The Problem
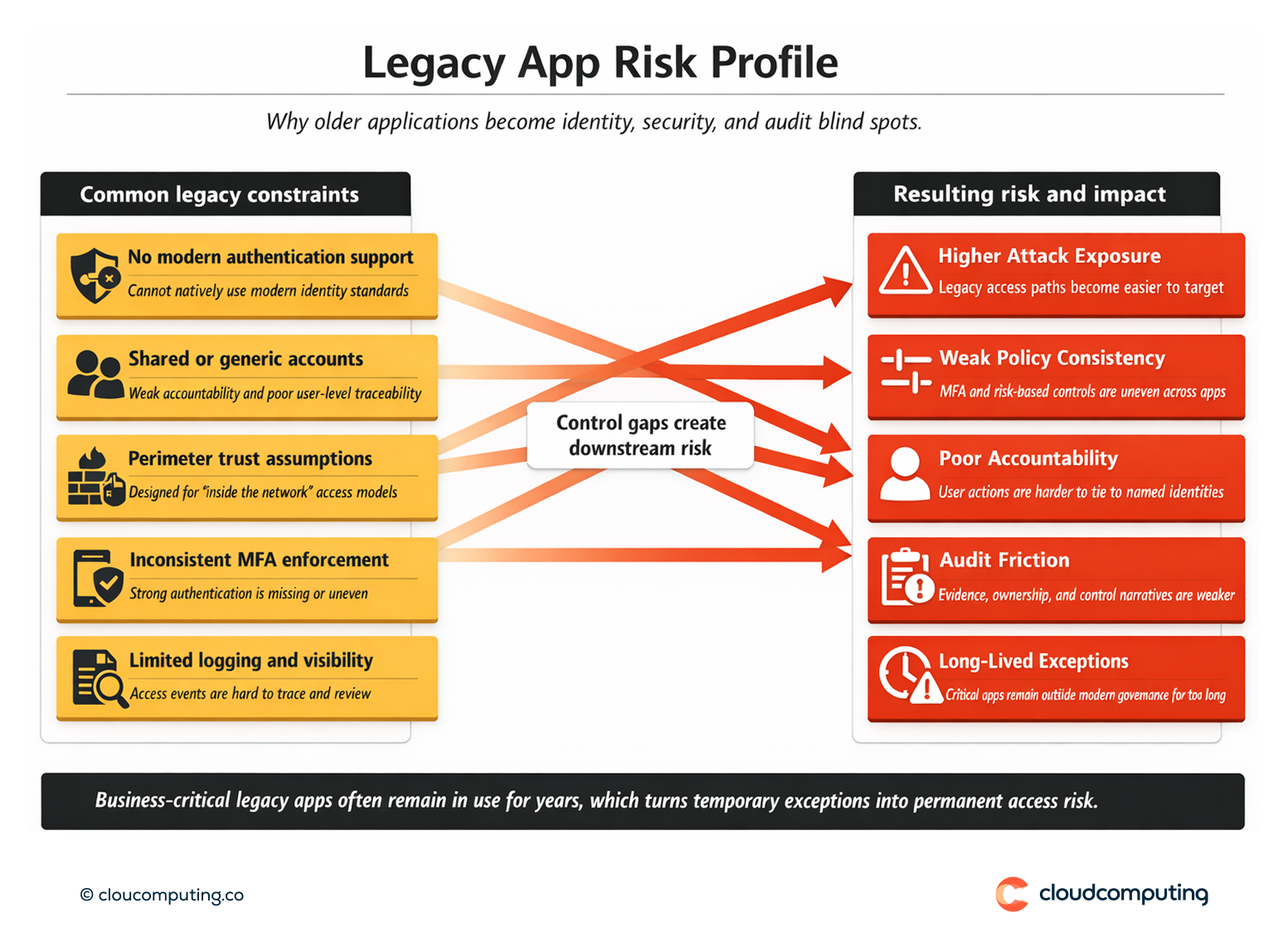
Legacy and on-prem applications often sit outside modern identity controls. Many do not support contemporary authentication standards, rely on older protocols, or assume the network perimeter is trustworthy.
As a result, security teams struggle to enforce consistent MFA, apply risk-based policies, or centralise access governance.
These applications are frequently business-critical, yet they are hard to modernise quickly – so they become long-lived exceptions that attackers target and auditors question.
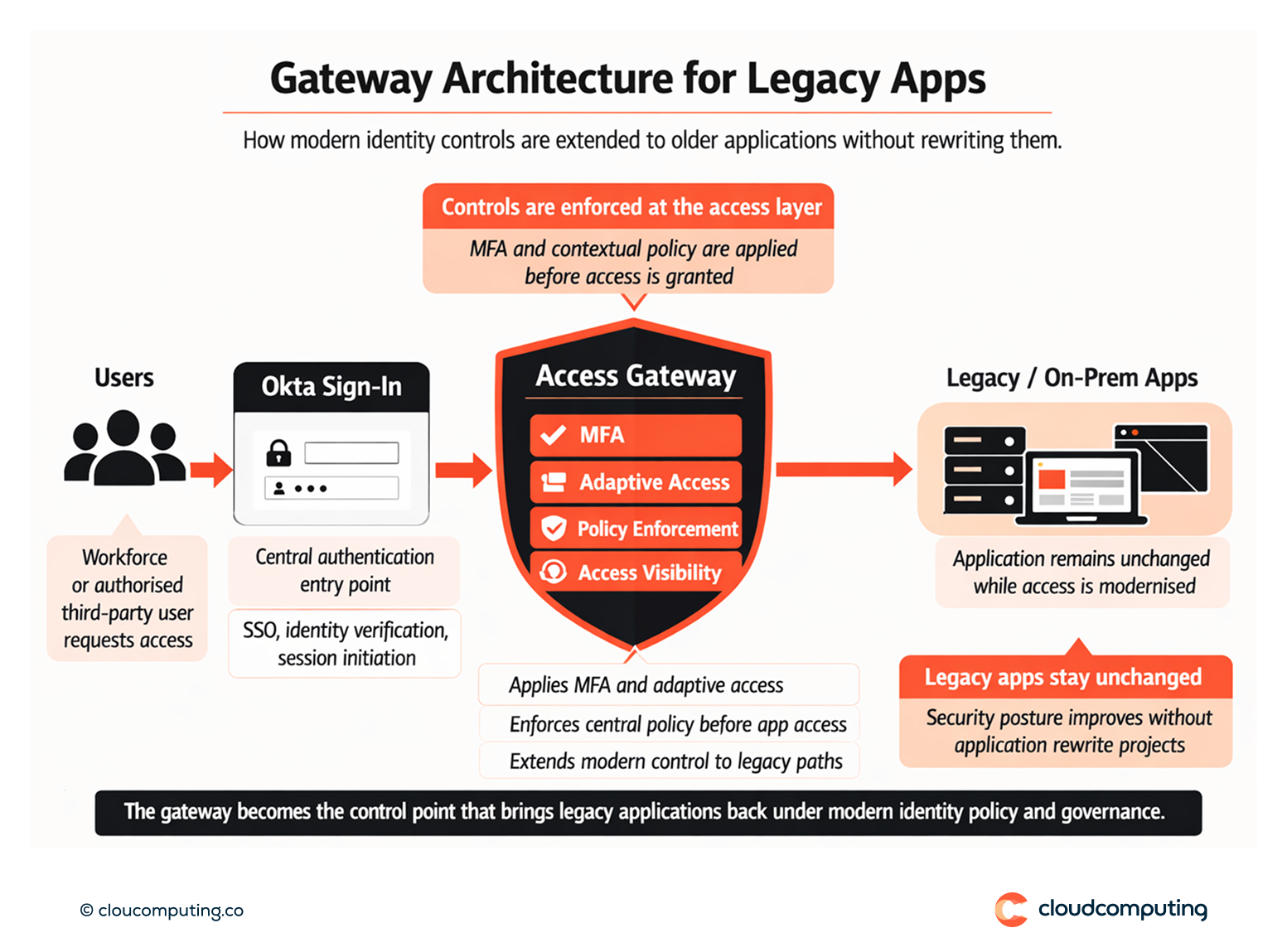
How we solve it: Extend modern access controls to legacy and on-prem apps using gateway patterns and centralised policy.
We integrate legacy applications into a modern access layer so users get consistent sign-in and security teams regain enforceable control—without forcing application rewrites.
- Application discovery and access-path mapping
We assess how each legacy app is accessed (web, thick client, remote access, internal network), then prioritise the apps that carry the highest risk and business impact. - Gateway patterns to modernise authentication
We use gateway approaches to front legacy apps with modern authentication, enabling centralised sign-in policies and consistent enforcement even when the app itself cannot be changed. - Consistent assurance controls
We apply MFA and adaptive access policies at the access layer, including step-up authentication for sensitive actions or risky contexts. - Access governance and visibility
We define ownership, access boundaries, and reporting so legacy apps are no longer blind spots in identity operations and compliance narratives. - Operational rollout with minimal disruption
We implement in controlled waves, validate user journeys, and align support processes to avoid business interruption during transition.
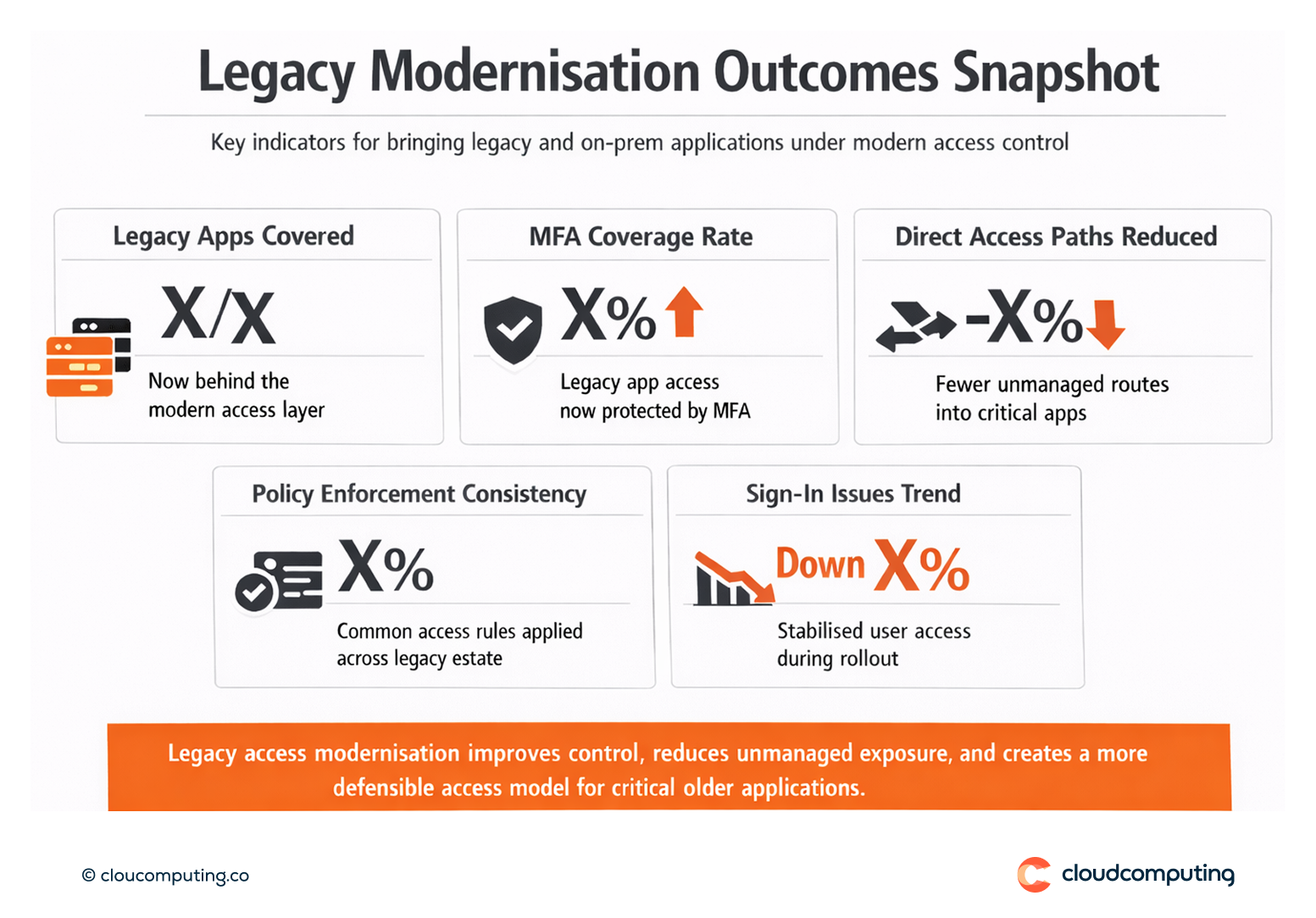
Expected outcome
- Modern sign-in experience for users across legacy and on-prem applications
- Stronger control through centralised MFA and policy enforcement at the access layer
- Reduced exception risk by bringing critical legacy apps under consistent governance
- Improved audit defensibility with clearer ownership, access boundaries, and traceable controls
Quick Answers
What is “secure access to legacy apps” without rewriting them?
It is applying modern identity controls through an access layer so legacy applications inherit consistent authentication and policy enforcement.
Why do legacy apps create identity risk?
They often lack modern authentication support, operate with weaker controls, and become long-term exceptions outside central governance.
What changes when a gateway pattern is used?
Authentication and policy enforcement move to a central layer, enabling consistent MFA and risk-based access while leaving the legacy app unchanged.
