The Problem
Unmanaged remote privileged access puts critical systems at risk.
VPN access can expand network exposure, vendors may use unmanaged devices, and credentials are often shared informally.
Oversight is limited, and access frequently persists beyond contract terms.
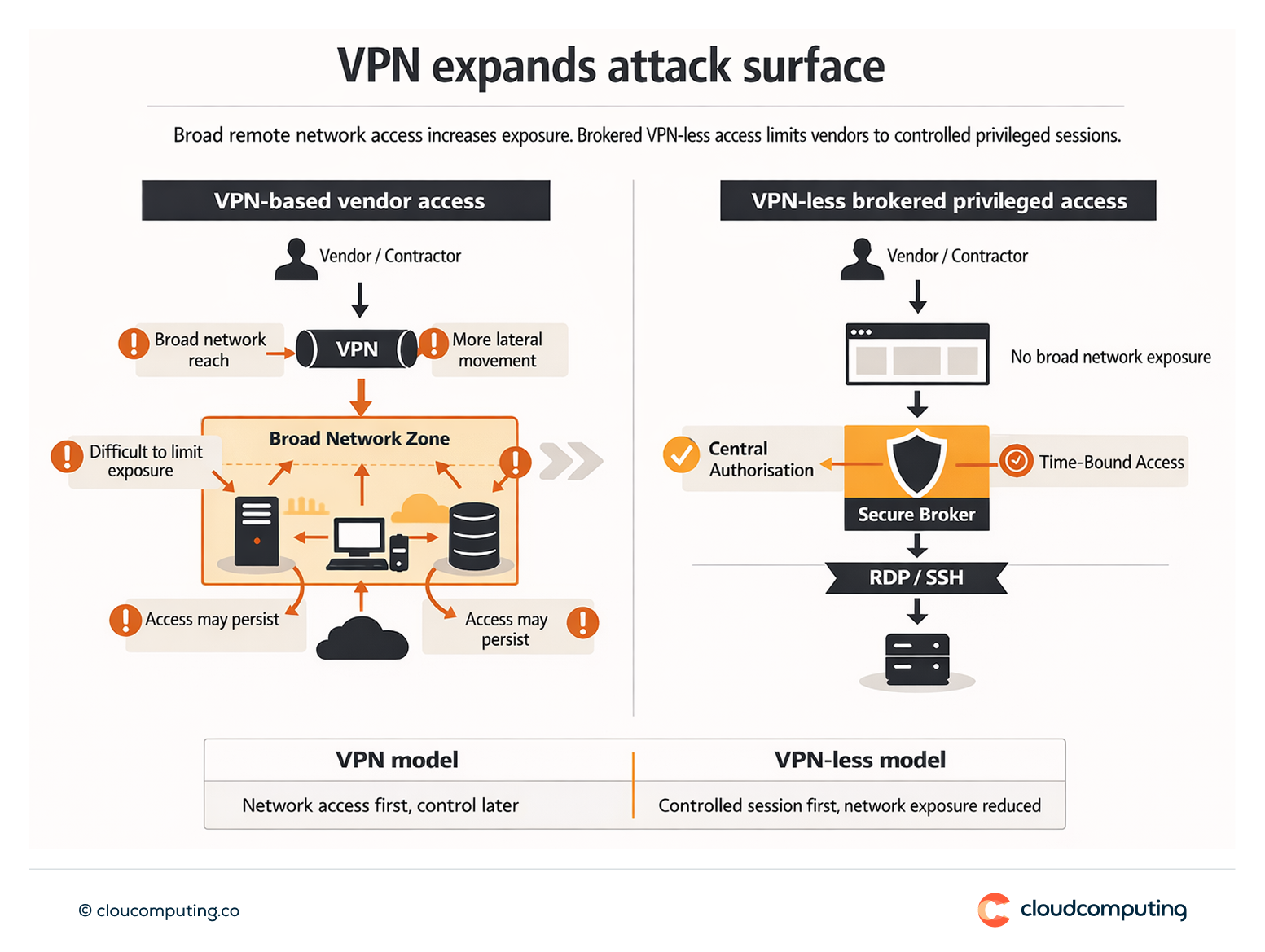
How we solve it: Use Delinea Privileged Remote Access for browser-based, VPN-less RDP/SSH with centralised authorisation and controls.
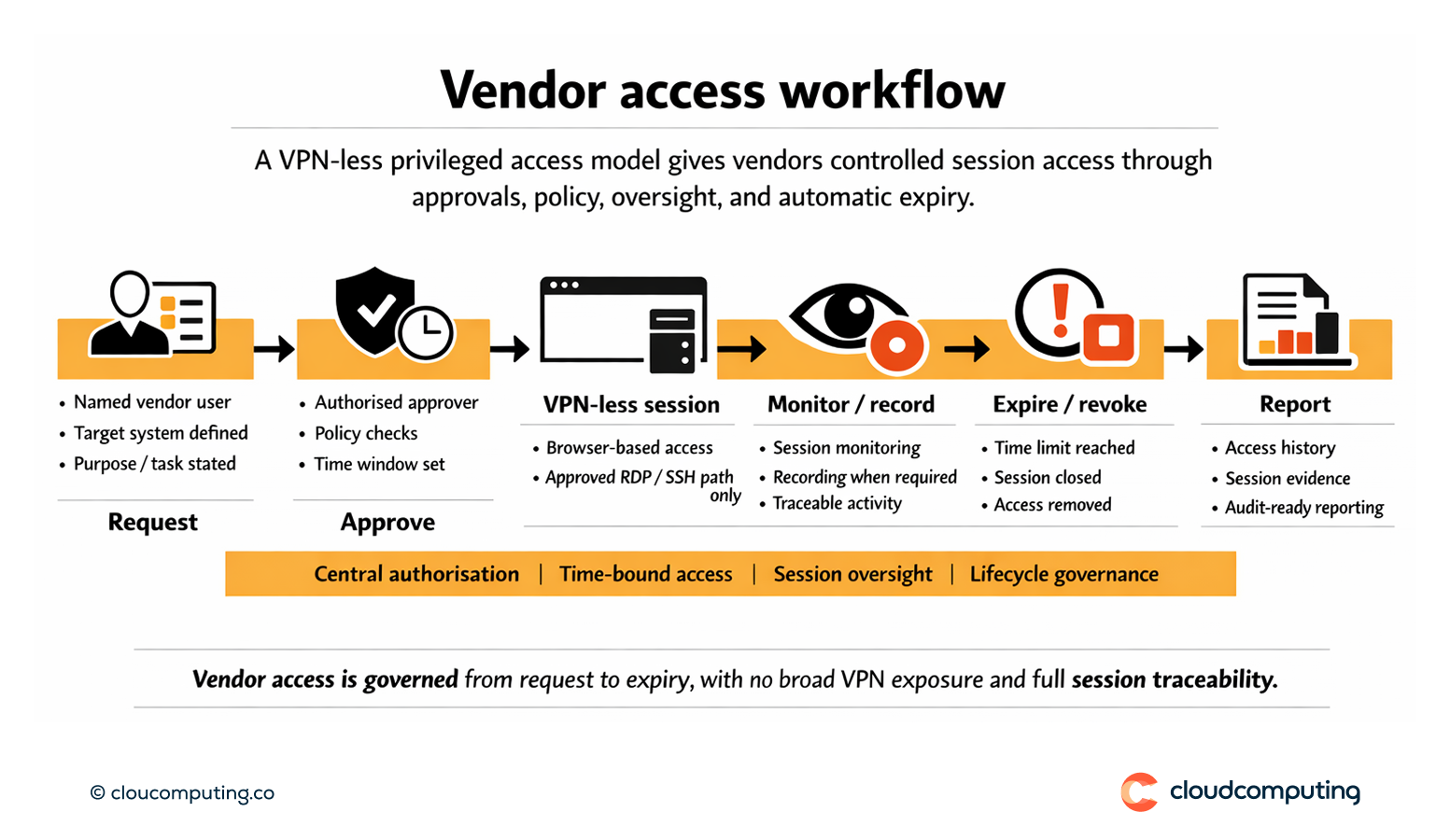
We implement a brokered remote access model that reduces network exposure and improves traceability for third-party privileged sessions.
- Brokered VPN-less access
Provide browser-based access paths that avoid broad network access. - Central authorisation and time bounds
Enforce who can access which systems, when, and under which conditions. - Session oversight
Apply monitoring and recording as required for accountability. - Lifecycle governance
Align vendor access to approvals, contract expiry, and offboarding.
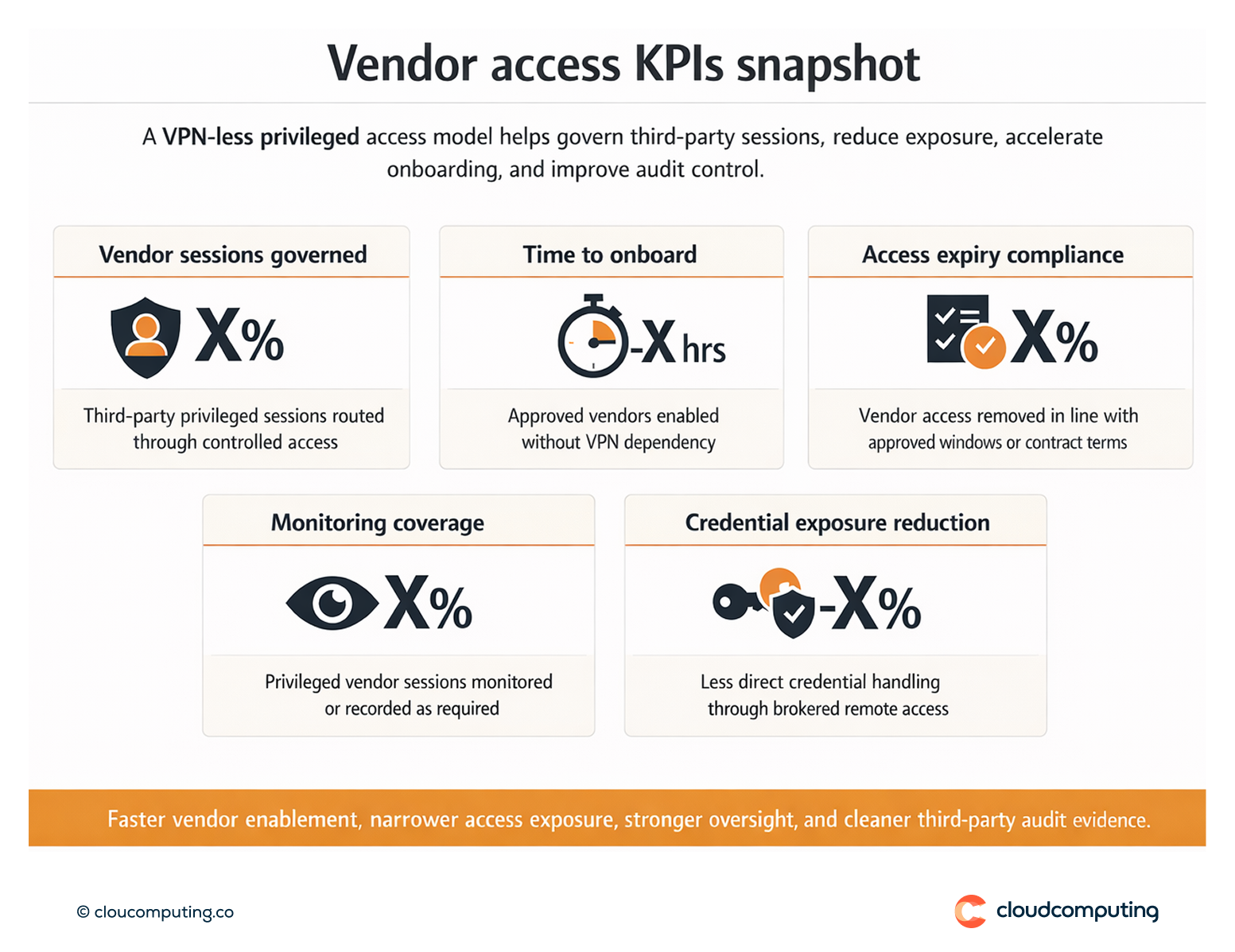
Expected outcome
- Faster third-party enablement without VPN dependency
- Tighter control with central authorisation and time-bound access
- Less credential exposure through brokered sessions and reduced direct access
- Improved audit readiness for third-party privileged activity
Quick Answers
What is VPN-less privileged access?
Brokered remote access that enables RDP/SSH via a controlled session layer without exposing the network via VPN.
Why is it safer for vendors?
It reduces network exposure and improves traceability and policy enforcement.
How do you enforce expiry?
Through time-bound access and lifecycle governance aligned to contract terms.
