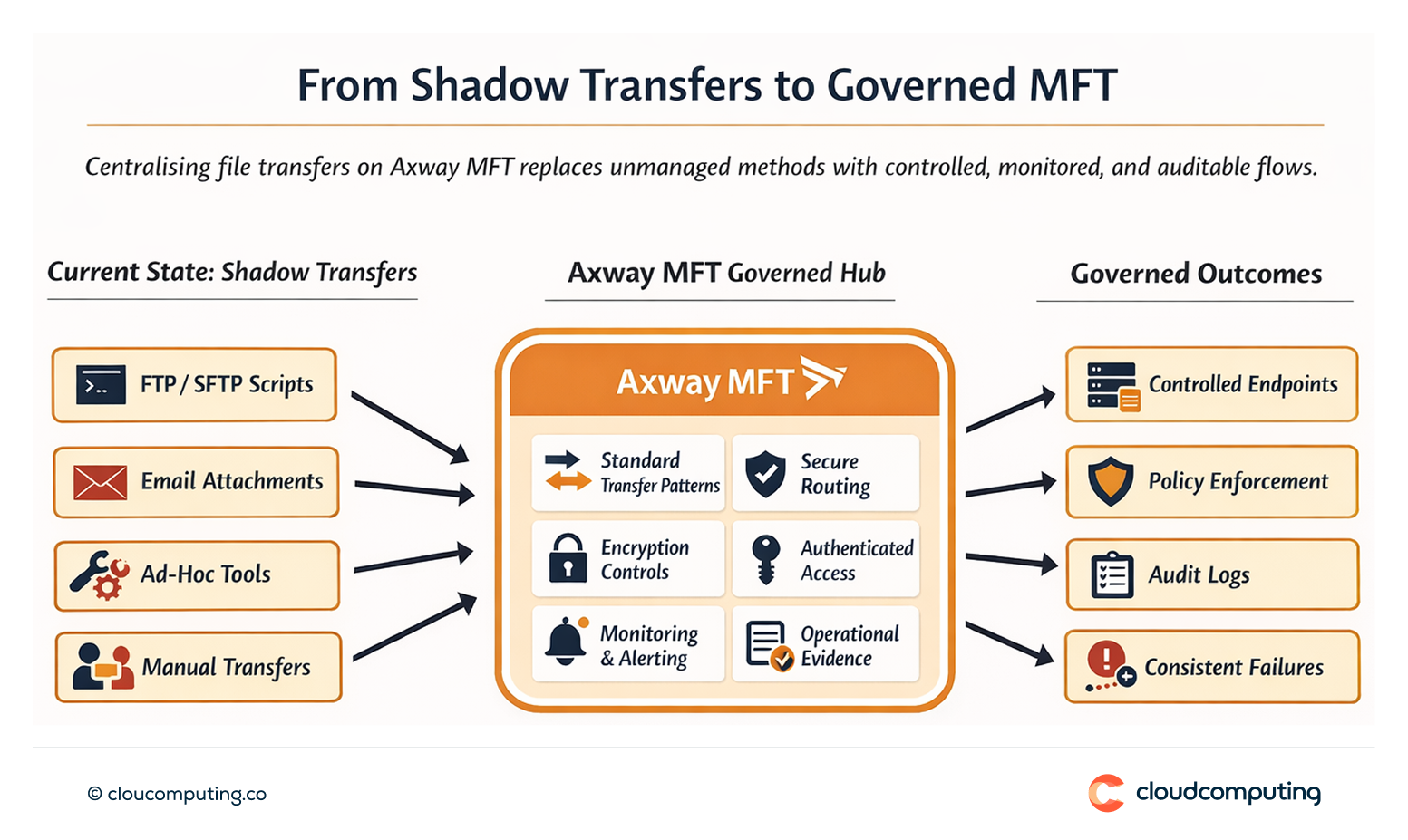
How we solve it: Centralise file transfers on Axway MFT using standard patterns, governance, and controlled endpoints.
We implement Axway MFT as the governed transfer layer, replacing unmanaged transfer methods with standardised flows, secure endpoints, and operational evidence.
- Transfer inventory and rationalisation
Identify existing scripts, gateways, and ad-hoc processes, then prioritise the highest-risk or highest-volume flows. - Standard transfer patterns
Define reusable templates for inbound/outbound transfers, naming conventions, encryption requirements, and routing rules. - Controlled endpoints and access governance
Consolidate endpoints, enforce authenticated access, and remove unmanaged transfer paths. - Operational handover and evidence
Establish monitoring, alerting, and reporting so transfers become supportable and auditable.
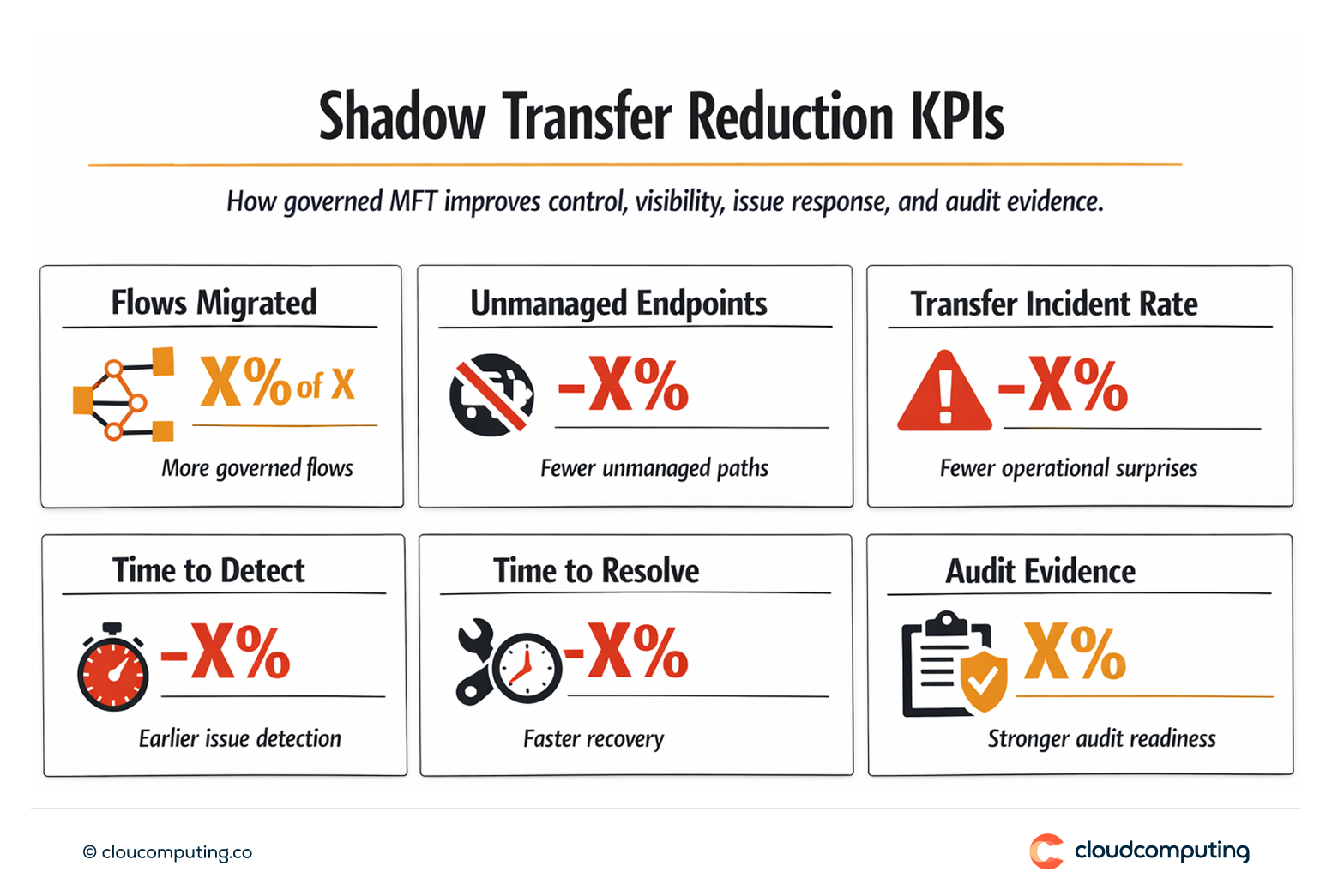
Expected outcome
- Reduced risk by eliminating unmanaged transfer methods and standardising controls
- Fewer operational surprises through monitoring and consistent failure handling
- Consistent security via governed endpoints and standard policies
- Improved audit readiness with traceability of transfers and controls
Quick Answers
What is “shadow IT” in file transfer?
Unmanaged transfer methods such as scripts, email, and ad-hoc tools that operate outside governance.
Why is it risky?
It creates weak traceability, inconsistent security, and hard-to-support operational dependencies.
What changes with Axway MFT?
Transfers become standardised, monitored, controlled, and auditable through a central platform.
